Modlishka Hacking Tool Can Bypass 2FA Protection on Your Online Accounts
- A security researcher has developed a tool that is capable of bypassing SMS and email-based 2FA protection.
- The tool was tested on platforms like Yahoo and Gmail.
- The Modlishka tool takes advantage of reverse proxies to intercept data from target users.
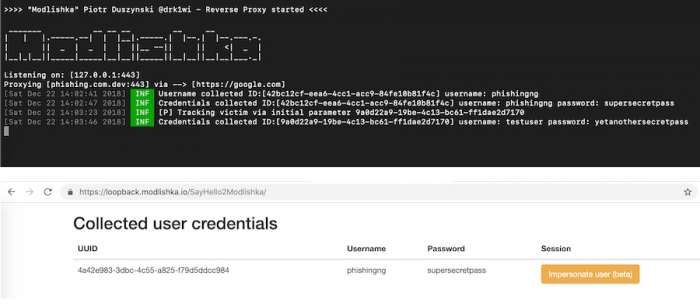
Polish security researcher Piotr Duszyński published a new hacking tool that can bypass 2FA protection on popular websites like Yahoo and Gmail. The tool manages to automate phishing attacks very effectively by utilizing a reverse proxy method. The Modlishka tool essentially modifies incoming traffic from users and intercepts it to steal login information.
The Modlishka tool’s proxy is placed between the target user and the website, and users unknowingly connect to the hacking tool’s server. The tool does not need to disguise itself as a genuine website as it is capable of stealing login information behind the scenes.
Image Courtesy of Piotr Duszynski
Modlishka also manages to trick 2FA systems as it is capable of collecting 2FA tokens in real-time without using any fake templates. All the tool needs are a valid TLS certificate and a phishing domain name to carry out the attacks. The tool is capable of impersonating legitimate websites by directly stealing config files from legitimate websites.
Duszyński revealed "The tool that I wrote is sort of a game changer, since it can be used as a 'point and click' proxy, that allows easy phishing campaign automation with full support of the 2FA (an exception to this is a U2F protocol-based tokens - which is currently the only resilient second factor)."
He also expects the tool to improve over time. Modlishka is one of the most effective tools that requires minimal technical skills, and it may lead to inexperienced hackers breaking into online accounts without any trouble. The tool is even more effective as most internet users are not aware of the risk that it poses.
If you want to secure yourself against tools like Modlishka, your best bet is to use app-based authentication instead of SMS or one-time codes as they can be intercepted. App-based authentication would require the official app to be infected if hackers want to steal private information which is far less likely than email or SMS based authentication to be compromised. Physical authentication keys are also viable for desktop and laptop users as there are no publicly known tools to compromise them.
What do you think about the Modlishka hacking tool? Let us know in the comments below. Don’t forget to visit our socials on Facebook and Twitter to join the discussions of our community.