Eight Popular Airlines Found to Expose Your Personal Data via E-Ticketing Systems
- Eight airlines were found to be following insecure check-in process practices, allowing third-parties to access your personal data.
- The implications include passenger information leaks and perturbation of the flight booking details.
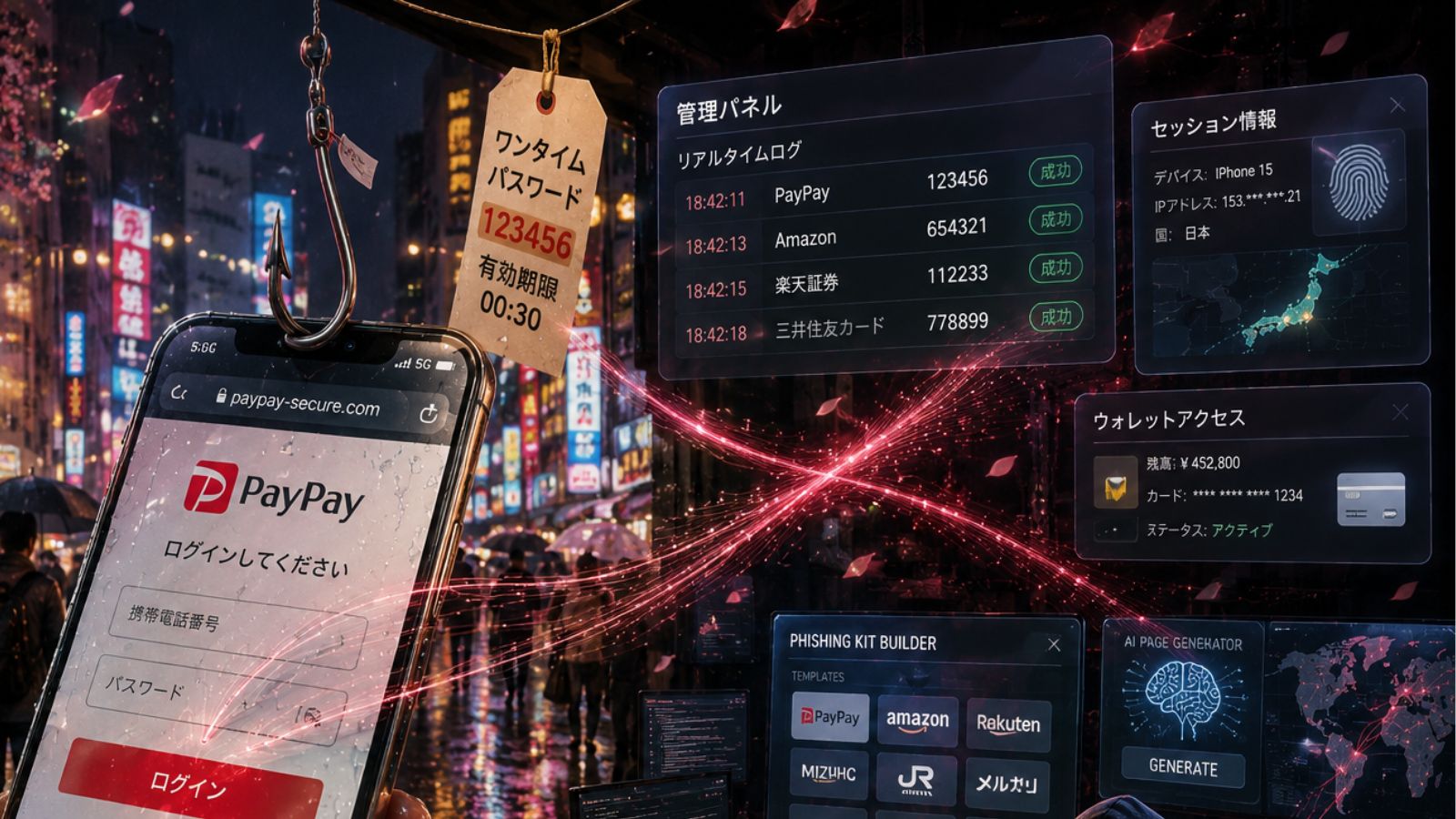
- The vulnerability is based on a series of insecure steps including unencrypted links and automatic passenger login.
According to a Wandera research report, at least eight high-profile airlines follow the practice of sending unencrypted check-in links to their customers, risking their interception by hackers. The airlines that were identified as risky by the researchers include Southwest, Air France, KLM, and Transavia, Vueling, Jetstar, Air Europa, and Thomas Cook. Due to this insecure data transaction, 3rd parties can gain access to personally identifiable information of passengers, their flight booking details, and their boarding passes, while in many cases, changing these details is also possible.
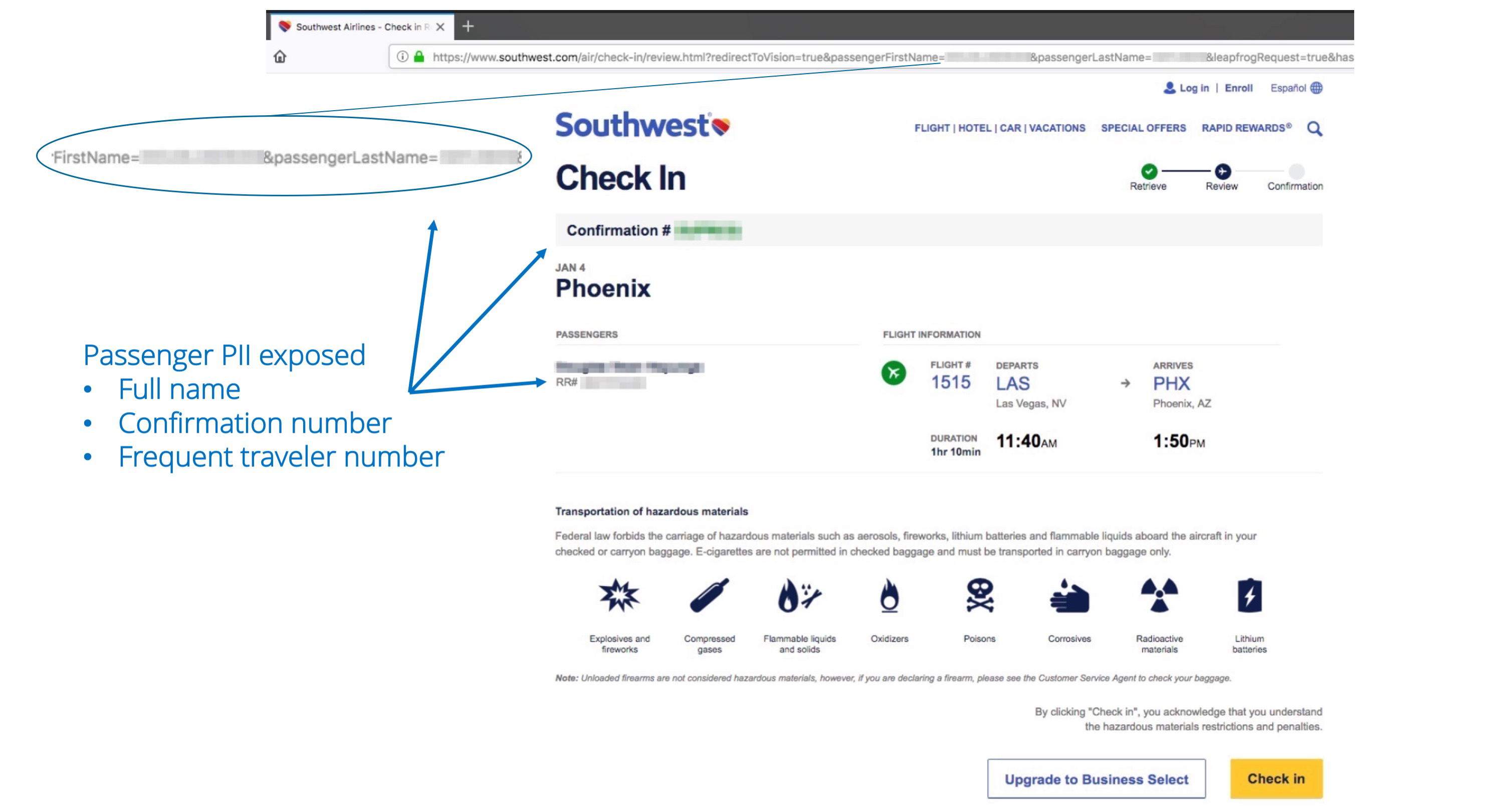
Online check-in is a standard process that requires the passengers to confirm their presence on a booked flight, usually opening up for them a few days beforehand. The airline sends a link to the passengers who have bought a ticket for the flight, and they are directed to a “check-in” web page. That page automatically logs in the passenger, so there’s no need for an authentication step, and depending on the airline, the client may also perform a couple of last-minute changes. Now, the problem with those directing links is that a hacker who is on the same network as the person who bought the ticket can intercept the link request, accessing the check-in web page without further effort.
From the Wandera report
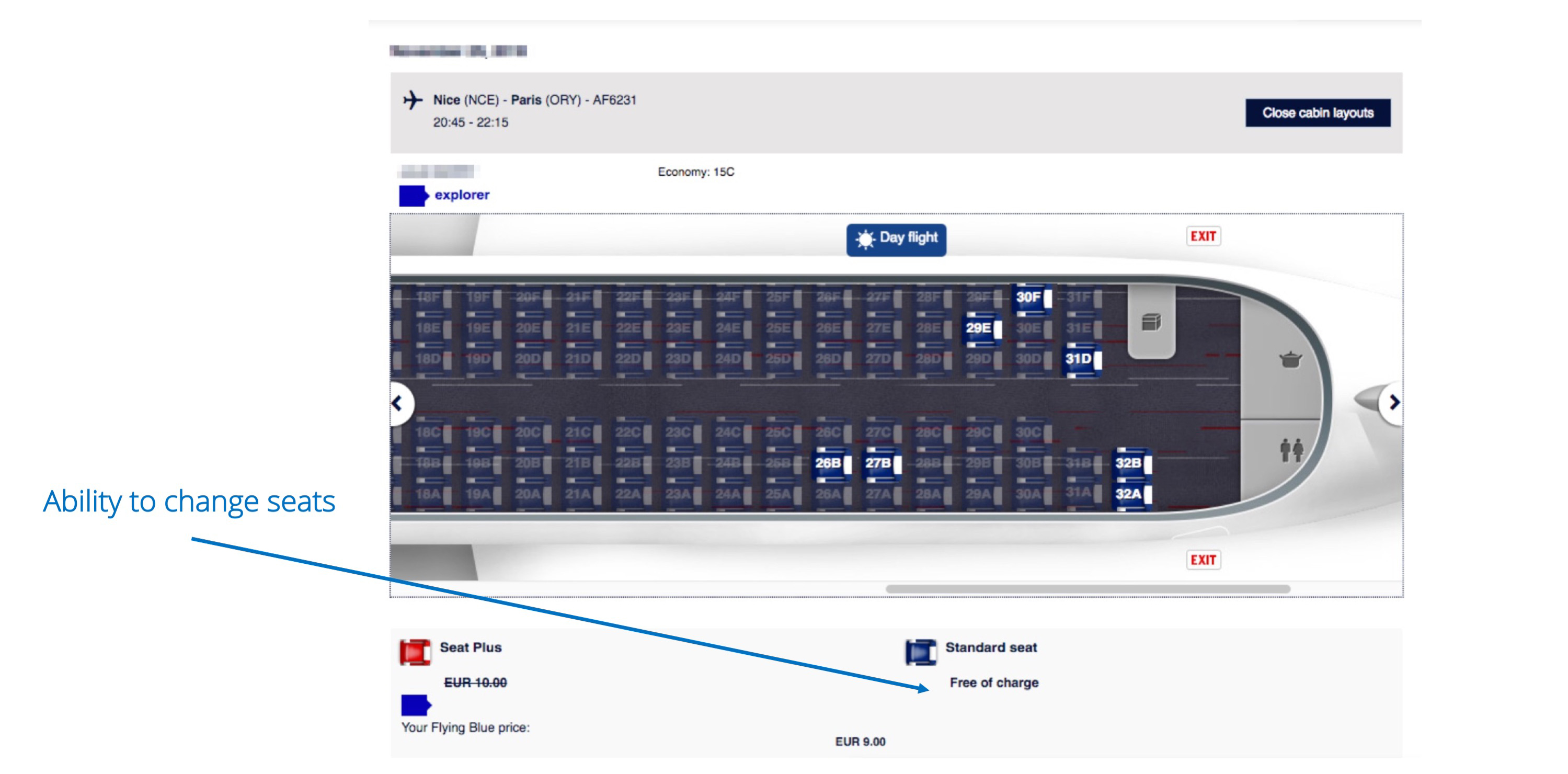
In there, the hacker may find all kinds of information about the passenger, including the full name, ID and passport numbers with their expiration dates, flight number and time, email address, seat and baggage handling selections, and the boarding passes. This gives the hacker the capacity to add or remove baggage, tamper with the seat selection, change the passenger email or phone number, and generally cause a disturbance to the passenger’s flight without the customer ever realizing that something is wrong until they enter the cabin.
From the Wandera report
Not all airlines offer a full-fledged set of flight booking options in their check-in web page, however, and following their “4-weeks non-disclosure policy” Wandera is not revealing which of the eight that were investigated are the riskiest at this moment. The majority though is giving out more than they should, with only three of them not giving access to the full boarding pass. The risks that arise from this vulnerability can be easily mitigated by sending encrypted check-in links, requiring authentication when accessing the check-in web page, and by using one-time access tokens for the sent links. Hopefully, the eight risky airlines will take Wandera’s findings seriously and will incorporate the proper precautions to ensure the safety of their customers’ data. Considering that we have little choice or say in the check-in process, it’s entirely up to them.
Have you ever experienced an inexplicable check-in or boarding pass mix-up? Let us know of the details in the comments section below, and don’t forget that you are helping us spread the world by sharing stories like this one through our Facebook and Twitter.