Fundraising Platform ‘WeDidIt’ Exposes 7.5 Million of its Donors
- WeDidIt blundered by leaving a live “production” database exposed to the public.
- The database contained the PII of 7.5 million donors and was modifiable and fully exploitable.
- No official announcements were made about the incident, and the exposed people probably don’t even know about it.
Another day, another story of an unprotected database seeing the light with no official statements from its owner and administrator. Security researcher Jeremiah Fowler has discovered a database that didn’t use password protection on July 11, 2019. Upon further investigation, the researcher discovered that the owner of the database was “WeDidIt”, a fundraising platform which enjoys high popularity and counts many thousands of donating members. While the company didn’t make any relevant announcements on their blog or their social media, at least they were quick to respond to the notification and secured the unprotected database in a short time.
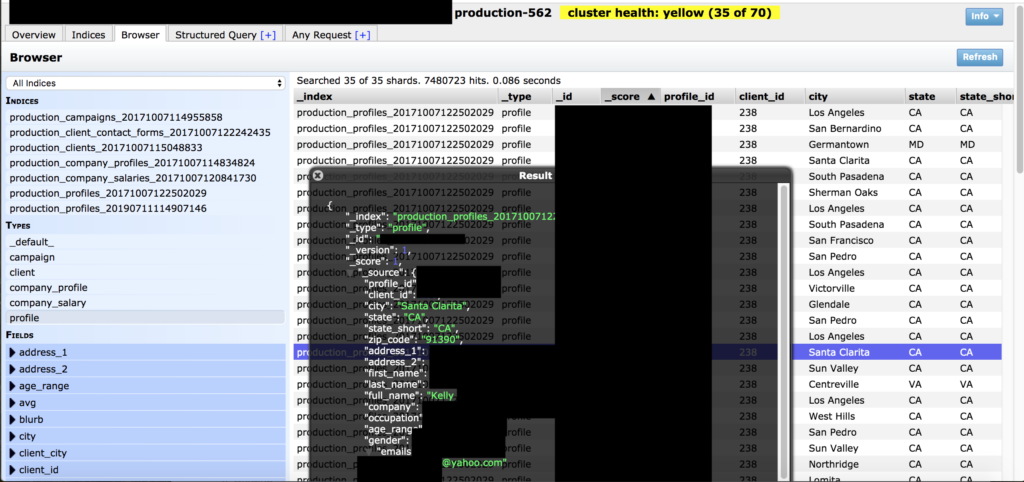
The exposed database contained 7.5 records that included the full names of the donors, their user account IDs, their home addresses, and their email addresses. The folders were tagged with the “production” flag, which means that the database was live and serving the crucial operations on WeDidIt. As the database was completely unprotected, an outsider could have taken it over to modify its contents, and from there find a way inside the internal network of the fundraising platform. Alarmingly, the required information for this action like the IP addresses, ports, and pathways was there and available.
image source: securitydiscovery.com
As no official comment was provided by WeDidIt to the researcher after all this time, the duration of the exposure and the reason for the erroneous configuration remains unknown. Moreover, there’s no indication that the authorities were informed about the security incident, nor that the affected members of the platform have been notified with an email. Based on the number of people who have been exposed by this incident as well as the type of the data and the level of its sensitivity, this is a grave occurrence that should have already made the cogs of the investigation turning.
WeDidIt is a New York-based company that was founded in 2012 and has grown exponentially since then. The campaigns mainly deal with nonprofit crowdfunding, but there are also software-development backing projects as well. As crowd-sourcing becomes increasingly popular, donors should be careful with the companies they trust, and this exposure highlights the risks that come with trying to support a good cause. Crooks have their eyes fixed to where the money is, so databases like this one are actively searched for, not just stumbled upon. In the occasion of WeDidIt, let’s just hope that the case was somehow the latter and that Fowler was the first outsider to access it.
Have you made a donation through WeDidIt? Did you receive any notifications about a security breach from them recently? Tell us in the comments below, or on our Facebook and Twitter pages.