145 Google Play Store Apps Infected with Malicious Microsoft Windows Executable Files
- Palo Alto Networks identified 145 instances of infected Google Play Apps that contained compromising software usable for large-scale cyber-attacks.
- The infected APK files on the Play Store did not pose any threats to Android users but running them on Windows systems could lead to malware infections.
- Such infections are reported to be hazardous to software supply chains as they are not easily detected by Google.
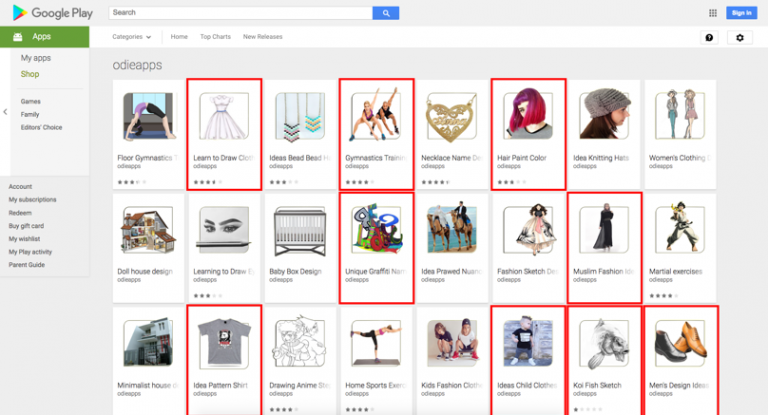
Next time you download an app from the Google Play Store with a high rating and a large number of downloads, it may not be as safe as you think. Security research company Palo Alto Networks conducted a scan on apps in the Play Store and identified 145 apps that are infected with malware. Google’s security team has already removed all of the flagged apps. Even recently they banned cryptocurrency mining apps in a bid to secure the platform. The findings are similar to a previous test conducted by Palo Alto in 2017 which returned 132 infected apps on Google’s online store.
Image Courtesy of Palo Alto
Google’s security features scan the apps for malware or other malicious code which may affect Android devices. However, checks to see if the apps pose any threats to other platforms are not done, making it easy for cybercriminals to inject Windows executable files into Android apps. The executables can create hidden files in Windows system folders and copy themselves, make changes to the Windows registry, put a PC to sleep for an extended period of time and initiate suspicious network activities.
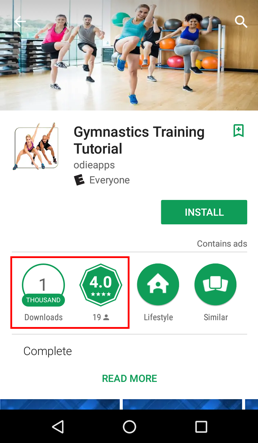
Image Courtesy of Palo Alto
This kind of malware design can be detrimental to the software supply chain as compromising mobile development platforms like Android or iOS to target desktop-based platforms has proven to be an effective tactic. With the release dates of the recently identified apps dating back to October 2017, more than half a year has passed with the apps being present on the Google Play Store.
The security firm revealed that developers often had a mix of infected and non-infected apps, hinting at the fact that developers often use different development platforms for their apps. With Google having no control over the development platforms that are used for producing Android apps for the Play Store, so security countermeasures by the tech giant can turn out to be useless. It is up to the developers and the development platforms to secure their software, which is hardly the case according to Palo Alto’s recent research.
What do you think about the vulnerabilities found in the Play Store apps? let us know in the comments below. Also, to get instant tech updates, Follow TechNadu’s Facebook page, and Twitter handle.