New Cryptojacking Campaign Exploits DevOps Exposures Across Cloud Environments
- A newly discovered malicious cryptocurrency mining campaign exploits misconfigurations and known flaws.
- Hackers target public DevOps applications like HashiCorp Nomad, Consul, Docker API, and Gitea.
- The attackers rely on official XMRig releases for mining Monero on compromised machines.
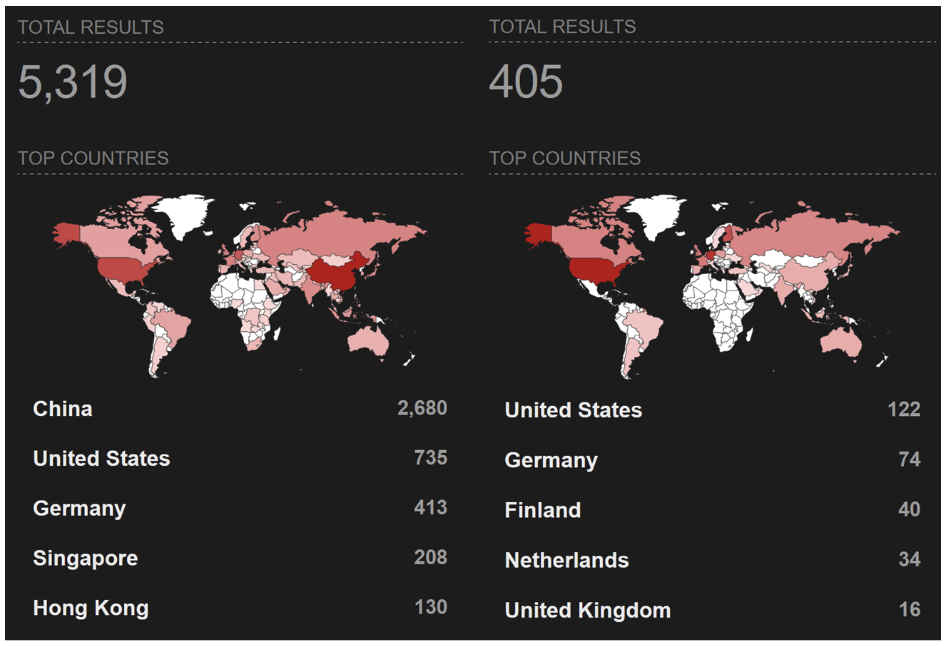
A widespread cryptojacking campaign, dubbed JINX-0132, targets publicly accessible DevOps applications including HashiCorp Nomad, Consul, Docker API, and Gitea, a recent investigation by Wiz Threat Research has uncovered.
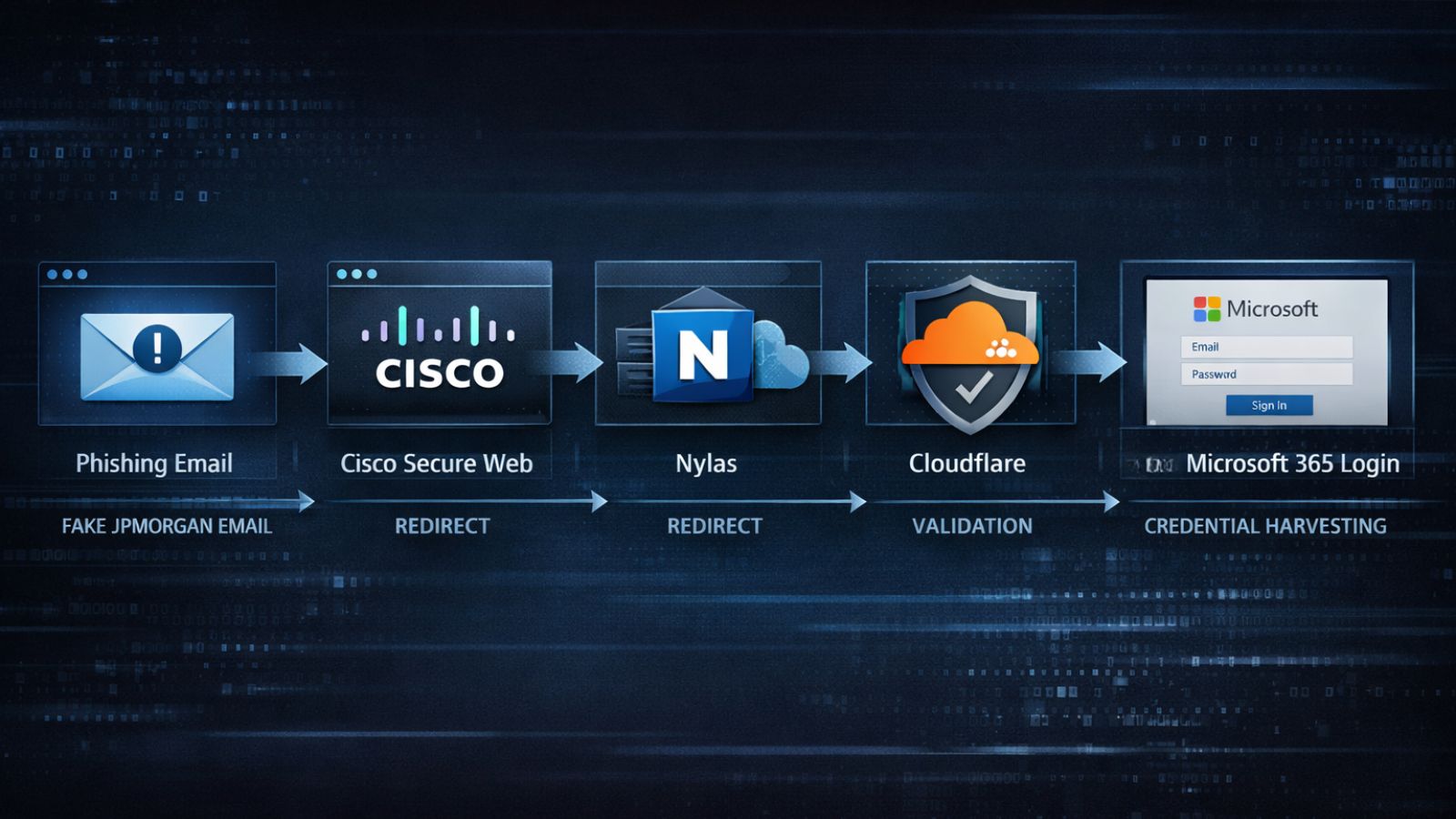
JINX-0132’s approach relies heavily on exploiting misconfigurations and known vulnerabilities rather than deploying traditional malware with easily detected Indicators of Compromise (IOCs).
The attackers leverage standard, publicly available tools from platforms like GitHub—for example, using official XMRig releases for mining Monero.
This off-the-shelf tactic complicates attribution and threat clustering, as the payloads are not customized and can evade common security detections.
- HashiCorp Nomad: Attackers abuse insecure default APIs, granting themselves unrestricted remote code execution capabilities by submitting malicious jobs to exposed Nomad servers.
- Gitea: JINX-0132 potentially leverages outdated software versions, misconfigured git hooks, and unlocked installations to gain initial access and deploy mining payloads.
- Consul: The campaign exploits insufficient access control and script-enabled service health checks, allowing arbitrary code execution through maliciously registered checks.
- Docker API: Exposed Docker daemons provide attackers root-level access to build and run mining containers directly on victim hosts.
This marks the first documented incident of misconfigured Nomad servers being actively exploited for malicious cryptocurrency mining in the wild.
Wiz data indicates that about 25% of cloud environments run at least one of these DevOps tools. Of these, 5% expose them to the internet, and 30% of the exposed instances are misconfigured, underscoring widespread vulnerability.
Breached instances have exhibited substantial computing capabilities, often costing victims tens of thousands of dollars per month.