‘Network Rail’ in the UK Leaked the Data of 10000 Travelers
- Various UK train station visitors were exposed through an unprotected public-access database.
- The firm responsible for this blunder is C3UK, and the incident affects about 10000 travelers.
- The event underlines the dangers of using free WiFi networks, and the need to use a mobile VPN.
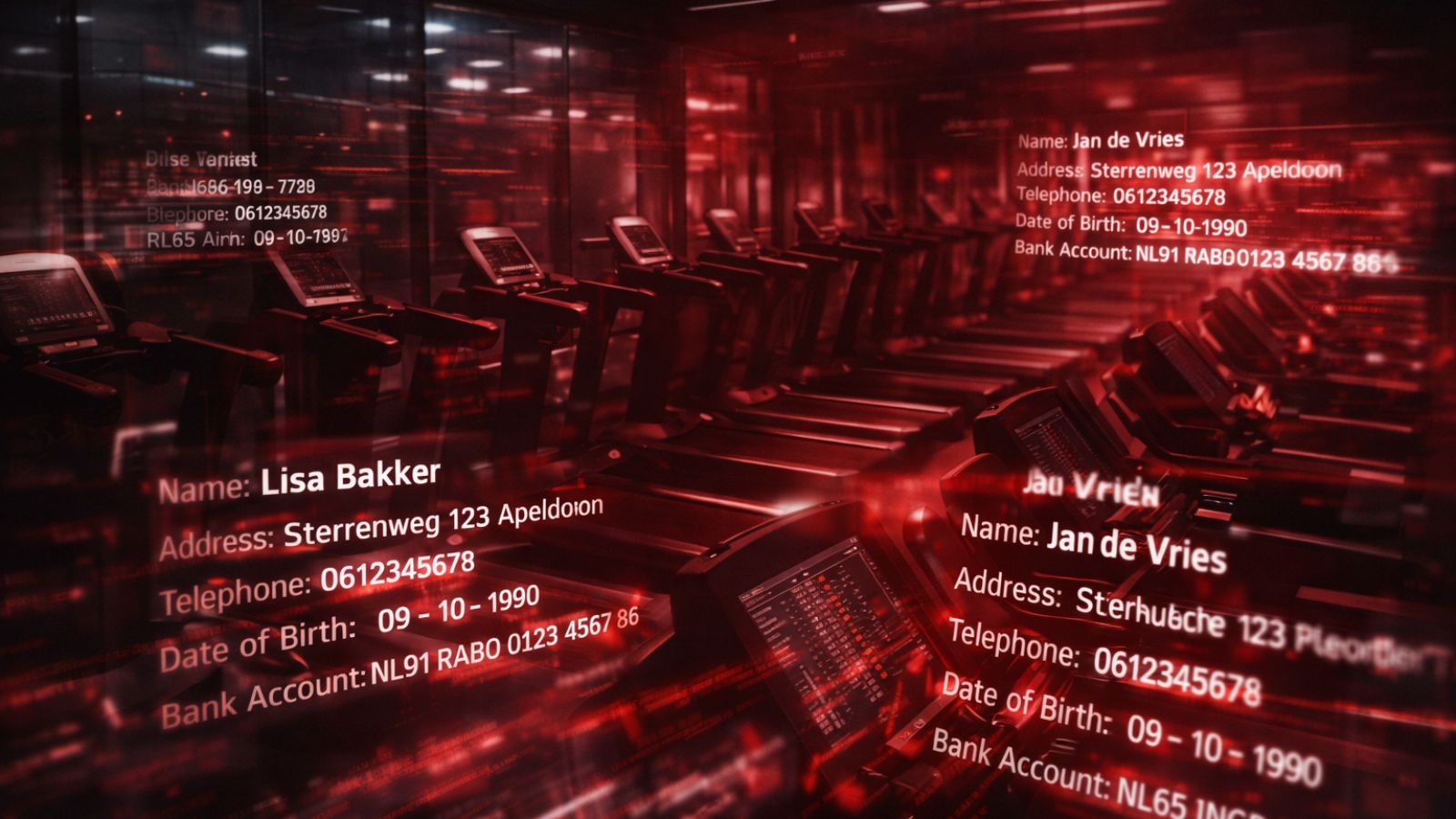
‘Network Rail’, the largest railway network infrastructure owner and manager in Great Britain has admitted a security incident that affects about 10000 travelers. The compromised data involves the email addresses, dates of birth, and travel details of these individuals. The exposure occurred through an unprotected database that was set to public access without a password. The entity responsible for the database is ‘C3UK’, who is an internet service provider and a contractor of ‘Network Rail’. The leaky server has been secured now, and C3UK told the press that they found no signs of anyone having accessed the data besides the researcher who discovered it on February 14, Jeremiah Fowler.
The researcher says that he counted 146 million records, including details about the WiFi network of the stations where people attempted to connect to, their IP addresses, and various collections of internal logs. This means that the travelers who were exposed are those who tried to connect to the WiFi network offered by ‘Network Rail’ through C3UK. The railway stations that can be confirmed as affected are the “Harlow Mill”, “Chelmsford”, “Colchester”, “Waltham Cross”, “Burnham”, “Norwich”, and the “London Bridge”.
Since travelers have had their email addresses exposed, they are now running the risk of receiving spam email, getting scammed, or even phished. The exposed data is very revealing, containing the time when the user logged on a station, ads they watched through the station’s internet service, the postcode of their location, the reason for traveling, and more. This data would make the efforts of phishing actors a lot easier and comes as a clear reminder of why we should always be careful when using “Free WiFi” networks on public spaces.
In this case, people sought for quick internet access while traveling, but it looks like C3UK or Network Rail were grasping the chance to collect the valuable commodity that is personal data today. One could suggest that offering free WiFi makes a travel service more competitive, but this is not the whole part of the story. The researcher found evidence that the data was being collected for purposes of serving targeted ads, and it is quite possible that the C3UK was selling this data to various third parties.
As for the official response, Network Rail told the press that C3UK assured them that the exposed data was “low-risk”, while ‘Greater Anglia’ decided to stop their collaboration with C3UK altogether. The network provider decided not to comment on why they were collecting this data and told the press that travelers had a “prefer not to say” option when they were questioned for their reason for travel on the connection prompt.