PrankDial.com Exposes 138 Million Records via Unprotected Database
- PrankDial.com was all jokes and fun until a user data spilling database appeared online.
- People have had their IP addresses, emails, password reset tokens, and log records exposed.
- The company hasn’t responded to the incident and is probably not planning to circulate notices.
Prank calling service “PrankDial.com” has exposed 138 million log records after they have left a non-password protected database online for anyone to access. The discovery was made in October by Jeremiah Fowler of “Security Discovery”, who reported the incident to the company immediately. The platform secured the database on the same day, but the exposure could have led to the stealing of the sensitive data in the meantime. The researcher never received an official response from them or any form of acknowledgment.
PrankDial is a service that has been used for over 300 million prank calls to unsuspecting victims. Users can choose from a galore of prank call scenarios like “You Kick My Dog” or “Why Do You Call My Girlfriend”, and send them to a number of their choice. The first three calls are provided for free, and anything in addition to this requires the purchase of tokens. The victims are recorded so that the user gets to hear their reaction and laugh with it. Then, the user can even share these reactions with others, and the other users can then rate or comment on them.
Source: prankdial.com
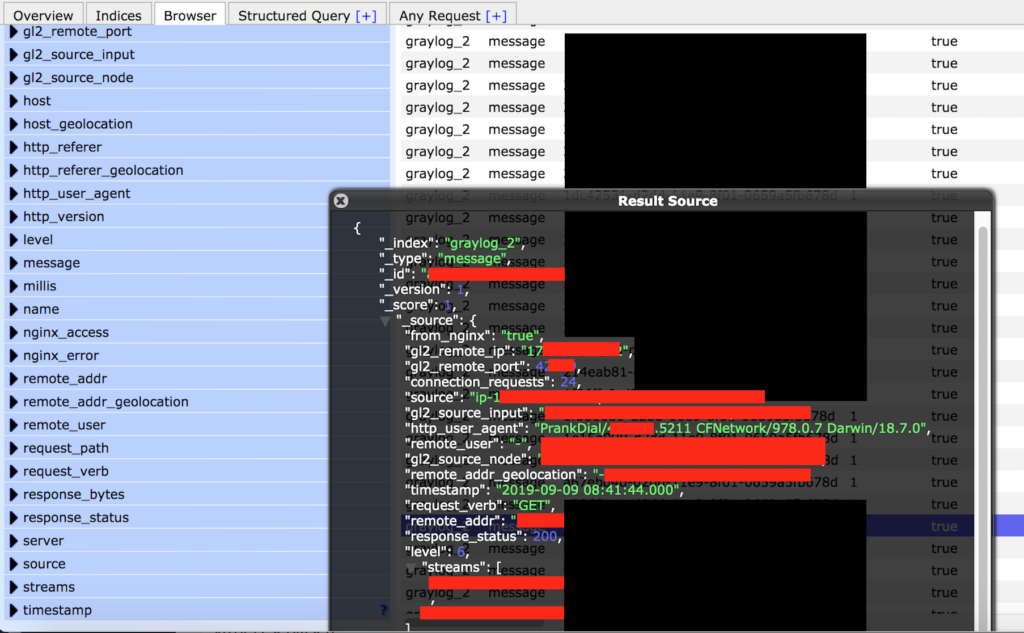
The owner of PrankDial also operates several other similar platforms, but thankfully, the particular database only contained information that links to this service. The data that was exposed includes the following:
- 138 million log records
- User emails, credentials and password reset tokens, user IP addresses exposed in the logs.
- Device, operating system, and version info.
- Internal IP addresses, Ports, Pathways, and storage info that cybercriminals could exploit to access deeper into the network.
Source: Security Discovery
The fact that the prank call platform hasn’t replied to J. Fowler is indicative of their intention to bury the incident. They are unlikely to send notices to the affected individuals, so most of the users will never get to know about what happened. Given the fact that people had their email addresses, and IP addresses exposed, they are now at risk of getting phished or scammed. At least the details about phone numbers are missing from the database, so one scamming channel is crossed out.
Help us spread the word by sharing this post through our socials, on Facebook and Twitter, and don’t hesitate to comment on the dedicated section below.