New RaaS Called ‘BlackMatter’ Emerges to Fill the Gap Left by REvil and DarkSide
- A new top-tier RaaS operator has appeared on the dark web, claiming to be the continuator of REvil and DarkSide.
- The actors set the bar high, aiming to compromise only large entities but not crucial or role-sensitive organizations.
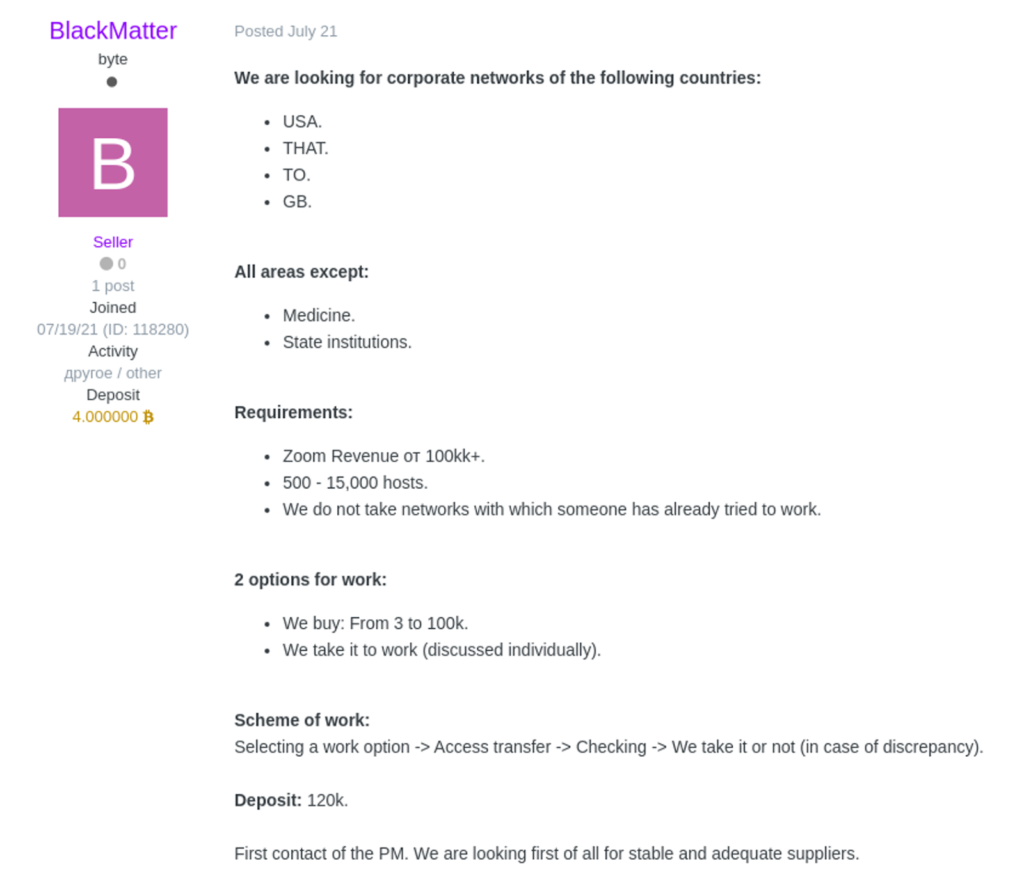
- The new group will pay between $3,000 and $100,000 for initial network access, depending on the size of the target.
Researchers at Recorded Future have noticed the appearance of new ransomware as a service (RaaS) operation named ‘BlackMatter,’ which promotes itself as the spiritual continuation of DarkSide and REvil. Those two notorious ransomware groups have disappeared all of a sudden from the cybercrime scene following two high-profile incidents that drew a lot of media and law enforcement attention upon them. Naturally, a gap was created at the highest level, and BlackMatter aims precisely there, targeting only big companies with yearly revenues of $100 million or more.
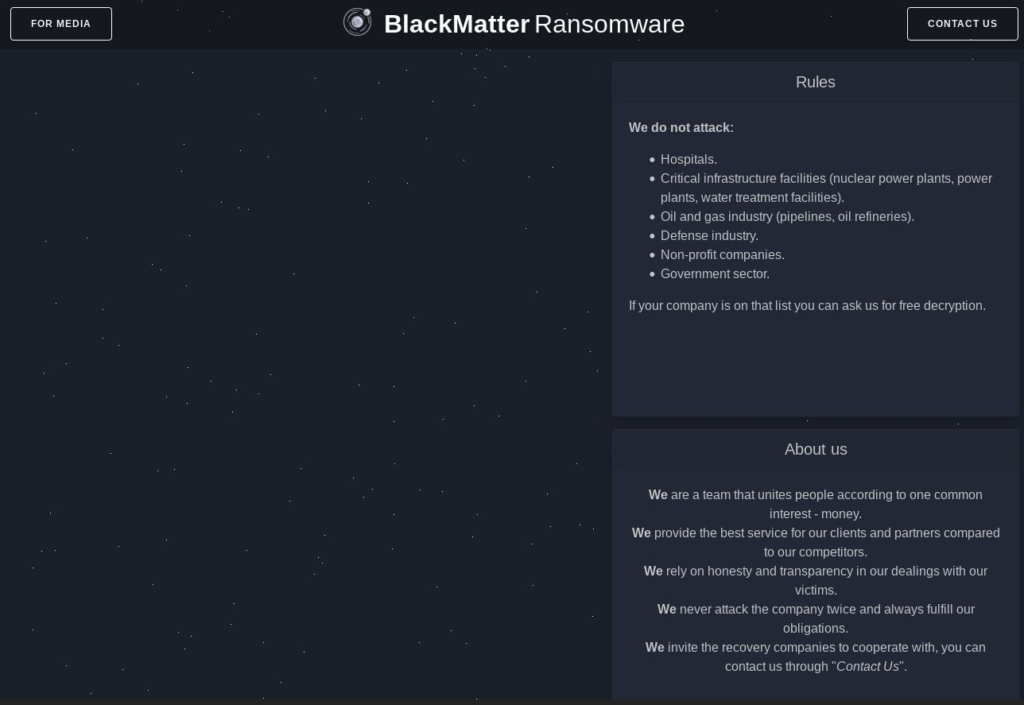
On announcing the launch of the ‘BlackMatter’ RaaS program, the group declares that its only interest is money. Still, some exclusions like hospitals, critical infrastructure facilities, the oil and gas industry, the defense industry, non-profit organizations, and government entities will apply. Also, the targets can be in the United States, Great Britain, Canada, or Australia, and they need to count at least 500 hosts to be eligible. No victim should be attacked twice, and if any mistakes of this kind happen, the actors promise to give away a decrypting key for free to the victimized entity.
Of course, similar promises have been made again by past RaaS operators, and along the way, they didn’t enforce their own rules or simply didn’t care about affiliate compliance at all. As such, these rules mean nothing until we start seeing firms getting victimized.
BlackMatter offers at least $3,000 and up to $100,000 for network access, depending on the victim, and has already deposited 4 Bitcoins on the Exploit forum, an amount that is to be used for purchasing access to compromised organizations. The option to give a cut to a contractor is also available, but no details about that have been posted yet (is discussed privately).
As for the ransomware strain itself, the actors claim to have combined the best parts of REvil, LockBit, and DarkSide, supporting all operating systems and a wide variety of filesystem types. For now, researchers haven’t sampled a payload, so nobody can tell if it features the sophistication of REvil’s key distribution system, Lockbit’s speed, or DarkSide’s strong encryption. What can be said is that BlackMatter's dark web portal design resembles the one used by DarkSide, although this doesn’t mean the two are necessarily linked.
Brett Callow, Threat Analyst at Emsisoft, a leader in the development of ransomware decryption tools, has shared the following comment with us:
From what seems to be the case, ‘BlackMatter’ will be making headlines in the following months, so that we will be keeping an eye on their portal for any updates and victim announcements.