OAuth Redirect Abuse Targets Government and Public Sector Organizations, Microsoft Warns
- Exploited Authorization Flows: Threat actors are manipulating OAuth redirect URIs to route authenticated users to malicious infrastructure undetected.
- Sophisticated Payloads: The campaign deploys embedded ZIP malware and utilizes EvilProxy phishing links to steal session tokens and bypass MFA.
- Critical Mitigation: Microsoft advises immediate administrative audits of application consent policies to secure public sector networks.
Microsoft has issued a critical security alert regarding an escalating campaign in which threat actors use OAuth redirect abuse to compromise high-value infrastructure. This sophisticated operation specifically targets public sector entities, exploiting trusted enterprise applications to bypass standard perimeter defenses and seamlessly deliver malicious payloads to end users.
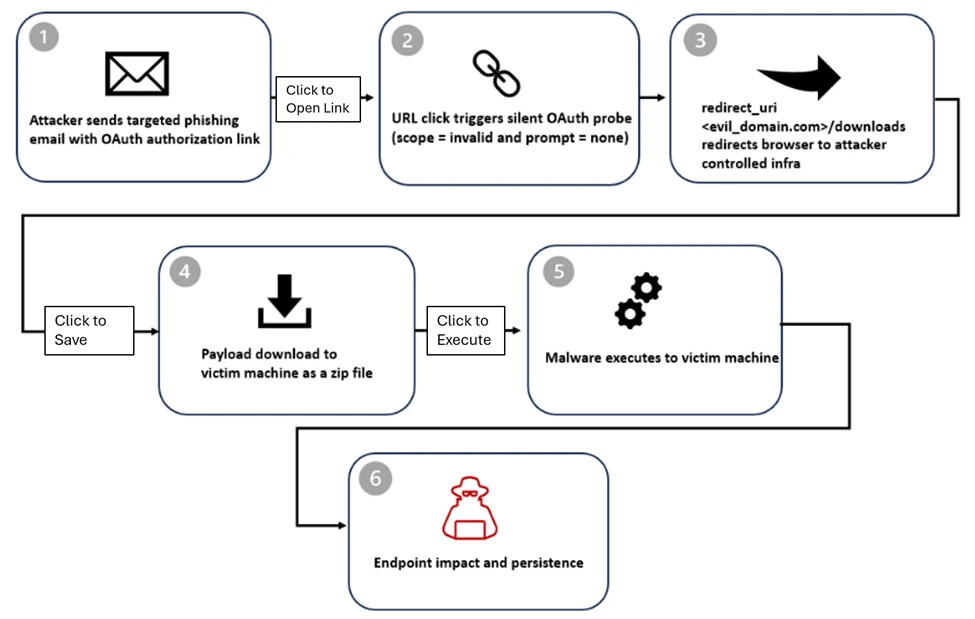
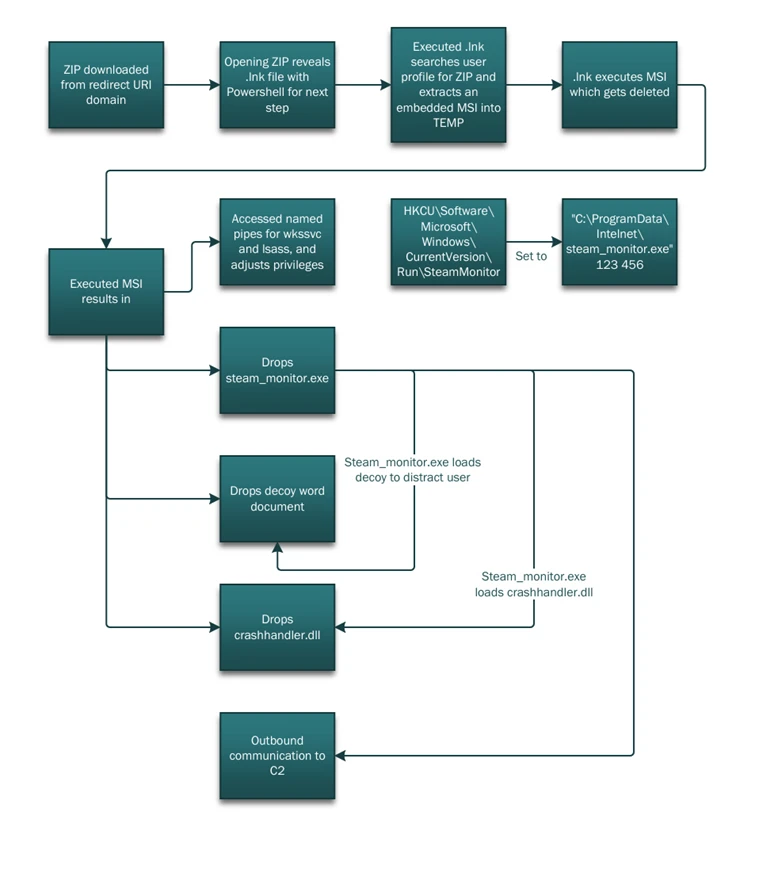
Execution of the Government Malware Attack
Threat actors are manipulating the standard OAuth authorization flow, routing authenticated users to external, attacker-controlled domains by hijacking legitimate redirect URIs within registered applications.
The recent Microsoft OAuth warning details that this vector serves a dual operational purpose: distributing embedded ZIP malware and routing victims through EvilProxy phishing infrastructure.
EvilProxy functions as an adversary-in-the-middle (AiTM) framework, explicitly designed to steal credentials and session cookies. Phishing pages often use proxy-based login interception, CAPTCHA challenges, and interstitial pages.
Exmail lures observed in the phishing/malware campaign and related social engineering themes include document sharing and review, social security, Teams meetings, password resets, and employee reports.
Mitigating Escalating Cybersecurity Threats
This specific government malware attack demonstrates that the abuse is operational and attackers increasingly target trust relationships and protocol behavior. Identity and access management (IAM) remains a primary battleground for network defense.
“These findings reinforce the need for cross-domain XDR detections, clearer governance around OAuth redirection behavior, and continued collaboration across the security community to reduce abuse while preserving the interoperability that OAuth enables,” Microsoft said.
Microsoft advises IT administrators to:
- Rigorously audit all registered OAuth applications,
- Limit user consent
- Regularly review application permissions,
- Remove unused or overprivileged apps.
Furthermore, combining these measures with identity protection, Conditional Access policies, and cross-domain detection across email, identity, and endpoint helps neutralize this specific abuse of federation protocols and protect sensitive government data architectures.
Last summer, OAuth tokens were exploited in the Salesloft breach to steal Salesforce data. Gainsight’s September investigation confirmed a data breach due to stolen OAuth tokens linked to Salesloft Drift.