European Space Agency Confirms Breach of External Servers Containing ‘Unclassified’ Information
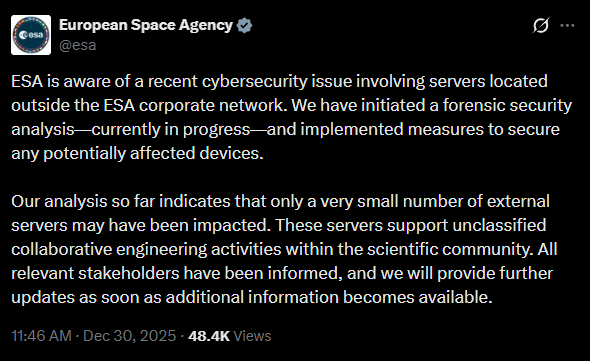
- Breach Confirmed: The ESA has confirmed a cybersecurity incident involving external servers outside its primary corporate network.
- Data Exfiltration: Threat actors claim to have exfiltrated over 200GB of data after gaining access for a week.
- Agency Response: The ESA said the impacted servers supported unclassified collaborative engineering activities.
The European Space Agency (ESA) has acknowledged a recent security breach affecting servers that support collaborative engineering activities. The confirmation followed claims posted on a hacking forum where a threat actor asserted they had gained access to ESA’s servers for a week and managed to steal data.
Scope of the Potential Data Leak
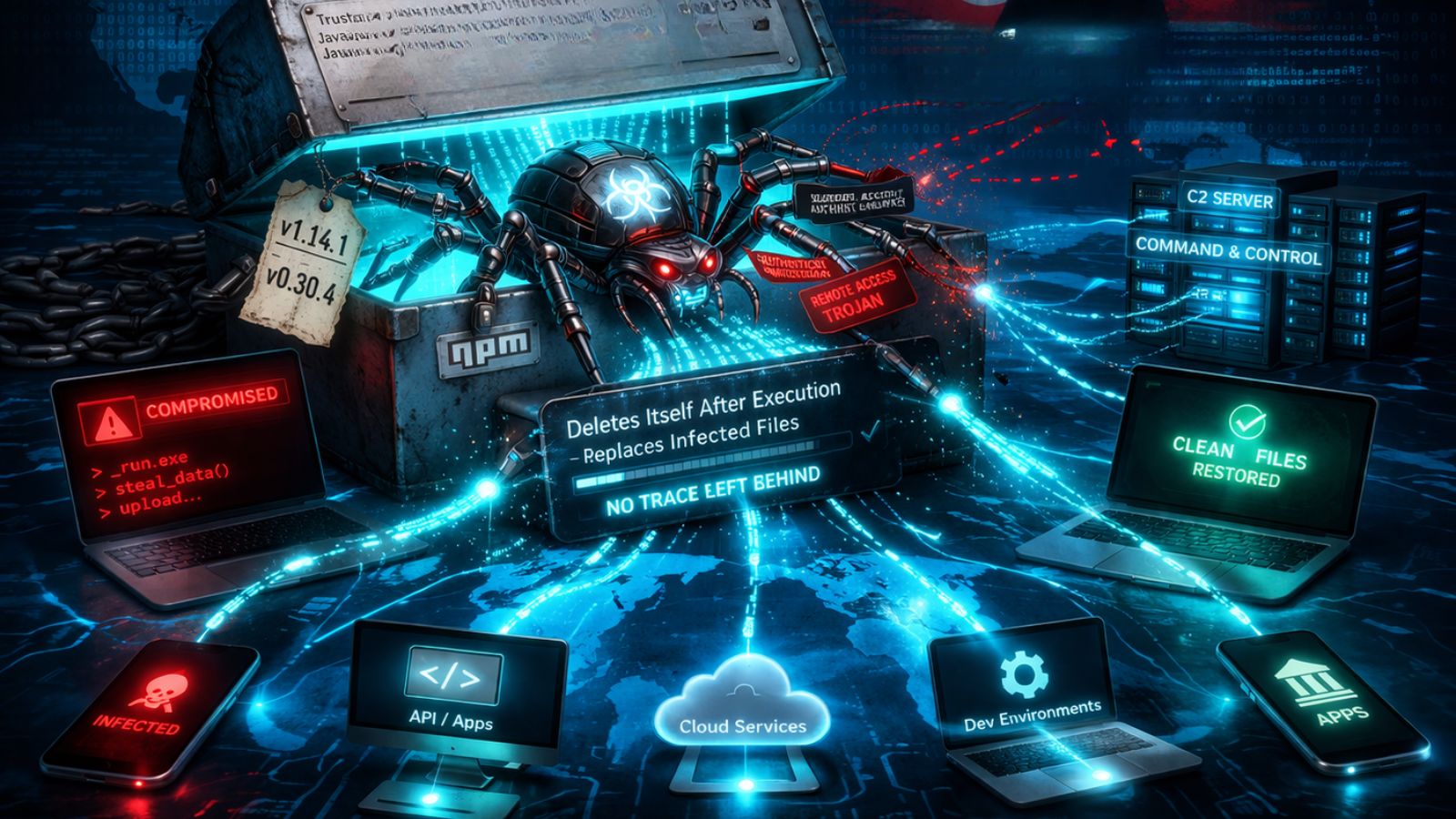
According to the threat actor's claims, the ESA server hack resulted in the theft of more than 200GB of data following unauthorized access to ESA's JIRA and Bitbucket servers. The exfiltrated information allegedly includes:
- Source code,
- CI/CD pipeline configurations,
- API tokens,
- Hardcoded credentials,
- Terraform files,
- Configuration files,
- SQL files,
- Confidential documents.
The attacker provided screenshots as purported evidence of their prolonged access to the agency’s systems.
The agency has stated that the breach was limited to external servers and did not impact its core corporate network.
While ESA has characterized the affected data as "unclassified collaborative engineering activities within the scientific community," the potential exposure of source code and access tokens presents a significant security risk that could facilitate further intrusions if not properly remediated.
Agency Response and Mitigation Efforts
In response to the European Space Agency data breach, the organization has notified all relevant stakeholders and pledged to provide updates as more information becomes available. A comprehensive data leak investigation is currently underway to determine the full scope of the incident and secure any potentially compromised systems.
This incident follows a breach last year where the agency's official web store was compromised to steal customer payment card information.
European diplomatic entities were targeted by a China-linked hacking group in an espionage campaign. In October, the Dark Storm hacktivist gang claimed a DDoS attack on the SpaceX website.