Salesloft Drift Breach Extends to Other Connected Systems, Salesforce Sued
- Salesforce breach scope: Google clarified the compromise is not limited to the Salesforce integration and may impact other Drift-connected platforms
- Google warns: All authentication tokens stored in or connected to the Drift platform are potentially compromised.
- Salesforce sued: Meanwhile, a class-action lawsuit alleges a March 2025 breach exposed the data of Farmers Group customers.
The Salesloft Drift compromise extends beyond Salesforce integrations, affecting other connected systems, according to recent updates from Google Threat Intelligence Group (GTIG). Attackers were active from August 8 to at least August 18, 2025, using stolen OAuth tokens to search for and exfiltrate corporate credentials.
Scope of Salesforce Breach
An August 28 update to Google’s report says that OAuth tokens for the "Drift Email" integration were confirmed compromised, with a threat actor accessing “a small number of Google Workspace accounts” configured with Salesloft on August 9, 2025.
“The scope of this compromise is not exclusive to the Salesforce integration with Salesloft Drift and impacts other integrations,” says the Google report, advising all Salesloft Drift customers to “treat any and all authentication tokens stored in or connected to the Drift platform as potentially compromised.” Mandiant is now assisting Salesforce in its investigation.
Potentially accessed accounts involve those specifically configured to integrate with Salesloft, the report stated, adding that other accounts on a customer's Workspace domain were not accessed.
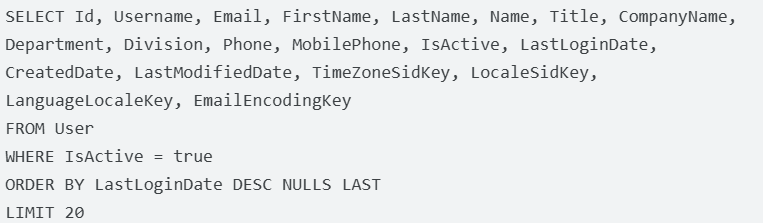
The UNC6395 threat actor specifically targeted Amazon Web Services (AWS) access keys (AKIA identifiers), Snowflake-related access tokens, and login URL strings. The report mentions hackers ran queries to get Salesforce objects-associated data, such as:
- Cases,
- Accounts,
- Users,
- Opportunities.
Google's Threat Intelligence team identified this incident as activity by the UNC6395 threat actor. The breach was also claimed by ShinyHunters ransomware. In June, Google reported that ShinyHunters targeted Salesforce via phishing.
The recent wave of Salesforce-related breaches has been attributed to Scattered Spider (UNC3944) and ShinyHunters (UNC6040), according to Google.
Salesforce Lawsuit
Salesforce Inc. was recently named in a class-action lawsuit in federal court for an alleged March 2025 breach that would have impacted the sensitive details of more than 1.1 million customers of the insurer Farmers Group Inc., according to Bloomberg News.
The complaint alleges violations of data protection and consumer privacy laws. The compromised data reportedly included names, addresses, dates of birth, driver’s license numbers, and possibly the last four digits of Social Security numbers.
The plaintiff, Malcolm Scott, claims Salesforce’s servers were breached via compromised customer access tokens or phishing, described as a "hub-and-spoke" intrusion, where Salesforce serves as the central hub, which may signify the number of affected users could be higher.
Protective Measures
Google has revoked affected OAuth tokens granted to the Drift Email application, disabled the Workspace and Drift integration, and is notifying impacted administrators. The report says Google Workspace and Alphabet systems remain secure.
Organizations are urged to review Drift integrations, rotate credentials, and investigate for unauthorized access.
“Organizations should view third-party applications, vendor tools, and CRM systems as integral extension points of their own attack surface," said Darren Guccione, CEO and Co-Founder at Keeper Security. "They should restrict access to what is necessary, and implement Privileged Access Management (PAM), zero-trust architectures, and zero-knowledge approaches to limit exposure.”
Related Incidents
These attacks appear linked to a broader campaign targeting Salesforce-connected systems, leveraging social engineering via voice phishing (vishing) and malicious connected app authorization—especially trojanized versions of Salesforce’s Data Loader tool.
Other high-profile companies that have been recently impacted by Salesforce data breaches include Google, Chanel, Cisco, Air France-KLM Group, Adidas, Qantas Airlines, Louis Vuitton, Dior, Tiffany & Co., and reportedly TransUnion.
In April, Google was spoofed via a DKIM replay attack and the exploit of an OAuth infrastructure flaw. In February, a sophisticated phishing scam targeted Workspace users.