Fake NordVPN Website Infects Victims With Banking Trojan
- Known group of malicious actors has refreshed its banking trojan campaign by using new websites.
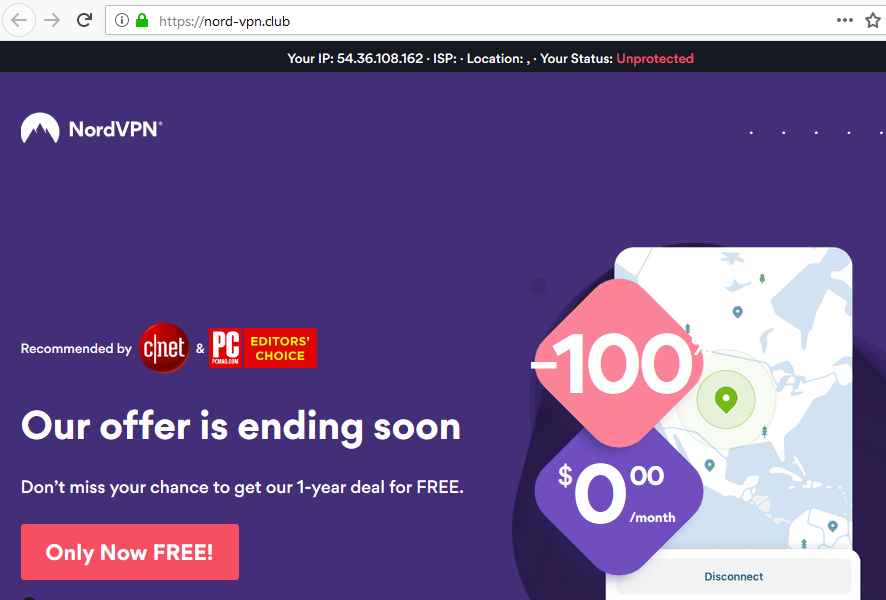
- The actors have created clone websites of NordVPN and other products, infecting systems with Bolik.
- The websites look very convincing, have similar URLs with the original ones, and carry valid SSL certificates.
According to a report by Dr. Web Antivirus researchers, the same actors that have compromised the website of the VSDC video editor to push trojans in April are now using a clone of the NordVPN website to do the same. The banking trojan that is distributed in the particularly dangerous “Win32.Bolik.2”, which is a multi-component virus capable of traffic interception, keylogging, code injection, and data exfiltration. To make things worse, the cloned website doesn’t only look very similar to the authentic one, but it also features a valid SSL certificate and its domain name looks legit at a first glance.
Decoy site, image source: news.drweb.com
Dr. Web has logged the first signs of the campaign's activity going back to August 8, 2019, and the fake website has already had thousands of visitors. However, the actors aren’t using only NordVPN for hooking their victims. They have set up similar decoy websites for Invoice 360, and also for Crystal Office, two popular office programs that have the potential to lure victims via the forum and social media posts. Of course, sending special offers for popular products via spam emails is also a great way to send fresh traffic towards these fake websites, and this method also adds to the “carelessness” factor.
Right now, the cloned websites are still up, albeit AV tools have indexed them in their blacklist, so you’re most likely to get a warning if you try to visit them. Doctor Web has already tried to notify the hosting service of the malicious websites so that they are taken down soon. The team of researchers has been following the particular group since April, and they were the same who saved the day with Bolik infections coming through the VDSC tools. VDSC admins didn’t realize that their website’s download section had been compromised, so there were at least 600 cases of infections before Dr. Web stepped in.
In this latest campaign, the decoy websites are still delivering the software executables so that the victims won’t suspect that anything weird is going on. That said, you’ll still get NordVPN from the fake platform, which is currently supposedly on an amazing “1-year Free” offer. The offer is ending in about nine hours, creating a fake emergency element that drives the victim to move forward without noticing the clear signs of fraud. If you are interested in buying NordVPN or any other software, use a reliable search engine to locate the official domain of the product and don’t trust links shared anywhere else.
NordVPN reached out to us and provided the following comment: Online scammers love to pretend to be trusted companies when trying to fool their victims. Because NordVPN is such a widely trusted online security company, scammers pretend to be us as well. They do this to steal users’ money or infect their PCs with malware. Always double-check information if you have even the slightest suspicion. Also, never give out personal information that has no relation to our services or transfer your money via wiring service. If you have any doubt, always contact NordVPN through one of our official channels.
Have something to say on the above? Write your thoughts in the comments section down below, and help us warn more people by sharing this post through our socials, on Facebook and Twitter.