The Lazarus Group is Using a new Banking Malware Against Indian Banks
- The North Koreans are trying to steal information and money from Indian financial institutions.
- The Lazarus group has created a new custom malware that is designed to be planted on ATMs.
- No Indian banks have issued any security incident notices, so maybe there aren’t any victims yet.
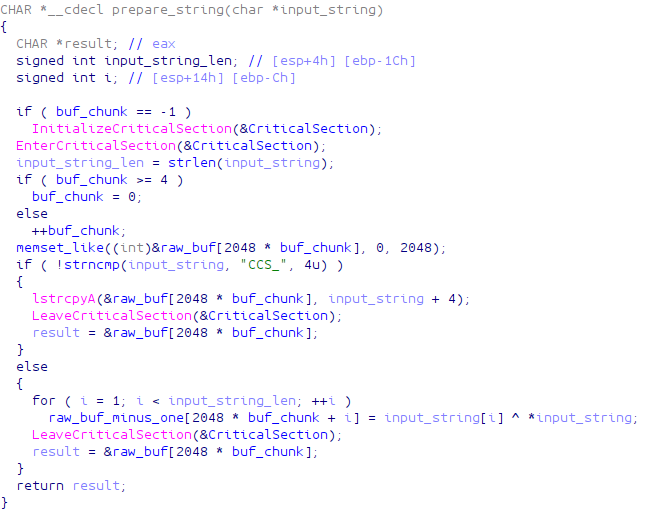
The notorious North Korean hacking group “Lazarus” is allegedly behind a new banking malware called “ATMDtrack”, and which is used against Indian financial institutions right now. The news came from Kaspersky’s researchers, who analyzed Dtrack and figured that it was designed to be planted on ATMs (automatic teller machines). Kaspersky’s telemetry shows that Dtrack was first activated at the beginning of the month, being dropped from various droppers, and featuring powerful encryption on the actual payload. The researchers managed to decrypt it and found similarities with the DarkSeoul campaign from 2013, which was also the work of the Lazarus group.
The various executables that are contained in the droppers are meant to help in the spying of the infected machine. Among the various functions that the researchers discovered, the following were the most notable:
- keylogging
- retrieving browser history
- gathering host IP addresses, information about available networks and active connections
- listing all running processes
- listing all files on all available disk volumes
Whatever data is collected is then neatly bundled in a password-protected archive that is saved onto the infected machine’s disk, or sent to the C2 server immediately.
Apart from the spying part of the attack, the droppers also contain remote access Trojans (RAT). The RAT commands that can hit the infected machines are the following:
- upload a file to the victim’s computer
- make target file persistent with auto-execution on the victim’s host start
- download a file from the victim’s computer
- dump all disk volume data and upload it to a host controlled by criminals
- dump a chosen disk volume and upload it to a host controlled by criminals
- dump a chosen folder and upload it to a host controlled by criminals
- set a new interval timeout value between new command checks
- exit and remove the persistence and the binary itself
- execute a process on the victim’s host
Source: securelist.com
We could find no cases of Indian banks having admitted a breach yet, and hopefully, their network monitoring practices have yielded adequate protection results. In addition to this, network security and password policies must remain at the absolute highest level when dealing with Lazarus campaigns. This incident shows that the North Korean hacking group continues to develop their own custom and powerful malware tools, combining money-stealing and cyber-espionage goals.
Have something to comment on the above? Feel free to do just that in the dedicated section beneath, or on our socials, on Facebook and Twitter.