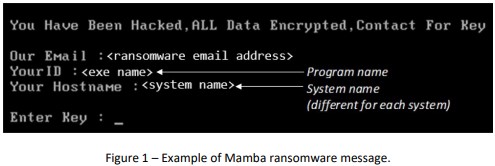
The ‘Mamba’ Ransomware Can Be Unlocked, Says FBI
- The FBI has published an alert to inform victims of the ‘Mamba’ ransomware that their files could be retrievable for free.
- The encrypter is storing a configuration file locally on the infected machine, which contains the plaintext key.
- The retrieval will only work with recent versions of the strain, as the actors are bound to update their scheme.
The FBI's cyber division has released an alert, informing victims of the Mamba ransomware strain that their files may be retrievable for free. According to the report, Mamba’s encryption process has a weak spot that could enable the victims to get the key from a locally stored file without paying a ransom.
The particular strain uses an open-source encrypter named “DiskCryptor,” which requires a system restart to install some needed libraries upon installation. This action has a time delay of about two minutes, and when the system returns after reboot, Mamba performs the encryption. This is where the victims' opportunity arises, as they have two hours before the next scheduled reboot that will wipe Mamba’s configuration file along with the decryption key.
This is named “myConf.txt,” and it’s stored under "C:\Users\Public." The file isn’t protected, and its contents are in cleartext form, so the victim may just open it and get the key. This can then be added onto the decrypter, which is bundled with Mamba, so the victims can unlock their files as if they had paid the ransom.
Obviously, the actors will now update their tool so that the file isn’t accessible or readable, and this means that victims of the Mamba ransomware can only benefit from this trick for a little while. For better security under all circumstances, take regular backups of your most precious files, implement network segmentation, keep your firmware, software, OS, and AV tools up to date, and require administration privilege for the installation of any software.
Mamba is generally targeting local governments, legal service providers, tech companies, industrial firms, commercial entities, manufacturing units, transportation agencies, and construction businesses. Certainly, the choice of DiskCryptor wasn’t ideal for the actors, especially when looking to compromise large and important entities. The particular ransomware strain has been around since at least 2016, so it’s notable that nobody has figured out the weakness before. Potentially, that particular flaw wasn’t there before.