Leadership for Educational Equity Leaks Out Data of 3.7 Million Members
- A non-profit organization dedicated to the support of disadvantaged individuals has leaked its members’ data.
- The leak occurred through an unprotected Elasticsearch database, but it is unknown if anyone accessed it.
- The database contained names and physical addresses, with all items being editable by anyone.
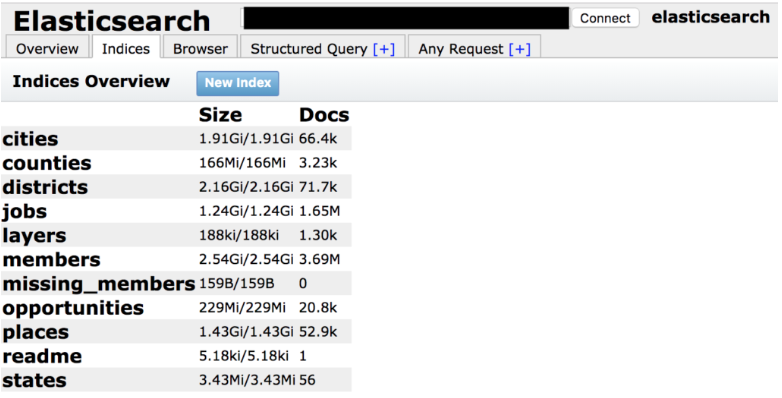
According to a report by security researcher Jeremiah Fowler, the Washington-based non-profit organization named “Leadership for Educational Equity” (LEE) has left an unprotected Elasticsearch database that contained a total of 5.2 million documents. Not having set up a password, anyone could access the database, so the researcher repeatedly tried to notify the owner via email and voicemail. The discovery took place on July 26, 2019, and after multiple notification attempts, it was secured on July 31, 2019. During his investigation, the researcher found out that the 5.2 million documents actually corresponded to the information of 3.7 individuals, members of the LEE.
image source: securitydiscovery.com
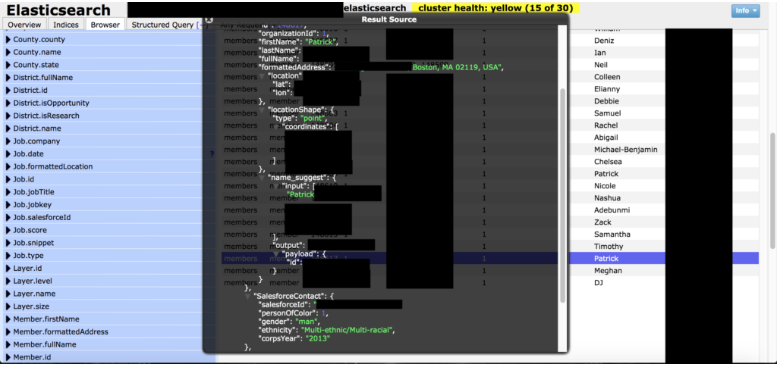
LEE is an organization that tries to support communities of lower-income, essentially helping in the fight against educational inequity. This means that their members could be disadvantaged individuals or people who volunteer to provide their support to these groups. Whatever the case, the accessible information included the full names of the people, their home addresses, their gender, ethnicity, corps year, prospect information, and their Salesforce ID. Thankfully, the database didn’t contain any medical-related information or the payment data of the members. In addition to that, the database itself was editable, contained IP addresses, ports, and pathways, so any visitor would have admin rights that would enable them to edit anything or even to dive deeper into the LEE network.
image source: securitydiscovery.com
As Fowler points out, usually, non-profit organizations fall, victims of breaches, because their resources are way too limited and don't allow the implementation of a robust cyber-security strategy. In the case of LEE, however, it looks like their high-profile donors and the reported financial resources leave no margin for excuses. LEE has everything they need to employ more IT experts, deploy data protection systems, and eventually handle their members’ data with much greater responsibility.
This is a characteristic example of an organization that simply doesn’t care about security, choose to ignore the significance of the associated risks, and betray the trust of the people who opt to deal with them. It is sad to think about how easy it is to avoid such incidents for financially powerful organizations, yet here we are reporting such stories on a weekly basis. Of course, eight days later, no official statement from Leadership for Educational Equity has been published, and it’s highly unlikely we’ll see anything like that.
Have something to comment on the above? Feel free to share your comments beneath the post, or join the discussion on our social communities, on Facebook and Twitter.