A Flaw in Qualcomm’s Modem Component Affects 30% of All Smartphones Out There
- Researchers found a high-severity bug in the Qualcomm chip modem communication protocol.
- The flaw could enable the execution of arbitrary code following a memory corruption event.
- Qualcomm has pushed the fixing update, but smartphone vendors will have to push it downstream.
Researchers at Check Point have discovered a flaw in Qualcomm’s MSM (Mobile Station Modem), tracked as “CVE-2020-11292”, and which is present in approximately 30% of all mobile phones in the world. While the potential for exploitation or its scope isn’t clear right now, the path to do it is through QMI, which is Qualcomm’s proprietary communication protocol linking the modem’s software with all other peripheral subsystems of the device.
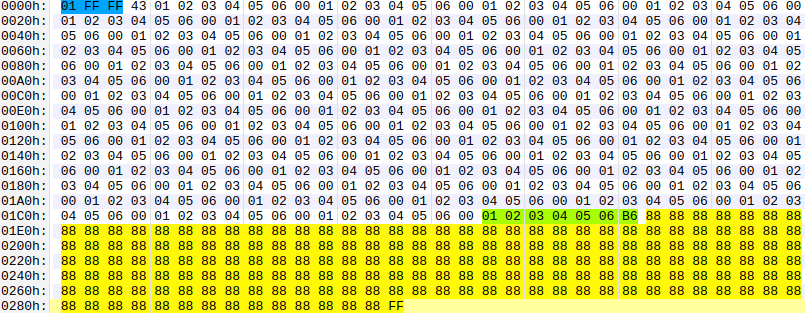
The trick is to create a TLV packet containing a payload that would trigger a buffer overflow condition, allowing the attacker to send a reboot action on the target modem, or inject malicious code into it, proceed to access sensitive data on the device, snoop communications, and more. Even the action of unlocking the SIM is included in the possibilities of the exploitation spectrum, which would enable the attacker to bypass any limitations imposed by the provider. The researchers have skipped exploring all exploitation possibilities, but the above are indicative enough.
Normally, no third-party apps have permission to use QMI. Still, the researchers found another way through radio or media reaching the device - or even through privileged users who have access to the service. So, the TLV packet that would trigger CVE-2020-11292 could reach the device in the form of a video, for example, requiring nothing other than a mere playback.
The researchers found this bug by reverse-engineering Qualcomm’s protocol and following a feedback fuzzing method. The first bug report and a proof-of-concept example were sent to Qualcomm on October 8, 2020. Qualcomm realized the importance of the finding quickly and gave the vulnerability a high criticality rating only a week after. However, addressing the issue is complicated.
You see, Qualcomm has released a fix and pushed it to mobile vendors, but QMI fixes must be implemented by them now, and we all know how incompetent the Android world is at that. Every smartphone maker uses its own implementation of the QMI protocol, sometimes adding services on top of what’s provided as default by Qualcomm - so patching isn’t a “plug it in” thing.