REvil Struck Laptop-Maker Acer and Demands $50 Million in Ransom
- Acer has suffered a ransomware attack by REvil, who are asking for a humongous ransom payment.
- The computer maker has decided not to go into details and just skipped media requests through generic statements.
- The notorious ransomware group may have managed to weaponize the Exchange flaws.
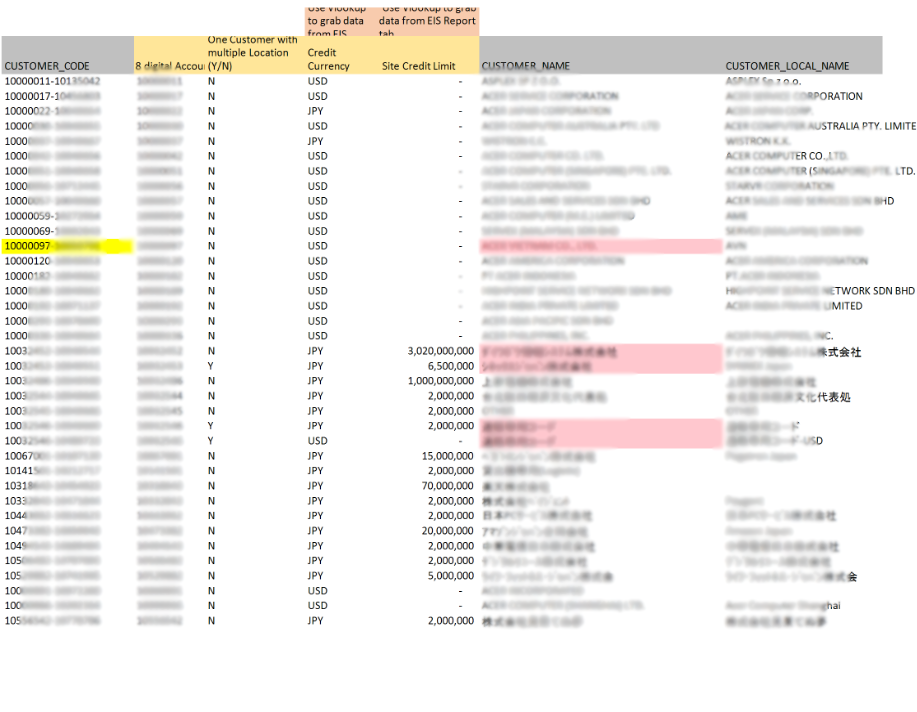
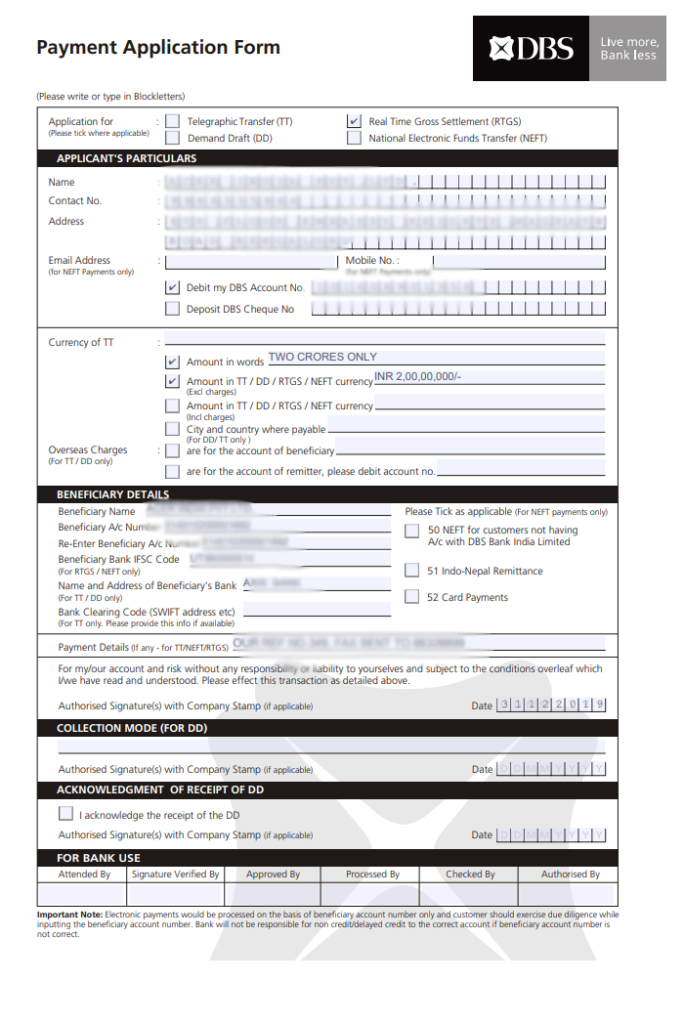
Acer, the Taiwanese laptop maker with annual revenue of over 8 billion USD, has been hit by the REvil ransomware gang, who are now demanding a record-breaking amount of $50,000,000 to be paid in Monero. The actors have started leaking out images of the stolen data indicating that they got to exfiltrate financial documents, communications with banks, spreadsheets, etc. However, these are only the first samples to be disclosed, so there must be a lot more in the hands of REvil.
With the help of KELA’s cyber-intelligence tools, we located the new leak site, and we got to access the documents that are used for the extortion. We have blurred the following for you to get an idea of what has been stolen from Acer’s computers.
The computer maker has confirmed that they have launched an investigation on the incident but stated that they would rather not comment on anything at the moment. They instead shared a generic statement with BleepingComputer, saying that they routinely have to deal with cyber-attacks. When things are “abnormal,” they report it to law enforcement and data protection authorities in multiple countries.
It appears that Acer’s business, production, websites, and online services haven’t been affected by this attack, so the company can choose to downplay the incident, but the data-stealing aspect that may cause them significant harm soon remains a problem no doubt.
As it seems to be the case, the attack occurred on March 14, 2021, so Acer has until March 28, 2021, until the deadline is reached. After that, the ransom amount will be doubled to $100 million, and the data leaks will intensify.
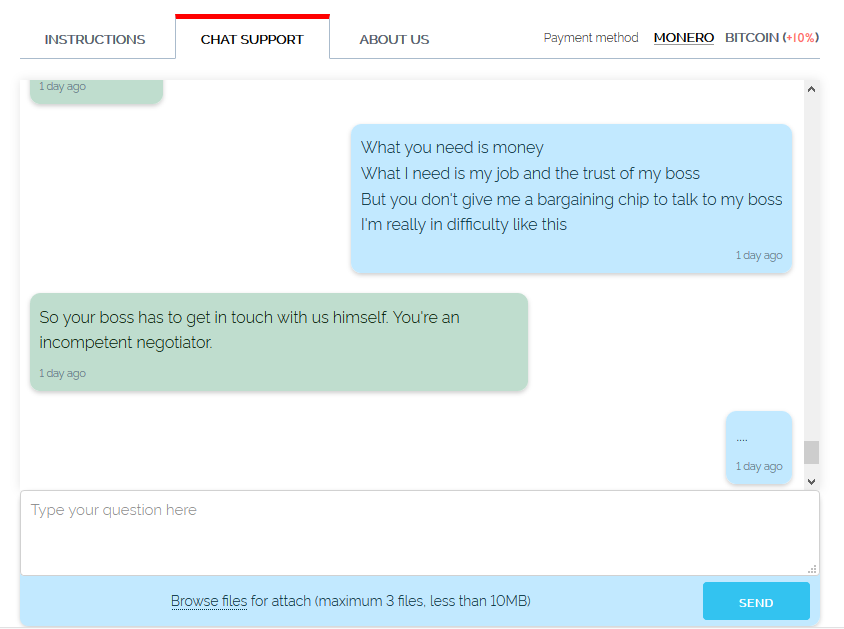
Samples of conversations between the Acer representative and the REvil agent have also been leaked from the actors’ side, showing that Acer’s side was shocked by the ransom amount. The negotiations seem to have reached a dead-end for now.
An interesting question is what the REvil actors could have exploited to breach Acer, and the currently hot Exchange flaws cannot be excluded. The types of files that are presented in the hackers’ leak site are compatible with this assumption.
In fact, researcher Vitali Kremez of "Advanced Intel" stated that their detectors have “caught” at least one REvil affiliate pursuing the weaponization of Exchange flaws. If that’s the case, this is going to be just the first of a series of high-profile attacks launched in a similar way.