New Phishing Campaign Employs ‘Supreme Court Settlement Agreement’ Tactics
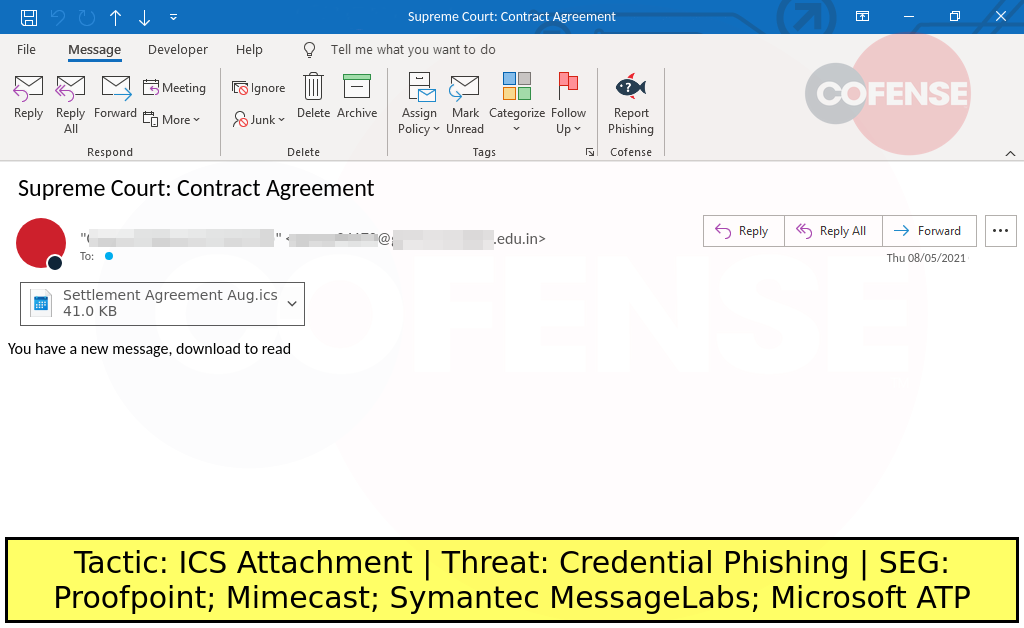
- Phishing actors are now using fake Calendar invites to trick recipients into clicking on URLs.
- The theme is a supposed meeting for a settlement agreement on a Supreme Court-level case.
- The links lead to phishing login sites that offer the victim the choice of the account they wish to give away.
Even though there aren’t many people who are hoping to receive a lucrative settlement agreement and have their legal case resolved, getting an email with a relevant subject is definitely interesting - if not of intimidating importance for some. As Cofense reports, this is precisely the trick employed by phishing actors lately, as the security company has noticed a surge of email subjects talking about a supposed agreement in a ‘Supreme Court’ case no less.
These emails come with malicious attachments that have the form of an ICS file (iCalendar), and their goal is to perform credentials phishing. Opening the attachment triggers a calendar invite containing a meeting notice that instructs the recipient to click on the link in order to get more details
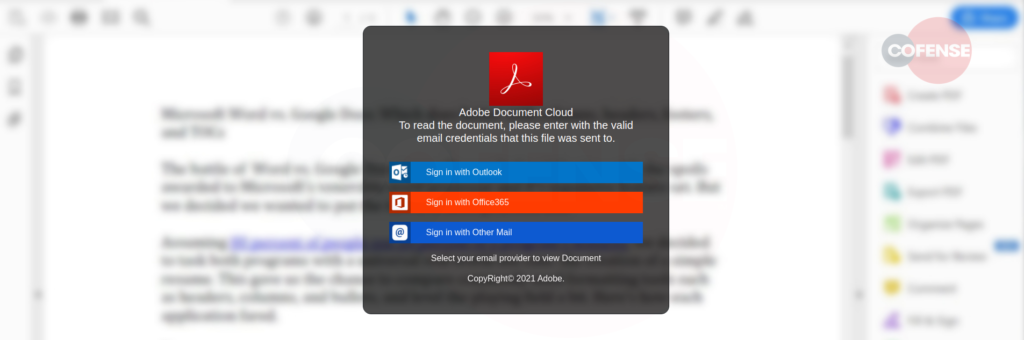
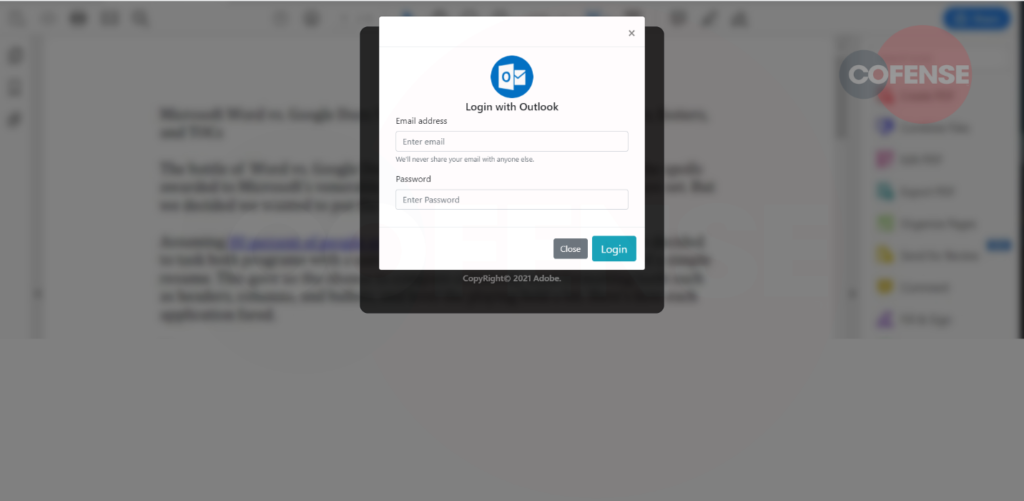
Clicking on that link leads to a phishing page that prompts the user to log in to Outlook or Office365 or any email provider they may be using. The typical trick of blurring a supposed document in the background is seen here too, so consider this a huge red flag in general.
Another interesting aspect of this phishing campaign is that the URLs used in these phony meeting invites do not end with a “.com” but with “court,” like for example: “hxxp://0xc1a9fd67/Court” or “hxxp://0xc1a9fd67/Supremecourt”, which resolve to “hxxp://193[.]169[.]253[.]103/Court” and “hxxp://193[.]169[.]253[.]103/Supremecourt”. This works well both as a legitimacy booster and as a way to bypass checks from security endpoint detection tools.
Confense’s report has the full list of the indicators of compromise, including the IPs where the credentials are getting exfiltrated to, so make sure to check out the relevant information if you’re preparing a blacklist. Some of these URLs and IPs have been previously associated with the phishing-as-a-service platform known as ‘BulletProftLink,’ a Malaysian service that offers ready-made phishing pages and also hosting for only $100 per month. This service has been around since at least 2018, and it appears that it’s still rocking three years on.