‘IndieFlix’ Has Exposed 93,867 Sensitive Files via S3 Server Misconfiguration [Update]
- The “indie” film streaming service ‘IndieFlix’ has left sensitive contractor data online for five years.
- The data includes full names, signatures, addresses, emails, SSNs, Tax IDs, phone numbers, and more.
- The platform believes there has been no compromise, but this is highly unlikely to be the case.
The latest company to blunder hugely by misconfiguring its Amazon S3 server for password-less access is ‘IndieFlix,’ a subscription-based video streaming service specialized in “indie” productions, features films, and documentaries. The leaky bucket discovery came from CyberNews researchers, who found 93,867 files in the server that contained very sensitive data.
The team contacted IndieFlix immediately on July 15, 2020, but the platform failed to respond timely. On July 22, 2020, CyberNews reached out to Amazon, and after they informed the owner directly, the database got finally secured.
The data that has been exposed online includes the following:
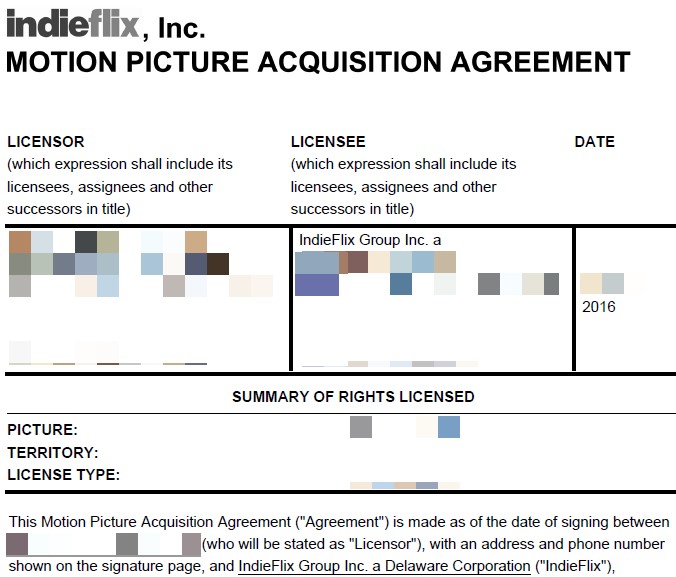
- 4,275 motion picture acquisition agreements and contract addendums
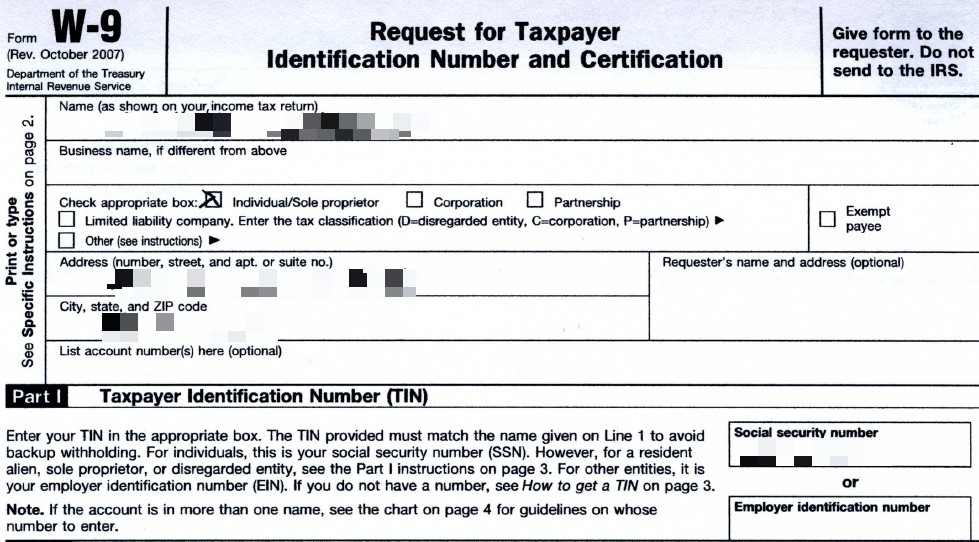
- 3,217 scans of requests for tax identification numbers that include addresses, signatures, as well as social security numbers and/or employer identification numbers of the filmmakers or their distribution agents
- A contact list of 5,966 film industry professionals, including their full names, email addresses, street addresses, phone numbers, and zip codes
- 15,225 video files, which include short films as well as clips and trailers from the platform’s Quick Pick feature library
Source: CyberNews
Source: CyberNews
From what can be deduced, no subscriber data has been exposed in this incident. However, filmmakers, distribution agents, and various professionals working in the film industry have had their extremely sensitive data compromised. Tax IDs, emails, phone numbers, street addresses, full names, signatures, and SSNs make up for a catastrophic cocktail of information that can be used for anything, from simple scams to sophisticated identity theft scenarios.
Several of these things cannot be reset, so there really is no way to effectively manage the risks other than to be very careful with incoming messages and to monitor all activities around your name. Registering for an identity theft monitoring service would also be a great idea if you’re affected by this incident.
IndieFlix eventually had communication with CyberNews and admitted that the exposed documents were uploaded to the particular server by mistake. These files were typically stored in a secure private drive, not in the AWS server, but an old backup was somehow mistakenly uploaded there. Indeed, the fact that the files date between 2013 and 2016 confirms this scenario.
As for the duration of the exposure, IndieFlix managed to trace the initial upload’s timestamp, and it apparently occurred back in May 2015. Even though that’s more than five years, the platform states that they see no signs of malicious access, but that’s very unlikely to be the case.
UPDATE: The CEO and co-founder of IndieFlix, Scilla Andreen, has provided TechNadu with the following clarifications on the present story:
- 93,867 was the total number of files in the bucket, not the number of files containing sensitive information, the vast majority of files in the bucket were thumbnails, images and other public web assets.
- The bucket was not misconfigured and was intended to be publicly accessible to deliver web assets as our CDN. It's just that a former employee uploaded an archive of files that never should have been uploaded.
- No full-length films (short films or features) were included in the quickpick library, only clips that were intended to be publicly viewable by users on our site as a way to "preview" a film to see if they want to watch it.
- We also did not receive the notification from Cybernews on July 15 because the only person contacted was our PR person who had just had a baby (early) and she was not checking emails. My email as well as a host of company emails that are public were never contacted nor was there a phone call. When we were contacted by AWS we immediately responded and remedied the situation within a few hours.