Hackers Breached Ethereum Foundation’s Email Address and Targeted 36,000 Users with Phishing
- Unnamed hackers managed to breach an email address belonging to the Ethereum Foundation.
- As a result, almost 36,000 of the email addresses in their database received malicious messages.
- These contained a link to a phishing website hosting a crypto drainer.
Ethereum Foundation (EF) announced that almost 36,000 addresses on the organization’s mailing list received phishing emails that tried to persuade potential victims to click a link directing them to a crypto drainer that would empty their wallets upon approving the advertised transaction.
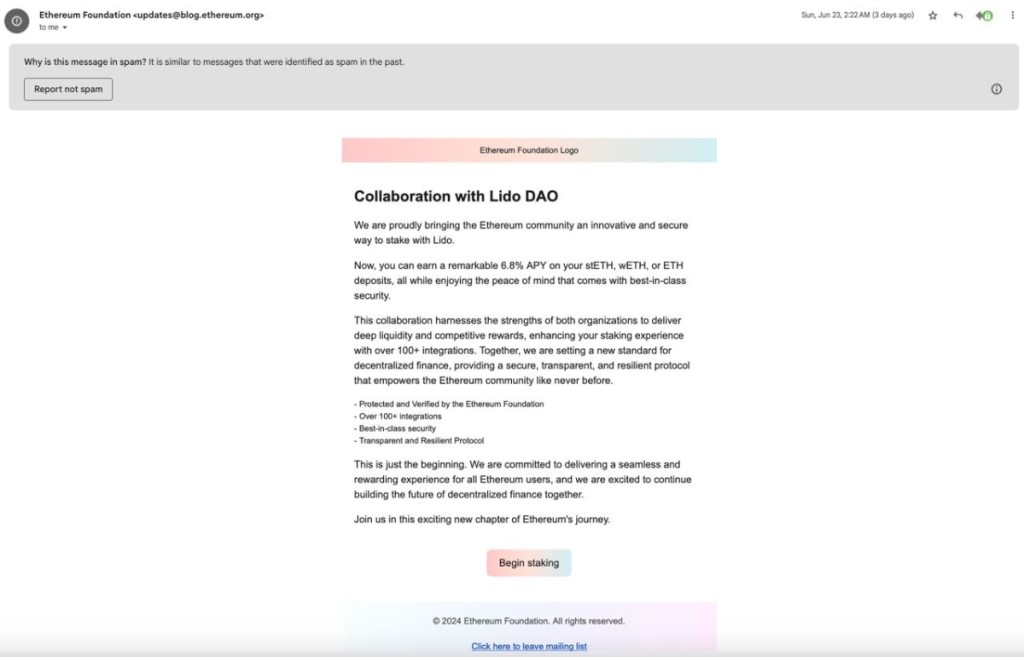
The organization dedicated to supporting Ethereum and related technologies says the phishing email appearing to be sent from ‘[email protected]’ was sent out to 35,794 email addresses on June 23 and claimed that the Foundation was collaborating with LidoDAO to offer a 6.8% return on Ethereum staking.
The 'Begin staking' CTA button in the malicious email’s body directed the user to an aptly crafted fake website designed to convince potential victims that the promotion was real. Yet, a crypto drainer would send the entire amount in their wallets to the attacker if someone decided to connect their wallets on the phishing website and approve the transaction.
The threat actor imported a large email list into the EF mailing list platform, where they apparently managed to access 3,759 email addresses, combining the two for the phishing campaign. However, most turned out to be duplicates, with only 81 of the stolen addresses previously unknown to the attacker.
The EF investigation into the attack analyzed on-chain transactions made to the threat actor and revealed that no victims lost funds between the time the email campaign was sent out and the blocking of the malicious domain.
Luckily, none of the email recipients fell for the trap, and the malicious link has since been blocked by the majority of Web3 wallet providers and Cloudflare.