Microsoft Takes the Final Step in Exchange Patching With Automatic Defender Mitigation
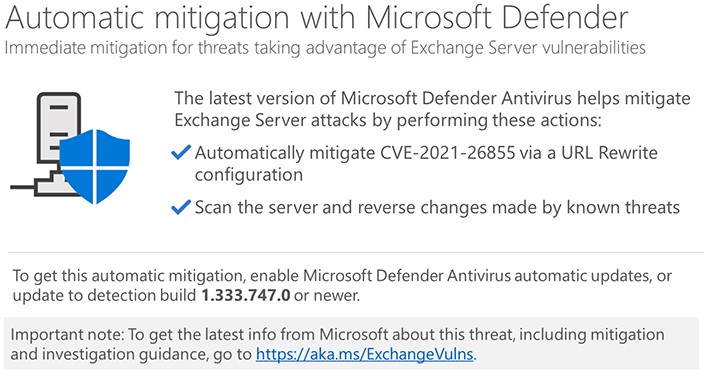
- Microsoft is now pushing an Exchange mitigation through a Defender security update.
- The tool will automatically scan for vulnerable servers, change URL configuration, and reverse known threat changes.
- Everything is fully automated, so hopefully, this will help secure tens of thousands of servers that remain vulnerable.
Microsoft cannot rely on admins to patch their vulnerable Exchange Servers this time, and they are moving forward with an automatic mitigation that comes through Defender. This comes on top of the repeated warnings, the actual Exchange patch, its inclusion in the monthly Patch Tuesday, and the release of a one-click on-premise fixing tool. Rolling out an automatic mitigation through MS Defender should be the final step in this effort, as there’s literally no other, more aggressive way to push a fix.
All that you need to do for the mitigation to unfold automatically on its own is to ensure that you have the latest security intelligence update on the Microsoft Defender Antivirus and System Center Endpoint Protection. That would be build number 1.333.747.0 or newer, which should have already arrived if you have the automatic updates turned on.
Of course, this mitigation is not and should not be considered equally secure as the actual Exchange security update, as it only mitigates the CVE-2021-26855. This, though, should still be enough to stay out of trouble from ransomware and other campaigns that are going rampant against vulnerable email servers right now. Again, treat this mitigation as a temporary solution that breaks the most common attack chain and not a permanent fix that you should rely on for long.
After activating and updating the Defender, the tool will automatically scan for the Exchange Server's existence and detect the version. Then, the mitigation will be deployed through a URL rewrite configuration. Moreover, the tool will scan the server for changes made by known threats and will effectively reverse them. This will happen only once per machine to avoid unnecessary over-activity.
Although cloud protection isn’t a requirement for the mitigation to work, customers are still encouraged to enable it as part of the best security practices. Finally, if you can’t use the Microsoft Defender for any reason, you may still use the one-click on-premises mitigation tool and do the job manually. It’s still a fairly simple process, so don’t postpone it any longer.