Ilia Kolochenko, ImmuniWeb CEO: Cybercriminals Are Exploiting Fear About the Pandemic
Ilia Kolochenko, Swiss cybersec expert, CEO & Founder of ImmuniWeb, knows there are risks surrounding us every time we go online. He also knows just how important it is to make sure everything is as safe as it possibly can be.
The Coronavirus pandemic has brought on new risks and new threats, as people work from home, away from the usual cybersecurity protection companies take with their own devices at headquarters.
About the security issues born by the pandemic, the risks we take, and more, we had a chat with ImmuniWeb CEO Ilia Kolochenko.
TechNadu: The world has been working from home more than ever in the past few months. How is this changing attack surfaces? What exactly is making things more dangerous now than they were before?
Ilia Kolochenko: Working-from-home has greatly affected the modern threat landscape. It is noticeable not only in a surge in the number of VPNs and RDPs but the overall proliferation of unprotected systems or uncontrolled corporate data across the Internet. Users increasingly use file-sharing services, private email accounts, and cloud storage facilities to share sensitive corporate data, without even notifying their employer. Conscientiously trying to meet their targets and not to let clients down, they unwittingly undermine organizational cybersecurity and data protection strategies.
Worse, many cybersecurity and IT teams are forcefully disrupted and have no time or free resources to address the skyrocketing number of problems. Resultingly, a not insignificant number of business-critical systems remain unmaintained, unpatched and vulnerable, opening the door to a corporate's Crown Jewels.
TechNadu: What steps should companies and employees be taking to protect their data?
Ilia Kolochenko: Continuous and holistic visibility of your digital and IT assets, data, and users is the right place to start. You cannot protect what you don't see. Once you possess an up to date and inclusive inventory, it is essential to develop and implement a continuous, consistent, and risk-based cybersecurity policy and concomitant procedures.
Security awareness training is likewise imperative as human error and carelessness top the list of most dangerous threats. All of the data protection and cyber resilience procedures should be regularly reviewed and, if necessary, improved on a continuous basis, while all the stakeholders should be quickly informed about such updates. Finally, a well-thought third-party risk management program, including suppliers and vendors with privileged access to your data or systems, is an indispensable element to keep your Crown Jewels safe and secure.
TechNadu: The dark web is teeming with credentials from companies all over the world. How are these used by cybercriminals, and what are the risks for both individuals and companies?
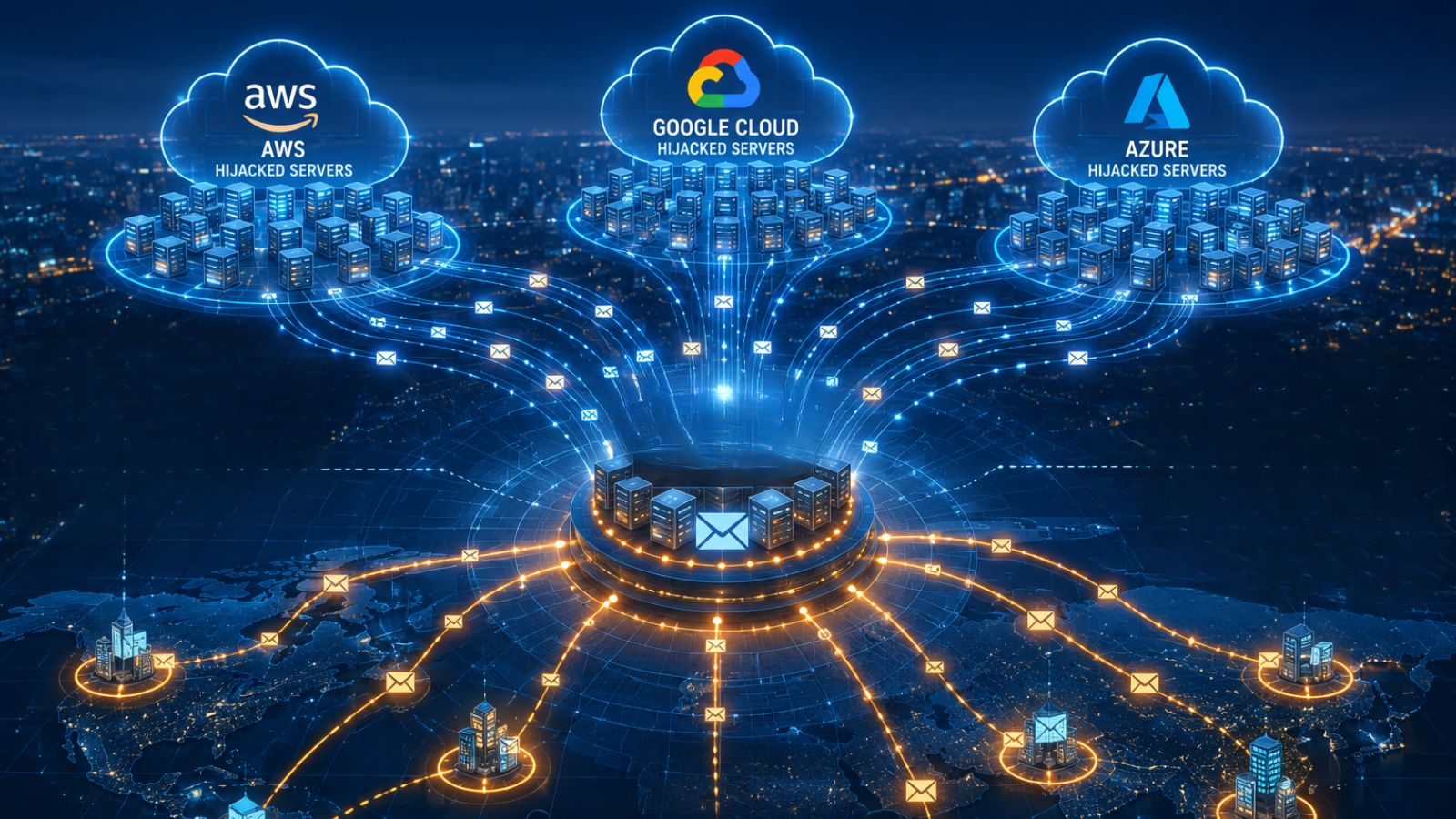
Ilia Kolochenko: We conducted research late last year and found that found over 21 million (21,040,296) credentials belonging to Fortune 500 companies, amid which over 16 million (16,055,871) were compromised over a 12 month period, and these figures are probably not going to decrease any time soon.
Cybercriminals incrementally target third-parties that have privileged access to the data they seek, instead of running frontal attacks against the victims. Acquisition of stolen credentials on the Dark Web and consequent password re-use attacks are formidable vectors of indirect intrusion tactics, rapidly gaining popularity and unprecedented success. It may be sufficient to buy one single account with privileged access to a business-critical system, and the integrity of your data protection efforts vanish. Worse, such attacks are hardly detectable, given that the organization is not hacked and technically cannot detect any anomalies.
To help more entities to understand their status in the Dark Web, we just launched a free online test that enables enterprises, governments, and organizations of all sizes to rapidly illuminate and assess their current exposure. Our monitoring of the Dark Web includes mushrooming hacking forums and underground marketplaces, dedicated IRC channels and Telegram chats, paste-websites, and many other locations in Deep, Dark, and Surface Web.
TechNadu: How do you feel things have changed since the pandemic started? Do we see a spike in threats? Is there more online criminal activity?
Ilia Kolochenko: Cybercriminals are aggressively exploiting fear and uncertainty about the pandemic, luring even the most experienced users into clicking on phishing links or sending out valuable information. BEC and whaling attacks were practically successful during the last few weeks.
TechNadu: What are the areas where you've noticed companies need to work more to protect themselves? Are there common chinks in armors?
Ilia Kolochenko: Lack of visibility, insufficient or otherwise flawed enforcement of existing cybersecurity policies, security procedures that are inconsistent or insufficiently promoted amid stakeholders, and ignorance of cloud and third-party risks dominate the multitude of the modern-day chinks in the armor, and they are aptly pierced by shrewd cybercriminals.
TechNadu: Given the security issues tied to IoT devices, how do we pick the right ones to take into our homes? Are there any extra precautions we should take?
Ilia Kolochenko: Pick a trusted global vendor; usually, they do care about robust security compared to cheap brandless models. If a device's price is too good to be true, it likely is so. Ensure that the device has an auto-update mechanism and is supplied with a comprehensive privacy and data protection terms and conditions.
TechNadu: Children these days grow up online, which exposes them to a long list of risks. How should the issue be approached by parents? Are parental controls the solution to this problem?
Ilia Kolochenko: Unfortunately, most of the efforts aimed to protect our children from violent, inappropriate, or adult-oriented content eventually fail in one manner or another. Thus, on top of the foundational technical controls (e.g., activating content filtering on devices, browsers, and websites), educational efforts are required to mitigate the impact of harmful content your kid will inevitably watch sooner or later.
TechNadu: When it comes to personal security, what are the most important steps people need to take, in your opinion?
Ilia Kolochenko: Individual users should maintain their mobile devices, computers, and the integrity of the installed software up to date. Using unique and strong passwords is a must, while activation of 2FA, when available, will never hurt. Any unexpected incoming messages that leverage urgency, emotions, or threats should be meticulously scrutinized as most of such messages are aptly crafted phishing campaigns.