How To Use PGP Encryption for Secure Communication
Have you ever needed to tell someone something desperately, but were worried that someone other than the intended target might read it. Maybe you also don't want the recipient to know you are for one of many reasons. What can you do?
Speaking in Tongues
The answer is encryption! We've spoken about this topic frequently on TechNadu, but I'll do a little recap of what encryption is here for convenience.
Basically when you encrypt something you run the text of the message through an algorithm that scrambles it. The resultant text is basically just gibberish. If you've ever learned pig latin or letter substitution you already know some encryption.
The problem, of course, is that those forms of encryption are symmetric. In other words, the method you use to encrypt the information is the same you use to decrypt it. In other words, this is only secure if both the sender and receiver never share the key with anyone else.
These days we use something called asymmetric or public key encryption. Here the key to encrypt and decrypt are different. The receiver never shares their decryption key. However, anyone who wants to send them a secure message can use the public key which doesn't have to be a secret. To send someone a piece of encrypted text via email securely the easiest way is by using a technology known as "PGP".
What's PGP?
"PGP" is short for pretty good privacy. Don't let the name fool you though. This free and open encryption technology is some of the most secure available to the public. Even intelligence organizations like the NSA haven't cracked it yet. At least not as far as anyone knows. Privacy folk hero Edward Snowden even reportedly uses it when communicating with reporters and such.
PGP started as a commercial program released in 1991. Since then we've seen the rise of open license versions of the technology and various programs that will do the job of encrypting your text.
For a long time, no one except a few hardcore privacy people knew about it. These days however just about every journalist has a public PGP key plastered on their Twitter account. So let's look at how you can use PGP to secure your own email.
How to Use PGP
The first thing you want to do is get a PGP software package for your operating system For Windows GPG4Win is a popular choice. Mac users seem to like GPG Tools, but since I'm on a Windows system I'll be using GPG4Win in the examples.
Many guides on PGP will take you through a long process of installing a desktop email client and then install plugins to automatically encrypt or decrypt emails. I'm not going to do that here for a couple of reasons.
First of all, using a desktop email client is a little extreme if you only want to send an encrypted message every now and then. Secondly, I want to make this introduction to using PGP simple. So all we'll do here is to encrypt plain text using our own public key. Then we'll decrypt that same text using the private key. This should demonstrate the principle and allow you to create encrypted text using someone else's public key.
Another advantage of doing this is that you can send the encrypted text via an anonymous email service. Instead of using your real email address, which can be tracked back to you. Something you want if the communication is meant to be one-way.
Step 1 - Creating Your Key Pair
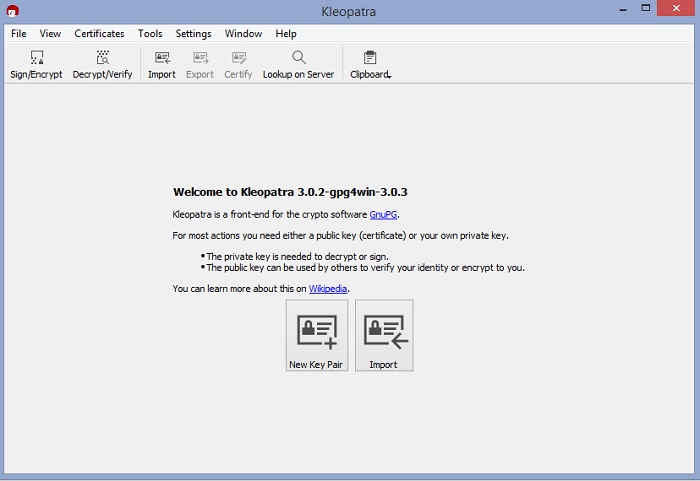
After installing GPG4Win you need to launch Kleopatra. Which is the graphical front-end for the software? When you first do this you'll see this screen:
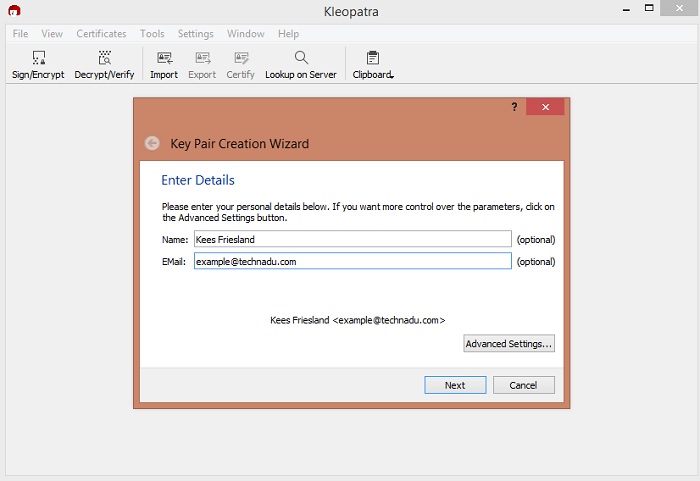
Click on "New Key Pair" then enter your name and email address. Obviously, you can enter false info as well or just nothing.
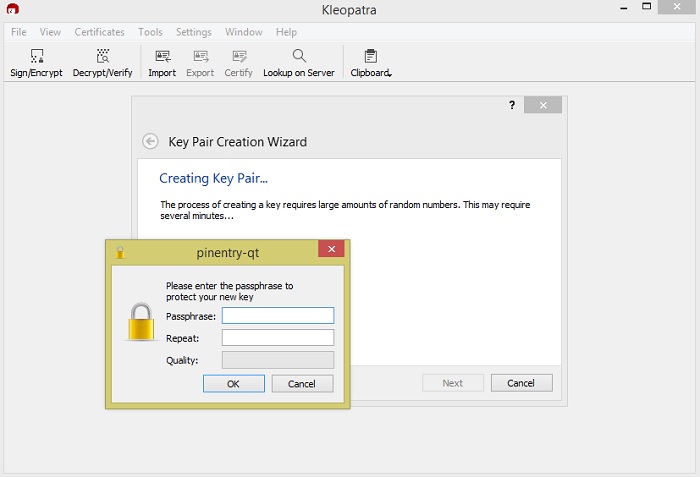
Once you've done this just click the create button and you will be prompted to create a passphrase. Come up with a good one and remember it or store it in a safe place.
Once it's all done you'll be presented with a window where you can make a backup of your new key, send out the public key by email or upload it to a keyserver so that people can look it up and send you encrypted messages.
Step 2 - Encrypting Text Using a Public Key
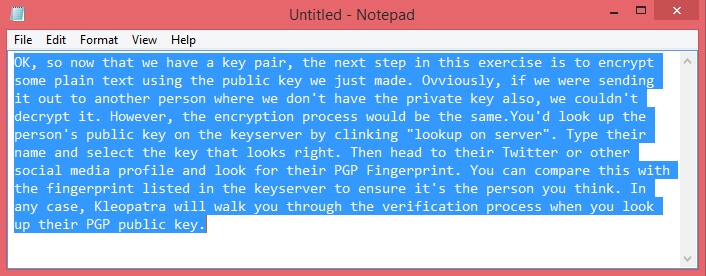
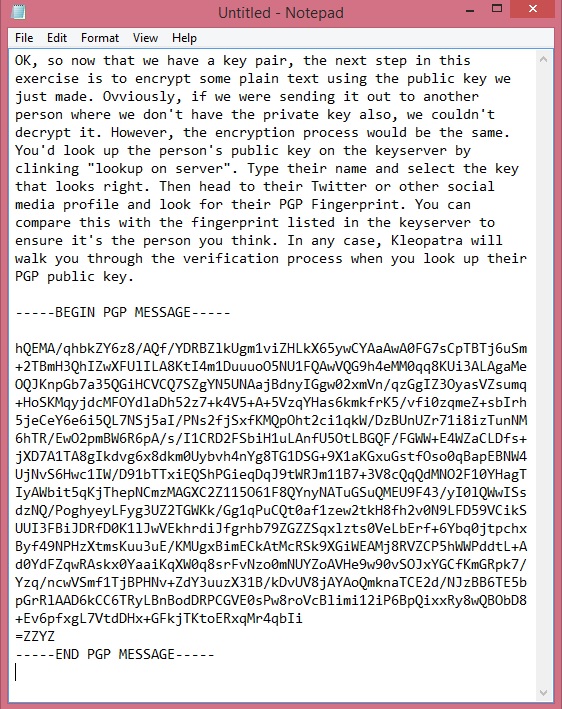
OK, so now that we have a key pair, the next step in this exercise is to encrypt some plain text using the public key we just made. Obviously, if we were sending it out to another person where we don't have the private key also, we couldn't decrypt it. However, the encryption process would be the same.
You'd look up the person's public key on the keyserver by clinking "lookup on server". Type their name and select the key that looks right. Then head to their Twitter or other social media profile and look for their PGP Fingerprint. You can compare this with the fingerprint listed in the keyserver to ensure it's the person you think. In any case, Kleopatra will walk you through the verification process when you look up their PGP public key.
Here we're going to copy text from notepad into the clipboard.
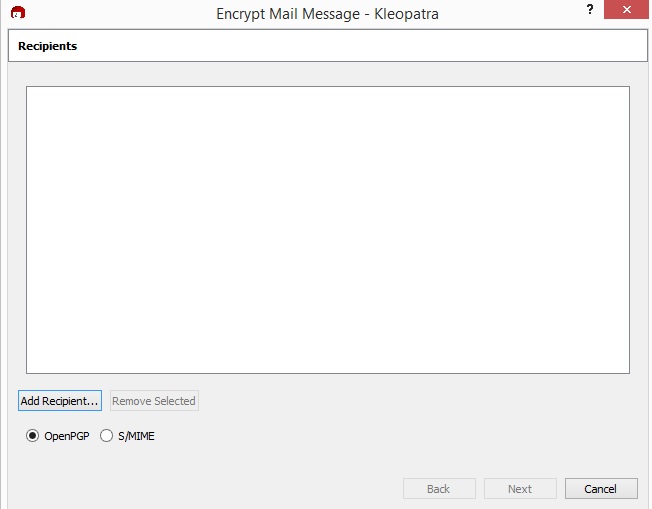
Then, in Kleopatra, click on clipboard>encrypt. You'll see this screen.
Click "add recipient" and select yourself for the purposes of this demo.
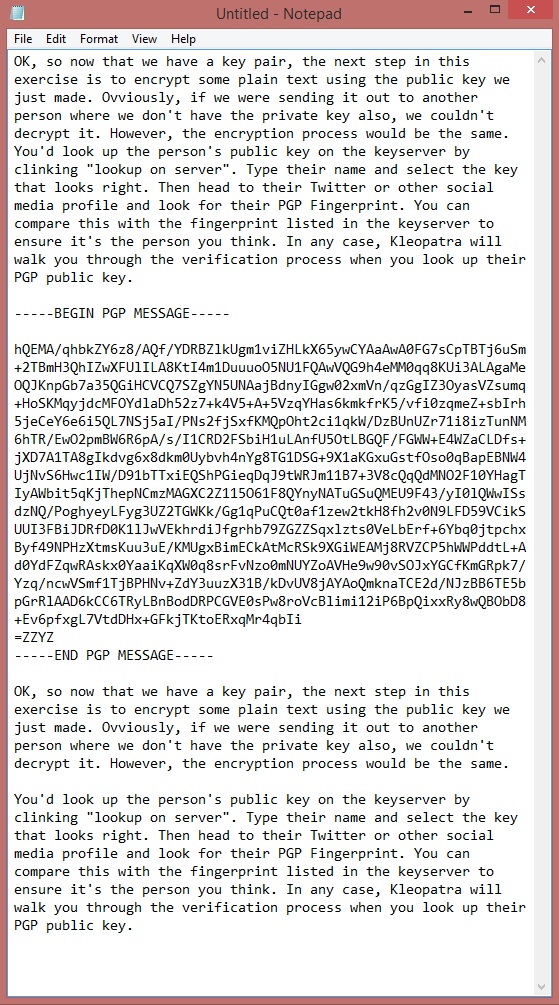
After completing the encryption you can paste the text in the clipboard back into the word processor. Here you can see the original text and encrypted text next to each other.
If this were meant for another recipient, that's the text you'd put in the email body. Since we sent this to ourselves, let's look at the decryption process.
Step 3 - Decrypting Text Using a Public Key
This is the same as step 2, just in reverse. Copy and select the entire encrypted text block, including the "begin" and "end" lines.
Now click on clipboard>decrypt/verify. You'll be prompted for your passphrase. Enter it and you should see the original text.
This is the process you'd follow to decrypt text sent to you that had been encrypted with your public key.
Keep It Secret, Keep It Safe
That's the core method for using PGP to secure a text body. Which you can send via email or any other transmission method that can handle plain text. As you can see, it's pretty simple if you do it this way. Without more than the minimum software in the way. PGP provides a great way to securely communicate either openly or anonymously without needing a degree in cryptography.