“Paay” Left an Unprotected Database Online Containing Credit Card Details
- Approximately 2.5 million credit card transactions belonging to 20 merchants were exposed online.
- The unprotected database was left accessible and without a password for about three weeks.
- The company responsible for the security lapse denies that their system holds credit card numbers, but the data samples say otherwise.
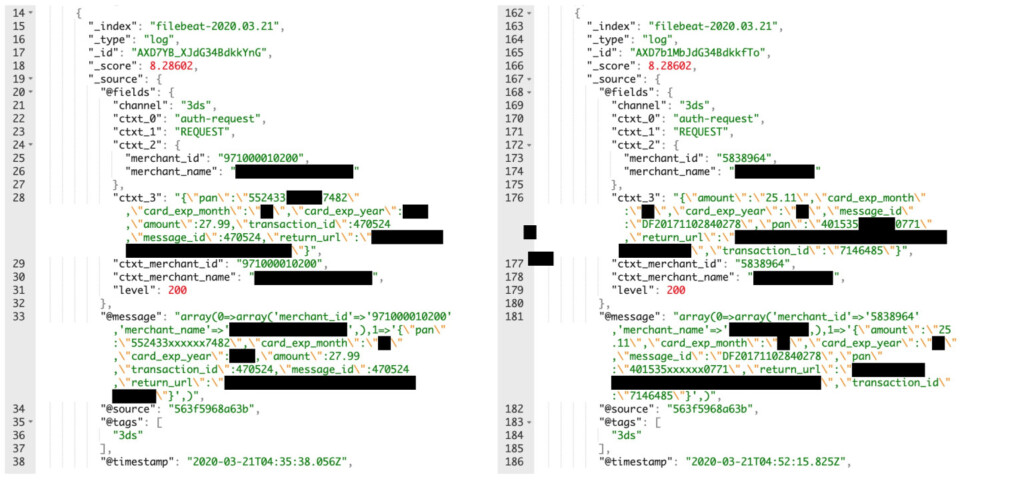
A mobile payment solutions provider based in New York called “Paay” has made a grave mistake by leaving a database online without password protection. The data that exposed includes roughly 2.5 million records that concern credit card transactions dating as far back as September 1, 2019. Each record contained the credit card number in plaintext form, the expiry date, and the amount of the transaction. Moreover, there was a partially masked copy of each credit card number, but thankfully, the cardholder names and the CVV codes were not stored in the exposed database.
This would make it harder for hackers to sell the data to fraudsters, but the exposed data is far from being considered useless. The discovery of the database was the work of security researcher Anurag Sen, and according to the official admission that followed, the information remained exposed and accessible for three weeks. Paay co-founder Yitz Mendlowitz explained that the error occurred on April 3, 2020, and happened during the setting up of a new Elasticsearch instance for a service that they are in the process of deprecating. Paay’s IT team forgot to set up a password for the new database, and no one noticed the problem during the three weeks it existed.
The spokesperson explained that they do not store card numbers as they have no use for them, so he disputed the above claims. However, TechCrunch, who got to check the data themselves after Anurag Sen shared a portion with them, have confirmed that there are credit card numbers in there. That said, their denial of storing this type of data doesn’t stand. Paay is currently working with a forensic auditor to determine the amount, scope, and extent of the damage. So far, it seems approximately twenty merchants have been affected by this incident, so they are being contacted by the firm to take the appropriate action.
Source: TechCrunch
Paay is offering services meant to help merchants stay protected from fraud, providing charge-back liability shift off via the EMV 3DS global security protocol. In the EU, Paay is using the PSD2 to facilitate customer authentication and verify the cardholders. This incident proves that even advanced tech solution providers can blunder in the simplest of ways, which is to leave a database online without password protection. As for the affected merchants, they will now have to endure the trouble and defamation that comes with informing their customers about a data breach caused by one of their partners.