RondoDox Botnet, a Stealth Malware Targeting Surveillance Systems with VPN and Gaming Traffic Camouflage
- An emerging infrastructure threat, the RondoDox botnet, has been uncovered by researchers
- It cloaks malicious traffic as VPN or gaming data, renames critical system binaries, and kills analysis tools
- The botnet targets embedded Linux systems, particularly TBK DVRs and Four-Faith routers, used in surveillance
A new botnet, RondoDox, is posing a threat to enterprise-grade network and surveillance systems. It operates stealthily and specifically targets embedded Linux-based devices exposed to the internet across enterprise, industrial, and municipal networks.
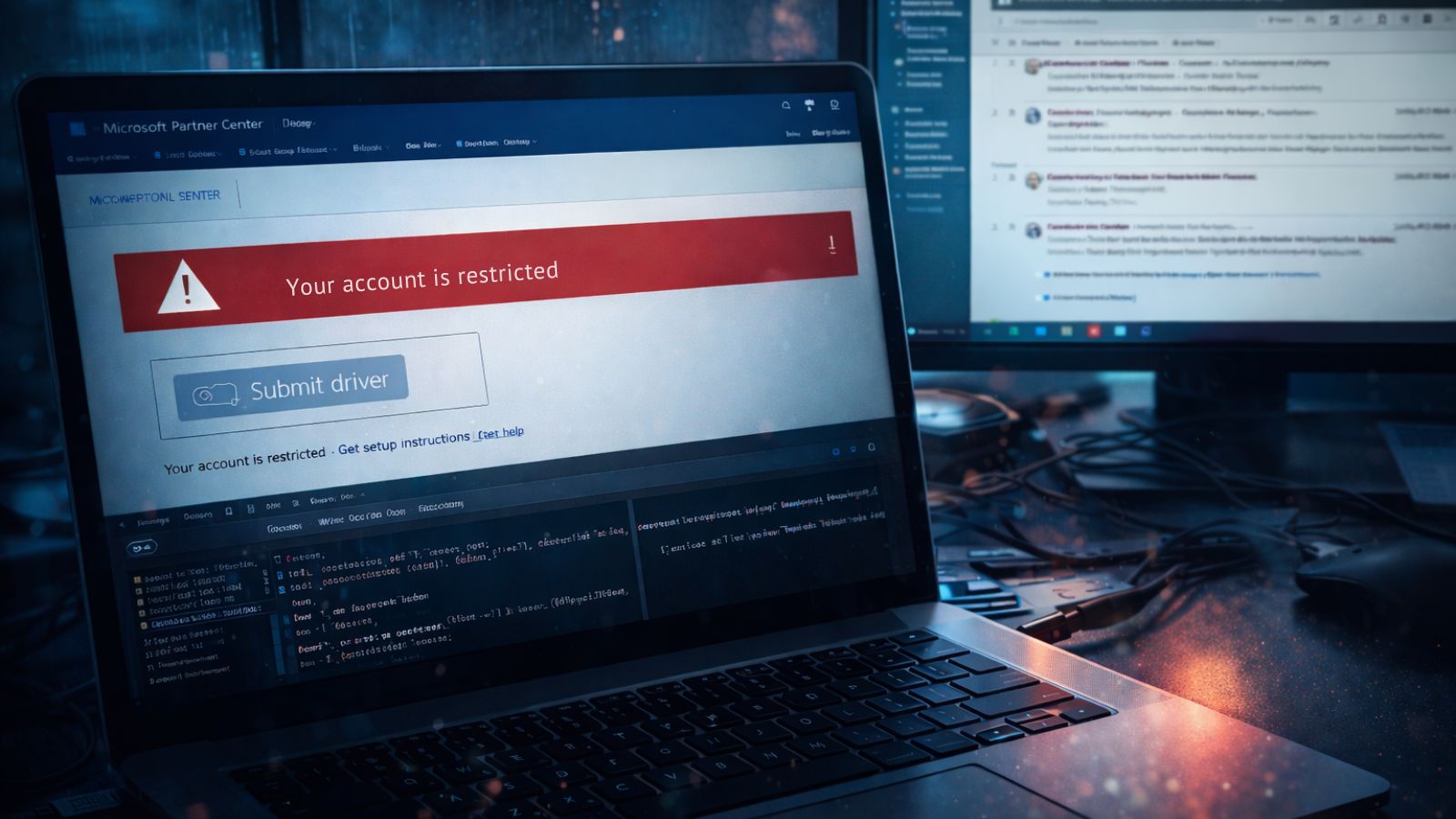
Uncovered by FortiGuard Labs, RondoDox has been linked to increased scanning activity and active exploitation of two high-risk vulnerabilities: CVE-2024-3721 and CVE-2024-12856. These flaws allow remote attackers to execute arbitrary commands on affected systems.
Presently considered a low-profile threat, RondoDox is being used to launch distributed denial-of-service (DDoS) attacks. To evade detection, it cloaks malicious traffic to resemble that of popular gaming platforms such as Minecraft, GTA, Roblox, and Fortnite, as well as VPN services including OpenVPN, WireGuard, and RakNet.
This enables it to blend into normal network activity and bypass firewalls or monitoring systems that rely on protocol signatures.
Capabilities of RondoDox botnet:
- Traffic cloaking: Disguises attack traffic as VPN or gaming data to evade detection
- Persistence: Survives reboots using layered init scripts, crontabs, and startup entries
- C2 Control: Communicates with a command-and-control server at 83[.]150[.]218[.]93
- Targets: Internet-connected devices used in surveillance and industrial communications:
- Exploits the vulnerability CVE-2024-3721 in TBK DVRs
- Exploits the vulnerability CVE-2024-12856 in Four-Faith Routers
These devices are frequently deployed in critical infrastructure sectors such as energy, water, transportation, and telecommunications. The affected routers and DVRs process sensitive data and serve as communication bridges between field sites and centralized control systems. Their compromise could lead to downtime, data exfiltration, and widespread operational disruption.
As of Fortinet’s July 3, 2025 research, there are no public indicators of specific victims, industries, or geographic targets.
However, given its focus on infrastructure-grade devices and its ability to disguise traffic as trusted services, RondoDox may represent the work of a nation-state-level adversary. The malware could be designed to infiltrate networks in regions aligned with conflicting interests in global hot zones such as Ukraine–Russia or Israel–Iran.
To evade detection, RondoDox employs multiple layers of stealth. It manipulates file permissions and renames critical system binaries such as iptables, ufw, and passwd to random character strings, effectively disabling firewall controls and user management tools. This tactic hinders incident response and complicates remediation.
The botnet also includes anti-debugging logic, terminating processes commonly used by analysts and defenders, including Wireshark, gdb, top, and others. To ensure long-term persistence, it leverages init scripts, crontabs, and multiple startup files, making it resilient against basic cleanup efforts.
Additionally, RondoDox obfuscates its configuration and command-and-control (C2) address using XOR encoding, further complicating static analysis and reverse engineering.
To remediate RondoDox infections or prevent stealthy compromise, organizations could deploy file integrity monitoring, harden Linux filesystem permissions, implement EDR tools with behavior-based alerts, and segment network access.
Maintain clean system images and restrict protocol usage from embedded devices, as both are critical steps, especially given how RondoDox tampers with binaries and evades traditional defenses.
Organizations should also urgently update the firmware on affected devices. If patches are not yet available from the vendors, administrators should restrict remote access to these devices and monitor them for suspicious behavior.