Holiday Mobile Threats Surge During Shopping Season, Report Finds: Phishing and Malware Risks Escalate
Key Takeaways
- Phishing spike: Mobile phishing campaigns increase by up to 4x during the holiday shopping season, often impersonating retail and shipping brands.
- Malware evolution: Banking trojans and remote access tools are increasingly targeting mobile shopping and payment apps to steal credentials and financial data.
- App flaws: Top shopping apps have security risks, including the ability to load remote code, unprotected components, and vulnerable third-party libraries.
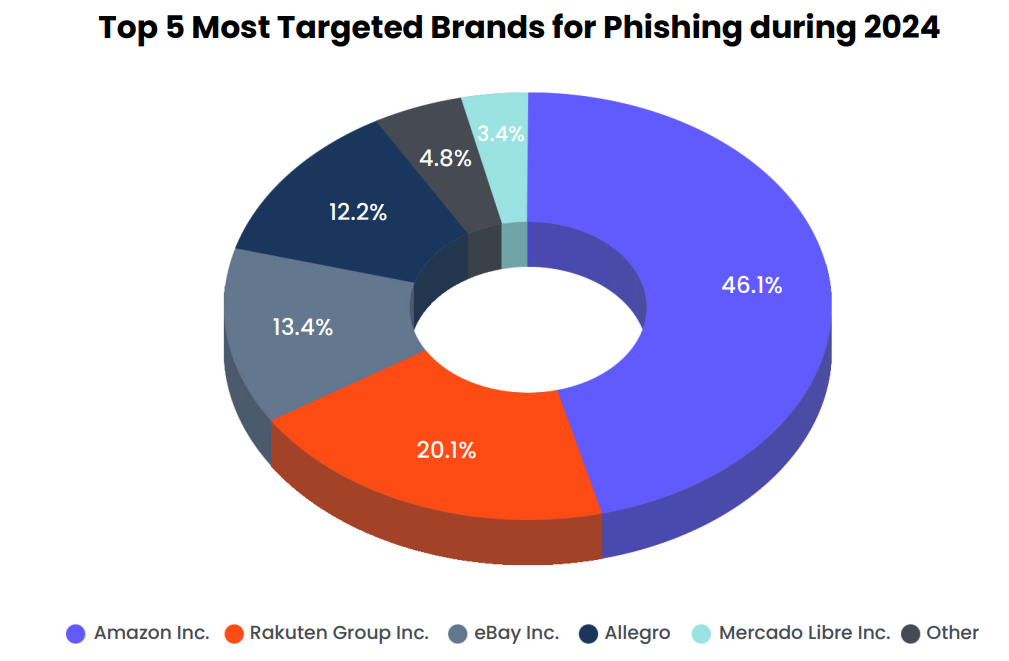
Holiday mobile threats surge as cybercriminals intensify their activities to coincide with peak retail periods like Black Friday and Cyber Monday. Threat actors leverage trusted brand names like Amazon and major shipping carriers to create a sense of urgency, deceiving users into clicking malicious links designed to steal credentials or download malware.
Malware and Mobile App Vulnerabilities Widespread
A new analysis from the Zimperium Mobile Shopping Report identifies mobile phishing (mishing) as the most immediate and scalable threat, with observed activity surging by up to 400% during the holiday season.
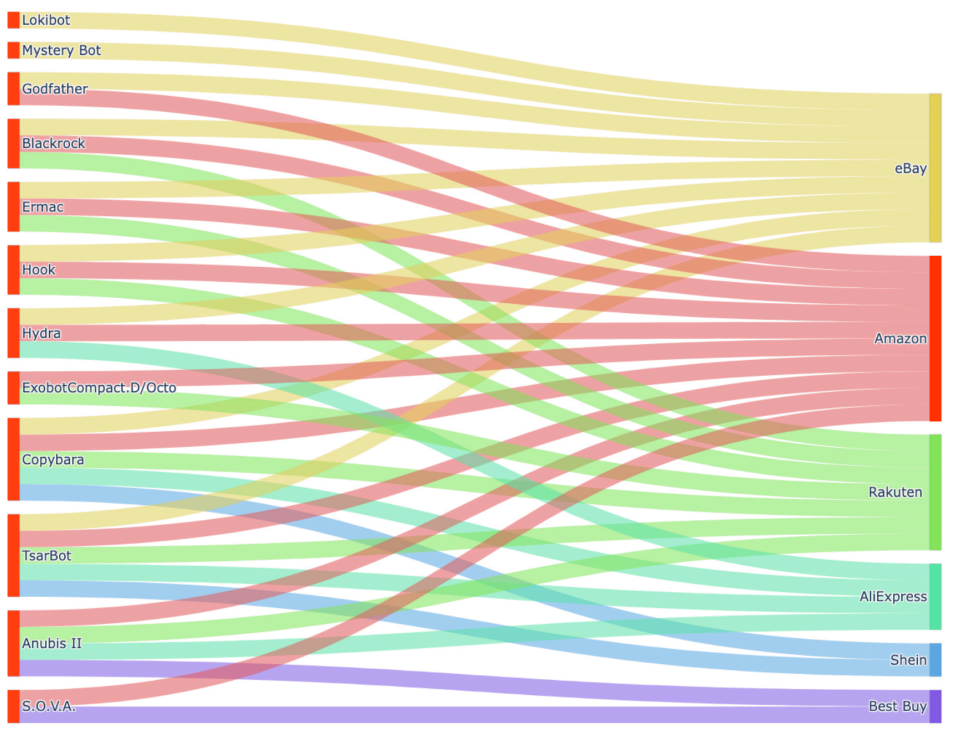
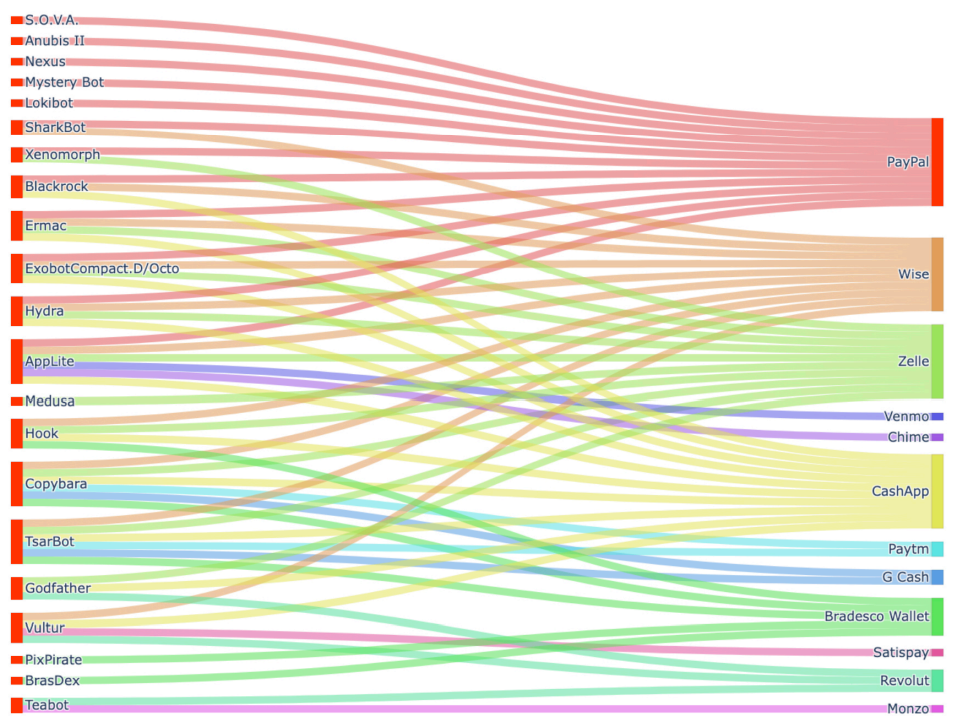
Beyond phishing, the report details the evolution of malware targeting mobile commerce. Banking trojans are increasingly adapted to attack popular shopping and digital wallet apps, using overlay attacks to capture credit card information and one-time passwords.
Analysis of prominent shopping apps revealed that many are targeted by malware families such as Copybara and TsarBot. Furthermore, the report uncovers significant mobile app vulnerabilities even in legitimate, top-ranked applications.
Of the top 100 Android shopping apps analyzed:
- Nearly 24% could load executable code from remote locations,
- 19% exposed unprotected components, creating pathways for data leakage or unauthorized operations.
- 14% have implicit activity vulnerabilities that may let attackers access arbitrary files
- 11% of Android apps were found to be signed with weak APK Signature Schemes
“As mobile and enterprise ecosystems converge, security teams must treat the holiday season as a critical risk window, not just for consumers, but for the business itself,” said Ignacio Monta, SVP, Strategy & Threat Intelligence at Zimperium.
Supply Chain and Enterprise Exposure
These vulnerabilities pose a serious risk not just to consumers but to enterprises as well. For example, one popular shopping app with over one million installs was found to contain a third-party SDK capable of secretly exfiltrating user data and remotely executing new code, effectively creating a supply chain compromise vector.
“One critical but often overlooked aspect of online security is the role of digital certificates that power the secure connection between shoppers and retailers,” Nick France, Chief Technology Officer at Sectigo, said.
For enterprises, employees using personal devices for work can inadvertently introduce these threats into corporate environments, according to Mika Aalto, Co-Founder and CEO at Hoxhunt.
“As we humans begin to let agents shop on our behalf, it will leave retailers one step removed from their human customers,” said Will Glazier, Head of CQ Prime Threat Research Team at Cequence Security. “The applications and agentic frameworks humans will delegate their shopping experience to will be vulnerable to the same type of spoofing that we see currently, where malicious actors impersonate trusted brands or applications.”
“This year, we’re guaranteed to see ever more sophisticated scams, primarily fueled by artificial intelligence, whether that be convincingly forged order confirmations, spoofed retailer sites, and even AI-generated customer service messages designed to steal login details or payment information,” said Anne Cutler, Cybersecurity Evangelist at Keeper Security.
Both consumers and organizations need to prioritize strengthening their defenses. Cutler recommended:
- The use of strong, unique passwords and Multi-Factor Authentication (MFA) on all accounts. Reviewing privileged access controls,
- Ensuring employees are trained to spot social engineering attempts
- Monitoring for unusual login activity throughout the Black Friday period.
“Users should be on high alert to what applications/sites they use for shopping, especially during the holiday shopping excitement,” added Nivedita Murthy, Senior Staff Consultant at Black Duck. Meanwhile, earlier this year, TikTok, AliExpress, SHEIN, Temu, WeChat, and Xiaomi were accused of sending data from the EU to China.