Popular iOS & Android Dating Apps Plagued by Security and Privacy Flaws
- After testing 14 of the most popular dating apps on Android and iOS, most of them are found to be insecure.
- In most cases, the apps don’t follow the proper user data privacy protection practices, which might lead to data leaks.
- Users should be very careful regarding the apps they are using and the data they share with these platforms.
Zimperium, a mobile security solutions provider, has shared a report with us where they present their worrisome findings regarding the security and privacy of 14 widely-used dating apps. The set of the tested apps are available both for Android and iOS, and they were evaluated based on a pre-determined scoring system via Zimperium’s Advanced Applications Analysis engine (3A). This means that the researchers have investigated the apps’ code, behavior, certificates, connected domains, data collection and retention policies, and the requested permissions upon installation.
The scoring of the apps is divided into three categories named - "passing", "average", and "failing". "Passing" means that the app comes with very few risks if any at all. "Average" means that the app has some risks that should be addressed, but it does take some steps to protect user data. A "failing" grade means that using the app involves significant risks.
Here are the most notable findings of the report from the "Privacy Risks" category:
- 100% of the tested iOS dating apps and 71% of their Android counterparts have failed to receive a passing score.
- Among the iOS apps, there are cases of user PII retention and sensitive information logging.
- 11 out of the 14 iOS apps are actively monitoring data retrieving from the Pasteboard.
- 12 out of the 14 Android apps use an insecure content provider.
Source: Zimperium
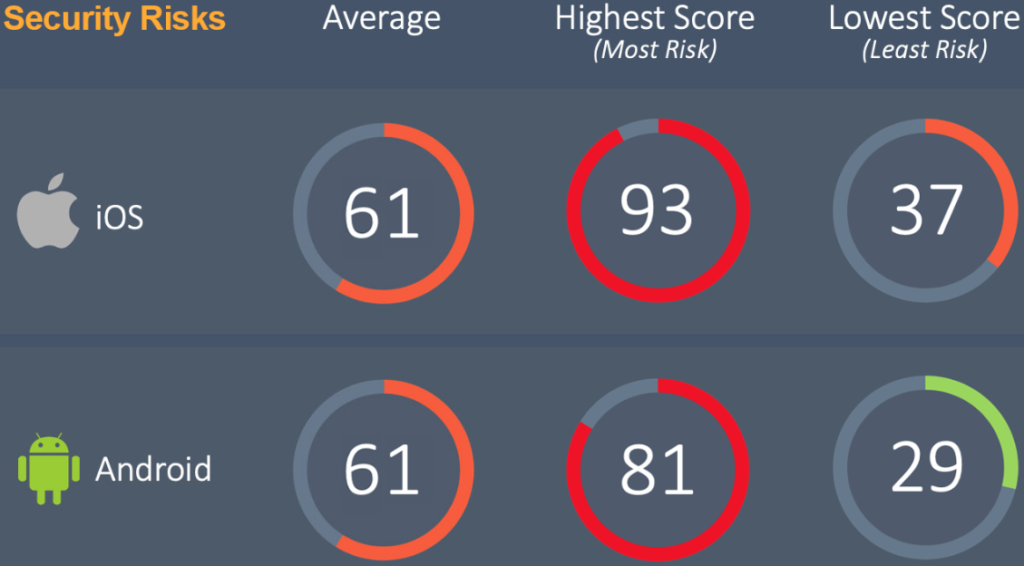
The following stats refer to the report’s key findings regarding "Security Risks":
- 100% of iOS-based apps and 93% of Android-based apps failed to receive a passing security grade.
- All 14 of iOS apps tested are susceptible to SSL and TLS chain validation override. Moreover, they all implement Swizzling API calls.
- 6 out of the 14 iOS apps allow insecure connections to servers with lower TLS versions.
- 9 out of the 14 Android apps enable WebView to execute JavaScript code, potentially leading to arbitrary code execution.
- Half of the Android apps tested allow the creation of new OS subprocesses, and provide methods of injecting Java objects from JavaScript.
- 29% of Android apps use WebKit to download additional files from the internet.
Source: Zimperium
As it becomes clear from the above data, using mobile dating apps involves severe risks for the users involved. User data privacy is a very important matter, and when it comes to dating apps, this data is a lot more sensitive so it should be handled with even greater care.
Unfortunately, we see that this is not the case for the majority of developers of these apps. Zimperium hasn’t mentioned any application names in their report as they prefer to work with the vendors to help them make their software more secure. For now, if you’re using a dating app, our advice is to be extra-vigilant.