Gearbest Server Leaking Millions of Highly Critical Customer Data
- An unprotected Elasticsearch database belonging to Gearbest is giving malicious actors everything on a plate.
- From personal identification information to banking data and payment vouchers, there’s nothing that's missing.
- The vast majority of the information was unencrypted, while a Kafka misconfiguration allowed anyone to change anything.
Noam Rotem, a white hat hacker and cybersecurity specialist discovered an unprotected Elasticsearch database belonging to Gearbest, that leaks customer data continuously reported by VPNMentor. The discovery occurred in the start of this month, but Gearbest are yet to respond or secure it, so anyone who wants to access it may do so and receive real-time customer additions as we are writing this. This admittedly sounds extremely irresponsible for the Chinese e-commerce company which happens to be one of the largest and most successful in this field around the globe, shipping to 250 countries, and ranking in the top 100 websites in 30% of those countries.
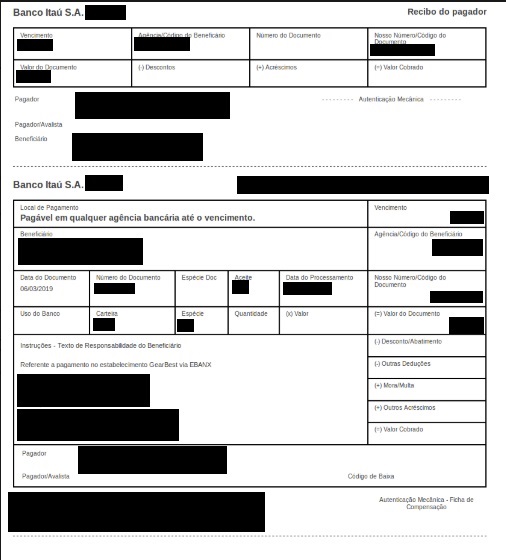
The customer data that is exposed through the unprotected database includes everything that a malicious actor could have possibly ask for, like the full names and addresses of the customers, the phone number and email addresses, the products that were purchased, the payment methods that were used, and even the invoice information that accompanied each order. In several cases, the database contained the active bank payment vouchers used by customers in Mexico and Brazil, with the unique barcodes being unmasked. This means that someone could use this information to act as the owner of the bank account.
source: vpnmentor.com
According to the researcher, nothing in the database was encrypted, which shows a bad practice from Gearbest’s side. Even if the database wasn’t left open to access, the user information should be encrypted so as to protect it in case of a breach. Taking advantage of this lack of fundamental security, the researchers have logged in to two Gearbest accounts picked at random, and could have easily taken them over by changing the password. Another alarming discovery was that the path to identity theft was paved with rose petals in several cases. User data that was found in the database includes the national identity number, and in some cases, even the health insurance records and credentials to access online government portals. That goes well beyond than what we’re used to seeing in stories like this one, and someone would wonder if it could get any worse already.
source: vpnmentor.com
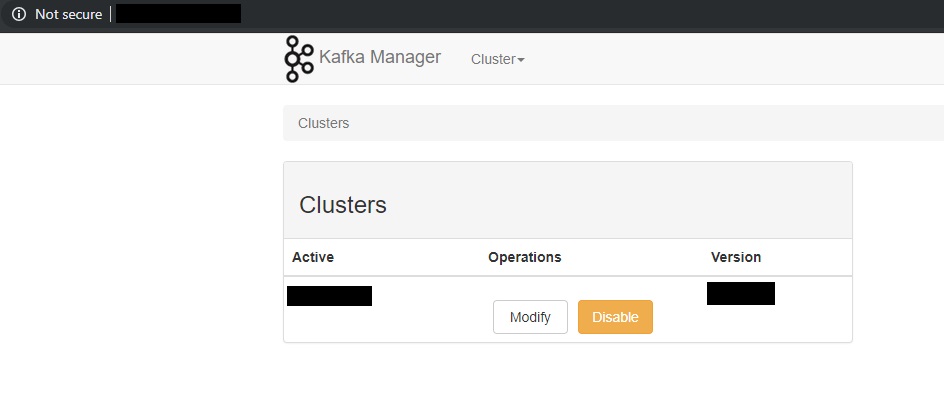
As it seems, it can, as the Kafka data management system that is used for the database has been wrongfully implemented, allowing visitors to manipulate its contents, reassign database properties, and arbitrarily disable server sections. This means that anyone can enter the database and fiddle with the stock data, order placement data, and anything else that they want.
Have you ever purchased anything from Gearbest? Would you trust them again in the future? Share your thoughts in the comments section beneath, and help us spread the word by sharing this story through our socials, on Facebook and Twitter.