Half a Million Zoom Accounts Are Currently for Sale on the Dark Web
- A large number of Zoom account emails, passwords, and personal meeting URLs are currently shared on the dark web.
- Hundreds of accounts are given away for free, as actors are having fun by zoom-bombing meetings.
- The passwords were figured through credential stuffing attacks, so this time it's the users' fault.
Only a week after we reported about 352 Zoom accounts being shared on the dark web, news about a much bigger dump appeared. Cyble, a cyber-risk intelligence firm that specializes in early breach detection and dark web monitoring, is reporting that they have located the sale of 530,000 Zoom accounts on hacker forums and marketplaces. In some cases, Zoom accounts are shared with other users for free, as the whole dark web community is having fun with pranks and zoom-bombing. The cost of those that are sold is very low anyway, set at $0.002 per item.
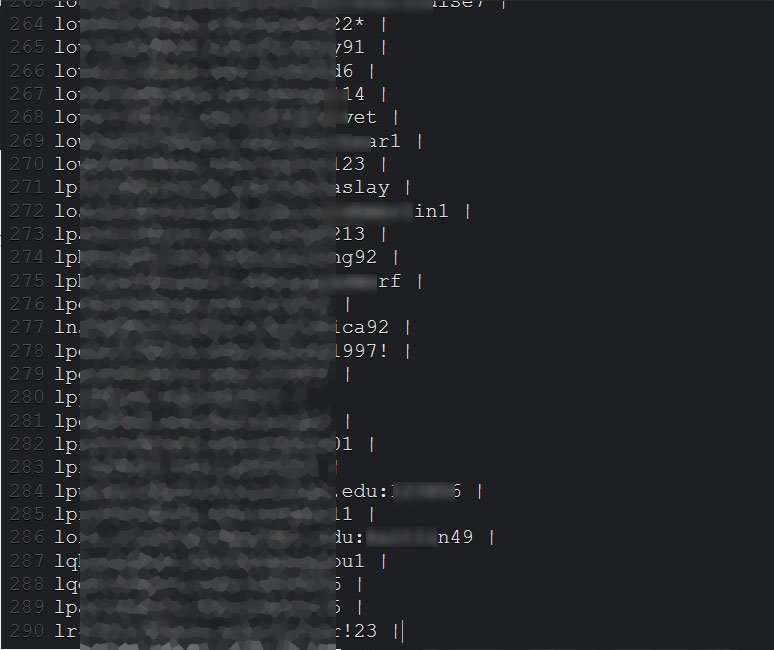
The account credentials are shared in Pastebin platforms containing hundreds of email addresses and passwords in plaintext form. In other cases, there are bulk sales concerning packs that contain up to 530,000 account credentials, host keys, and personal meeting URLs, priced at $1060. As for whether these credentials are valid or not, Cyble's random tests have confirmed that the emails and passwords are indeed working on Zoom. However, in some cases, users have already reset their passwords. So there's a chance that some entries contain older and invalidated passwords. Cyble is already sending warning emails to its customers, so if you have been breached, you will receive an email soon. If you're not their customer, check your email on the HaveIBeenPwned service.
Source: Bleeping Computer
Source: Bleeping Computer
The question that arises is how did the actors get their hands on these credentials in the first place. One way would be a security breach on Zoom's systems, but there's no indication of anything like that had happened. Most likely, these sold credentials are the product of successful stuffing attacks. It means that the compromised individuals were using the same passwords in other online platforms, the data was leaked previously, the hackers tested them on Zoom, kept what worked, and filtered out what didn't.
If you have set a password on Zoom that you have been using on other services or websites, go ahead and reset it immediately. While Zoom has been at the epicenter of criticism lately, this incident has nothing to do with the teleconference platform's security, and it's totally the users' fault this time. Utilizing the same passwords everywhere is a sure way to get yourself compromised sooner or later, so you should use a password manager.