The Romanian Police Arrested a Group of Aspirant Ransomware Actors
- A group of website defacing actors decided to engage in ransomware operations and bought two old strains to do it.
- Since they weren’t hiding their online tracks adequately, the police were quick to locate and arrest them.
- The actors were planning to launch attacks against Romanian hospitals and healthcare centers.
The Romanian “Directorate for Investigating Organized Crime and Terrorism” (DIICOT) has announced the dismantling of a ransomware group using the name “PentaGuard.” Three individuals were arrested in Romania, while a fourth actor was located in the Republic of Moldova. All four were raided in their homes after the police secured home search warrants. According to the announcement, the malicious crew was preparing to hit hospitals and healthcare organizations in the country by sending emails impersonating government institutions that would include a file supposedly containing information regarding the threat of the ongoing COVID-19 pandemic. Thankfully, these plans didn’t come into fruition, as the bust came right in time to prevent them.
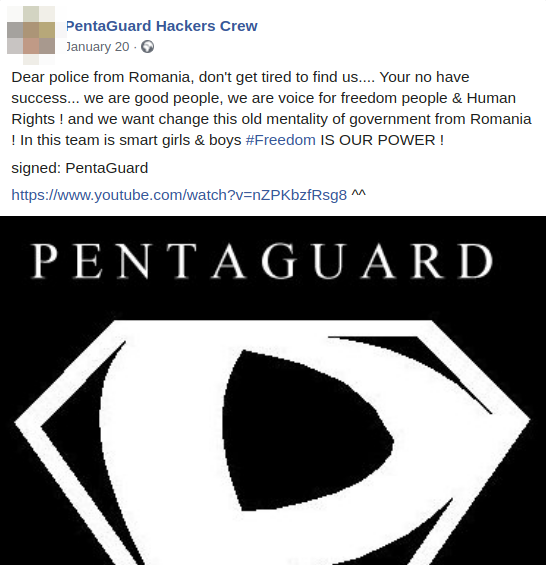
The DIICOT says the group was buying RATs (remote access tools) and various kinds of malware to use in ransomware attacks. Moreover, they used “SQL Injection” as a method to carry out their attacks. Website defacement on governmental or banking portals in Moldova and Romania was also a common thing for the PentaGuard. As it seems, the crew liked to taunt the law enforcement authorities with these defacement acts, bragging about their intelligence and how the police shouldn’t even try to find them.
Source: Bleeping Computer
In fact, PentaGuard formed a long time ago, possibly even before 2000, but website defacement was their main thing for almost two decades now. The group thought of launching ransomware attacks and making some money out of their online activity very recently, so they bought the first samples of the “Locky” and “Bad Rabbit” ransomware strains to do it. Locky was eventually unlocked in January 2019, while the activity that concerned “Bad Rabbit” culminated in 2017 when the strain wreaked havoc in Eastern European countries. Apparently, PentaGuard would go for using older strains, but that wasn’t their worst mistake. Their biggest error according to the DIICOT was that they weren’t careful enough in terms of hiding their online tracks.
As it seems, PentaGuard falsely thought that they were untraceable and invincible, but in reality, the police just didn’t bother to go after them for the defacements they have been doing all these years. As soon as the group turned to ransomware, and before they even got the chance to launch their first attack, the police knocked on their door. Finally, it is important to point out that the group has claimed that they were against the imposition of lock-down and freedom-defiling measures, which may be why they decided to take things to the next level. However, targeting hospitals and healthcare centers is absolutely unacceptable, especially at these times.