Operation Serengeti 2.0: Trend Micro Backs INTERPOL in Record Cybercrime Crackdown
- Cybersecurity collaborators: Trend Micro announced its contribution to the African Interpol crackdown, resulting in over 1,200 arrests.
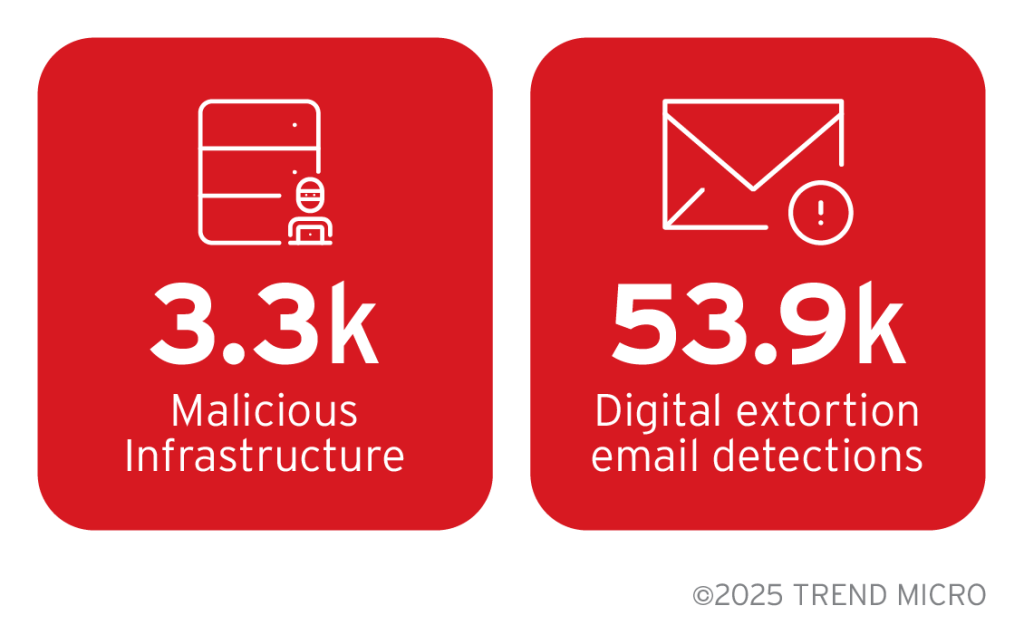
- In numbers: The cybersecurity company identified 3,300 malicious infrastructures and 54,000 digital extortion campaigns.
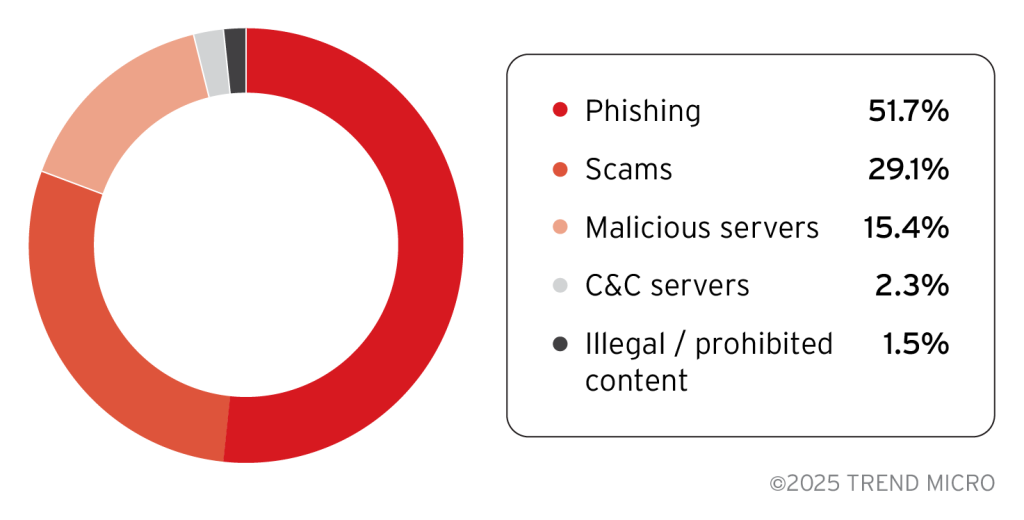
- Main threats: Of the identified cyber threats, more than half involved phishing and almost 30% scams.
The Trend Micro Operation Serengeti collaboration with INTERPOL has delivered unprecedented results in combating cybercrime across the African continent, as the cybersecurity company contributed with detecting digital extortion and mapping and sharing essential intel on malicious infrastructure.
Trend Micro's Strategic Intelligence Contributions
As a key operational partner, Trend Micro provided comprehensive threat intelligence that directly supported investigative outcomes. The company's technical contributions included:
- mapping 3,300 malicious infrastructures hosted across Africa
- detecting almost 54,000 digital extortion and sextortion campaigns targeting regional organizations
- sharing actionable intelligence on
- command-and-control (C2) servers,
- IP addresses,
- domain infrastructures.
The comprehensive cybercrime crackdown in Africa resulted in 1,209 arrests, the dismantling of 11,432 malicious infrastructures, and the recovery of $97.4 million in illicit funds between June and August 2025. Trend Micro reports that in the African region, identified threats were:
- 51.1% phishing
- 29.1% scams
- 15.4% malicious servers
- 2.3% C2 servers
- 1.5% illegal or prohibited content
This intelligence-sharing framework enabled law enforcement agencies to rapidly identify criminal infrastructure and implement proactive victim protection measures. Trend Micro's data facilitated the expedited investigation of cybercriminal networks operating across multiple jurisdictions.
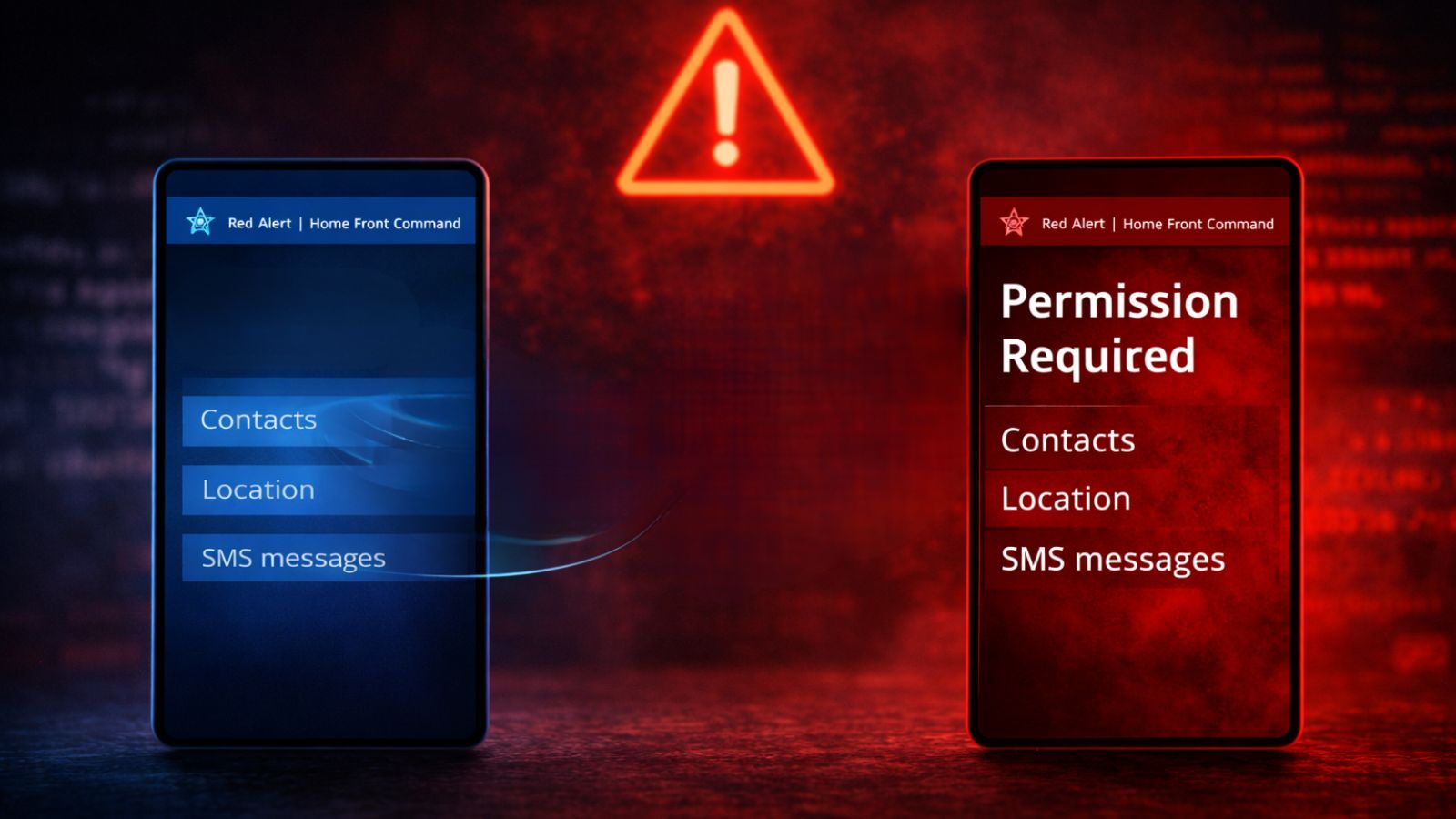
The INTERPOL cybercrime operation targeted critical threats identified in the INTERPOL Africa Cyberthreat Assessment Report, including ransomware, online scams, and business email compromise (BEC). Investigators from 18 African nations and the U.K. coordinated enforcement actions that ultimately protected nearly 88,000 potential victims.
Notable operational achievements included dismantling 25 illegal cryptocurrency mining centers in Angola with $37 million in seized equipment, 15 arrests related to the disruption of a $300 million investment fraud scheme in Zambia that affected 65,000 victims, and neutralizing a $1.6 million inheritance scam operation in Côte d'Ivoire with the arrest of the main suspect.
Other operational partners include Cybercrime Atlas, Fortinet, Group-IB, Kaspersky, The Shadowserver Foundation, Team Cymru, TRM Labs, and Uppsala Security.
Operational Training and Capacity Building
Prior to Operation Serengeti 2.0 execution, Trend Micro conducted specialized training workshops focused on ransomware analysis and investigative methodologies. These cybersecurity collaboration initiatives enhanced law enforcement capabilities, enabling personnel to pursue cybercriminals with improved technical precision and operational effectiveness.
The training component represents a critical element of sustained cybercrime disruption, building regional investigative capacity for future enforcement operations.
Other notable law enforcement crackdowns on DDoS-for-Hire services have resulted in the arrest of administrators and the seizure of domains.