Hacker Group Magecart is Still At Large According to Report
- The Magecart campaign that was responsible for hacking into British Airlines is still active according to a report.
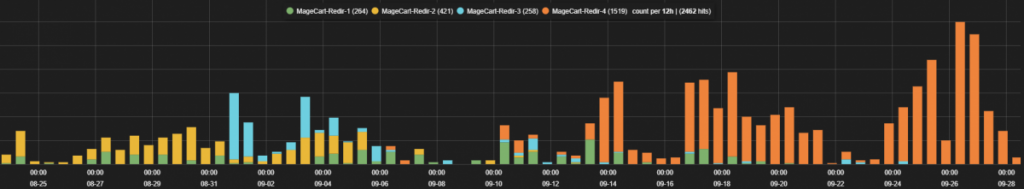
- Zscaler ThreatLabZ is actively tracking the Magecart campaign for months.
- The hacker group is known to inject websites with malicious JavaScript code that steals transaction data.
Hacker group Magecart is still active despite a number of successful exploits posted into e-commerce websites and more recently, the British Airways. The notorious group is known to skim websites using JavaScript code for stealing payment card data by tapping into transactions.
The obfuscated code created by Magecart makes it difficult for websites to track any malicious activity. Code obfuscation is a popular method that is used by many cybercriminals as it allows them to disguise malicious code in seeming harmless payment portals on official websites. With e-commerce websites unable to prevent the obfuscated code from being injected into their websites, it has become a global security problem for all affected companies.
Image Courtesy of ZScaler
Magecart is capable of creating fake forms on ecommerce websites that mimic an official payments page. These payments pages are created using the Document Object Model (DOM) properties which are capable of stealing credit card details, personal information of users, details about the website domain and more. A POST request is made by the attackers once enough data has been collected which causes the JavaScript to upload the data to private services owned by the hackers.
According to ZScaler, the attacks are becoming more creative by the day, and credit card skimming is becoming a huge problem. The hacker group has conducted a number of large-scale attacks. ZScaler stated that “Magecart has been responsible for large-scale attacks on well-known brands, and the ThreatLabZ team will continue to monitor its activities to ensure coverage for Zscaler customers.”
ZScaler revealed that the number of campaigns has been increasing and newer domains are being constantly exploited. Most of Magecart’s targets include e-commerce websites. The domains of the fake payments pages hosted by the hacker group are hosted on AS24936 Moscow, which narrows down the location of the hackers to Russia.
What do you think about Magecart actively targeting e-commerce websites all over the world? Let us know in the comments below. Also, to get instant tech updates, follow TechNadu’s Facebook page, and Twitter handle.