New IVPN Client App for Android Adds GPS ‘Location Mocking’
- IVPN’s new Android app can spoof the device’s GPS location and send fake data to spying apps.
- The system isn’t completely foolproof, but it should be enough for the majority of users.
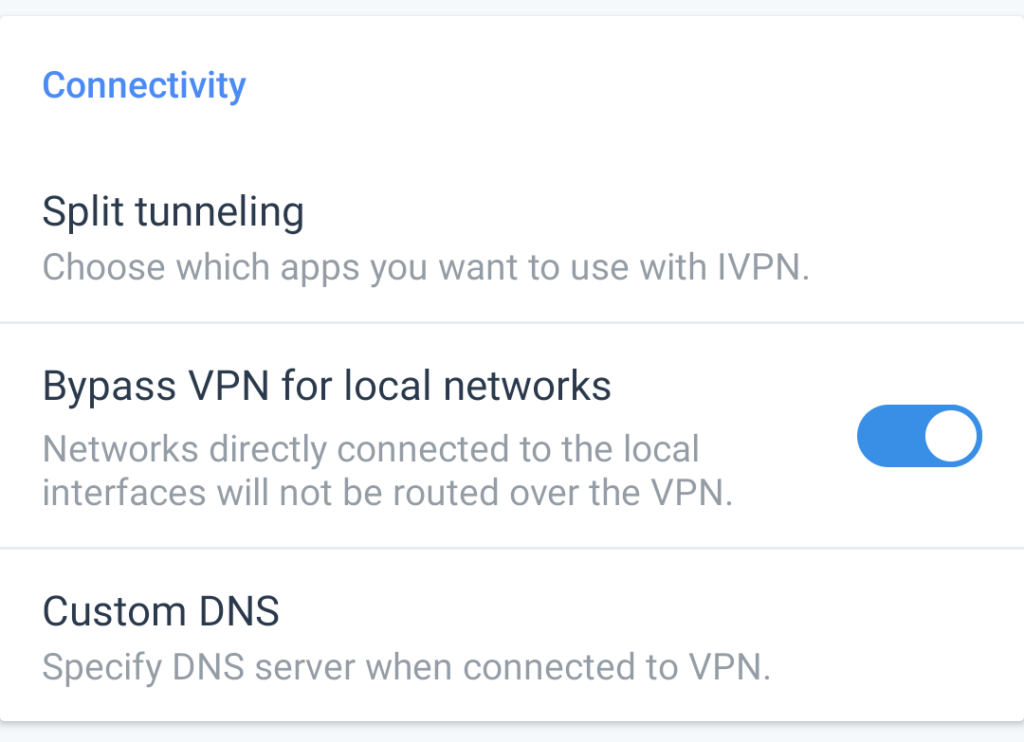
- Another option to bypass VPN when connecting to trusty devices has also been added.
The latest version (2.4.0) of the IVPN app for Android came out today, bringing two new key features that boost user privacy and comfort. First, there’s an option to ‘bypass VPN for local networks,’ and second, there’s the mocking of the GPS location on the device.
This is something similar to Surfshark’s GPS Spoofing system. In both cases, we see it as a measure to protect the users’ privacy against applications that attempt to track and log GPS data in the background.
IVPN explains that this will also work against annoying advertising or any kind of targeted activities. However, the VPN vendor warns that ‘Mock Location’ isn’t foolproof, so one shouldn’t rely on it if protecting this kind of information is crucial for your safety. For regular users who aren’t in a high-risk situation, it should work fine, though.
The ‘Bypass VPN’ option lets users access devices on the local network like printers, for example, without having the pass the traffic through the usual encryption tunnels. This is just a convenience option that, if used responsibly, shouldn’t introduce any risks for the users.
In our 2020 review of the IVPN product, we praised it for privacy protection and availability of features, as well as speed and performance. What the product was missing is media streaming and torrenting support, as well as a rich set of server options. Back then, only Netflix was supported, while Hulu, Amazon Prime Video, and Kodi all failed to connect. We will make sure to revisit IVPN, though, and check again, so stay tuned for an update on that review.
In the meantime, it is important to mention that all IVPN apps were recently audited by independent expert ‘Cure53’, who have spent 18 days scrutinizing the entire range and finding a total of four critical and important vulnerabilities, which were resolved immediately. In addition to these, Cure53 found another ten miscellaneous issues, eight of which were fixed right away and two low-importance currently mitigated.
Notably, the VPN firm has decided to publish all details about the pentest findings for reasons of transparency, so if you want to access the technical details, check out this report.