Peloton Bike+ Plagued by Bootloader Vulnerability Giving Actors Root Access
- McAfee researchers discovered that it’s possible to run custom OS images on Peloton Bike+.
- This should be prevented by AVB, which is in place, but a bug in its implementation allows the exploit.
- Peloton addressed the flaw via an update quickly after receiving McAfee’s report, so you should update your device now.
If you own and use a Peloton Bike+, you should apply the available patches immediately, updating to software version “PTX14A-290” or later. This release fixes a critical bootloader vulnerability discovered and reported to Peloton by McAfee’s Advanced Threat Research team, and which opened up an entire set of exploitation potential for malicious actors.
That would include spying on the user through the device’s microphone and camera, accessing personal data on the fly, installing additional software or modifying the existing (via root-level access), perform “man in the middle” attacks, sniff network traffic, and more.
The problems begin with a bypass of the Android Verified Boot process to fully compromise the Android OS that runs on the Peloton Bike+. Typically, that would happen by planting a malicious booting agent, which would run a modified OS image that gives the actor elevated privileges.
Practically, this requires physical access to the device, but considering the type of the product, one would have numerous tampering opportunities. From service and maintenance technicians to warehouse storage or retail store employees, a large number of people could potentially plant a malicious image before the device is even bought and set up.
McAfee’s researchers used a generic TWRP recovery image while exploring various system backup methods, and to their surprise, they found that it got past the fastboot boot command. This was a sign that custom images weren’t verified properly by the Android Verified Boot system.
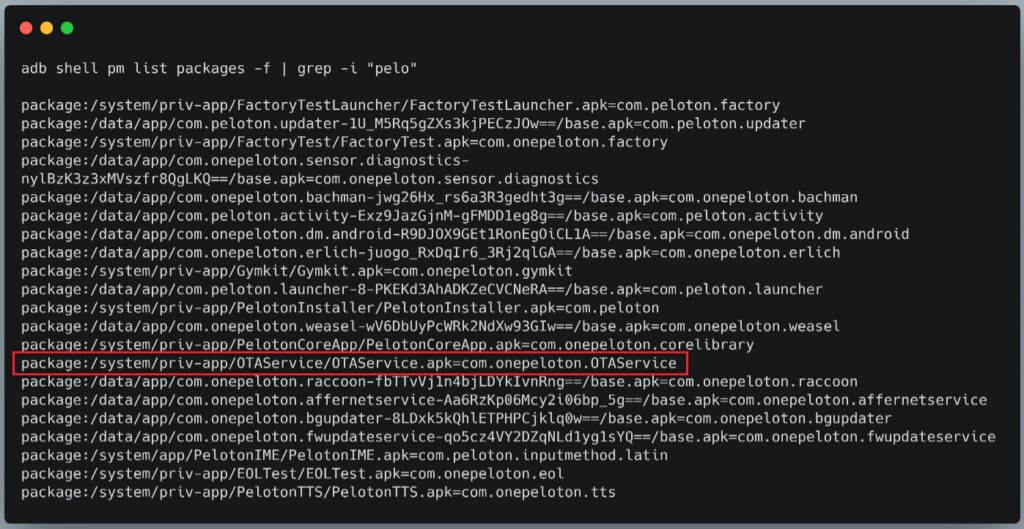
Next, they acquired an image from an OTA (over the air) update as they still needed a valid kernel and drivers for the device, modified it for attacking scenarios, and then loaded it to the Bike+. Since they had incorporated the “su” command on the new image, they could easily gain root-level access to all functions of the system.
Peloton’s fix addresses the AVB check gap and prevents all third-party builds from running on the device, so the mitigation covers all possible iterations of the attack. In this case, the protection system (AVB) was actually in place, but it didn’t work properly due to a bug. If it wasn’t for McAfee’s digging, it could have gone unnoticed and potentially exploited for a long time.
Last month, a security researcher discovered API access flaws in the Peloton network, enabling anyone to freely access sensitive data about Peloton users without leaving a trace or indication. Peloton was characteristically slow in admitting and addressing the reported flaw, leaving its entire userbase pray to malicious actors for a total of four months. In the case of the bootloader though, the fixing came a lot quicker.