MongoDB Flaw Allows Unauthenticated Memory Access, Immediate Patching Required
- Critical vulnerability: A significant security flaw has been identified in MongoDB, allowing attackers to read uninitialized heap memory from the server.
- Potential for data exposure: Sensitive data, including credentials, session tokens, and other confidential information, could be exposed if stored in the server's memory.
- Immediate patching required: MongoDB has released patches for the affected versions, and admins are urged to apply them immediately to mitigate the risk.
A critical MongoDB vulnerability has been disclosed that allows an unauthenticated remote attacker to access and read uninitialized memory on a vulnerable MongoDB server. This type of flaw can expose sensitive data fragments that may have been previously processed and are still present in the server's memory.
Technical Details of the Vulnerability
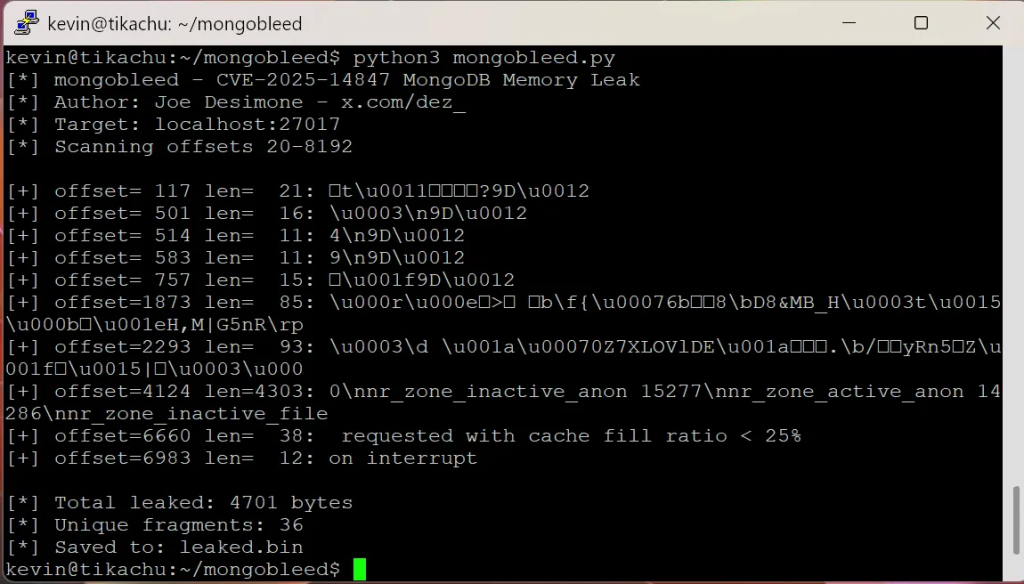
“A client-side exploit of the Server's zlib implementation can return uninitialized heap memory without authenticating to the server,” a MongoDB advisory reads. The vulnerability, tracked as CVE-2025-14847 (aka MongoBleed), stems from an issue in how the popular NoSQL database handles specific types of queries or commands.
An attacker can craft a malicious request that causes the server to return a response containing data from uninitialized heap memory. Because this action does not require authentication, any exposed MongoDB instance is a potential target.
An Elastic Security employee posted a proof-of-concept (PoC) exploit on GitHub, and Cybersecurity expert Kevin Beaumont validated it, stating that it harvests in-memory data such as:
- Database passwords (which are plain text),
- AWS secret keys.
The exploit does not allow for direct control over which memory is read, but an attacker can repeatedly query the server to collect a significant amount of data fragments over time. This information can then be pieced together to reconstruct sensitive information.
This issue affects MongoDB versions:
- MongoDB 8.2.0 through 8.2.3
- MongoDB 8.0.0 through 8.0.16
- MongoDB 7.0.0 through 7.0.26
- MongoDB 6.0.0 through 6.0.26
- MongoDB 5.0.0 through 5.0.31
- MongoDB 4.4.0 through 4.4.29
- All MongoDB Server v4.2 versions
- All MongoDB Server v4.0 versions
- All MongoDB Server v3.6 versions
According to Wiz, which validated many internet-facing instances as exploitable, “42% of cloud environments have at least one instance of MongoDB in a version vulnerable to CVE-2025-14847, including both publicly exposed and internal resources,” and Censys has reported observing 87,000 potentially vulnerable instances worldwide.
Mitigation and Cybersecurity Patch Update
In response to the discovery, MongoDB has released security patches, and administrators are strongly advised to immediately apply them to all affected MongoDB instances and upgrade to 8.2.3, 8.0.17, 7.0.28, 6.0.27, 5.0.32, or 4.4.30.
“If you cannot upgrade immediately, disable zlib compression on the MongoDB Server by starting mongod or mongos with a ‘networkMessageCompressors’ or a ‘net.compression.compressors’ option that explicitly omits zlib. Example safe values include snappy,zstd or disabled,” the advisory reads.
The exploitation activity appears to be opportunistic but well-timed, with attackers taking advantage of reduced monitoring and slower response cycles during the holiday period. Ben Ronallo, Principal Cybersecurity Engineer at Black Duck, said, "The threat actors were clever; they attacked during the holidays when many companies tend to be less responsive due to employees taking time off."
Ronallo shared the following for security teams:
- Confirm if you have any internet-facing systems with a vulnerable version of a MongoDB instance attached.
- If you find any such systems, immediately kick-off your incident response efforts to identify any potential compromise and contain the damage.
- There’s an open-source tool that can be leveraged to analyze MongoDB logs for indicators of compromise: https://github.com/Neo23x0/mongobleed-detector
- Any vulnerable versions should be patched immediately using official fixes from MongoDB.
Mayuresh Dani, Security Research Manager, at Qualys Threat Research Unit explained, "CVE-2025-14847 is dubbed "MongoBleed" and rightly so as it reliably leaks sensitive data from MongoDB instances akin to the infamous Heartbleed vulnerability in OpenSSL."
Dani recommended the following:
- Audit for MongoDB versions 3.6-8.2.2 with zlib enabled. This can be done with something like: mongod --version && grep -i "networkMessageCompressors\|compressors" /etc/mongod.conf. Internet facing systems can then be prioritized for updates and disable zlib compression immediately.
- Based on currently available proof-of-concept codes, the following patterns in MongoDB JSON logs (default in newer versions) can also be prioritized for incident response workflows:
- Event 22943: "Accepted connection" from unknown IP.
- Event 51800: "Client metadata" (MISSING - this is an important artifact).
- Event 22944: "Closed connection" - immediate disconnect from the IP.
- Firewall port 27017 (default MongoDB installations) access to trusted application servers only.
- Implement database-level authentication enforcement.
- Enable TLS/SSL for all MongoDB connections.
Last week, novice researchers were targeted via GitHub repositories containing fake PoC exploits for legitimate vulnerabilities.