The Ryuk Ransomware Gang Crippled Spain’s Public Payments Agency
- SEPE has been hit by the Ryuk ransomware group, and many of its systems remain unavailable.
- The agency will have to adjust deadlines and payment dates but assures the public that no data was stolen.
- The infiltrators may have used one of Ryuk’s recent variants, which feature worm-like capabilities.
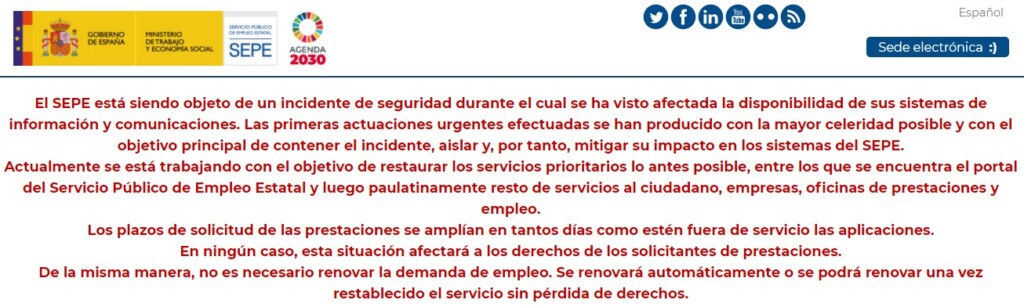
The Servicio Público de Empleo Estatal (SEPE) website is displaying a worrying message, informing the public that they have suffered a security incident and are currently in the effort to contain the attack and isolate it. As a result, there’s an impact on the systems, which means the public employment service and all payments to services, citizens, companies, and beneficiaries may have to be postponed for a while.
The message assures people that the application deadlines for benefits will be extended by as many days as the services remain down, so applicants don’t have to worry about it. That is, of course, unless you needed any money in the middle of the ongoing pandemic.
As for those looking to renew their demand for employment, the platform has promised that everyone eligible for that will have their demands automatically renewed once the service is restored without losing their rights.
The director of SEPE, Gerardo Guitérrez, has pointed the finger at the Ryuk gang, who are allegedly responsible for this situation. He added that nothing would be affected, only delayed, and gave his assurances about confidential data remaining safe and out of the actors’ reach. Also, the payroll generation system hasn’t been affected, so unemployment benefits should reach their beneficiaries as normal.
Separate sources claim that the ransomware has managed to spread vertically and laterally, essentially locking down 710 state offices, all telematics systems, and even affecting the laptops of the agency’s remote working staff. Others report that the attack started with the exploitation of an unpatched networking device, which helped the actors establish their foothold onto the agency’s internal network.
Recently, we covered an ANSSI analysis about Ryuk’s new worming capabilities that allow it to spread rapidly to connected devices, leaving little margin for IT teams to respond. The scale of the SEPE infection and the speed with which it appears to have happened may be explained by the deployment of one of Ryuk’s latest variants.
For the Ryuk group, having done all of the above and not exfiltrating any data, it would be extremely unlikely. The only way we see this happening is if employee details and other sensitive data were stored elsewhere, on a separate network. For a state agency taking such steps in cybersecurity, it would be a rare finding.