The Official Facebook Chat Plugin for WordPress Was Vulnerable to Takeover
- Websites that are using the Facebook Messenger Chat plugin for WordPress are vulnerable to attacks.
- Hackers can potentially divert communications, answer to visitors as admins, and cause a host of problems.
- Visitors should never share sensitive details with customer service and support agents on websites.
According to a report by Wordfence, Facebook’s official chat plugin for WordPress, which is found in more than 80,000 websites out there, could make it possible for malicious actors to engage in social engineering. The discovered flaw is given a CVSS score of 7.4 and was found on June 26, 2020.
Upon contacting Facebook with all the associated details, the researchers were asked for more clarifications, which led to delays in the fixing. Eventually, Facebook released version 1.6 of the plugin, which addressed the discovered flaws on July 28, 2020, a full month later.
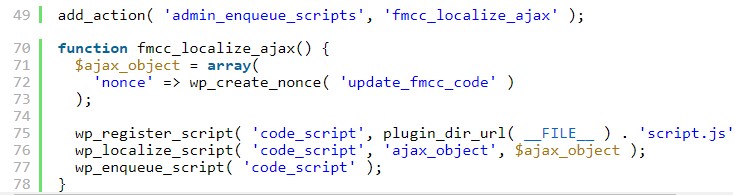
The particular plugin enables a WordPress site's visitors to log in to their Facebook account and interact with other site visitors through a Messenger chat pop-up. The plugin registers an AJAX function to set up on the hosting website, but that function isn't checking the admin's requests, so there's no authentication.
This could potentially allow a malicious actor to send a request to update the Messenger plugin's options, changing the set account to their own. To do this, the attacker would simply have to register to the WordPress site that runs the Messenger plugin, which should be possible in most cases.
Source: WordFence
Any messages on the chat would then pass to the attacker and not the website admin, which means that site visitors would interact with a hacker without having a way to realize it. The obvious repercussion of this would be to fall victim to social engineering attacks.
For the website owners, they could suffer defaming actions, chat downtime, and loss of sales. There's really a wide range of catastrophic scenarios that are direct outcomes of this vulnerability.
As a site visitor, you can mitigate the risks of getting trapped by hackers by refusing to share sensitive information like credentials, credit card details, etc. Customer service agents should never ask you your credentials, and they would typically have no access to them anyway.
Always treat these communications as potentially compromised, since you have no way to ensure that they aren't. From the perspective of WordPress site admins, you should keep your plugins up to date, so you should move to version 1.6 immediately.