Estée Lauder Exposed 440 Million Internal Records (no Client Data)
- The New York cosmetics giant has blundered by exposing their sensitive corporate network details online.
- The leaking database contained middleware logs and records, user mails, ports, pathways, and more.
- Estée Lauder was apparently compromised back in 2011, but that was kept internally.
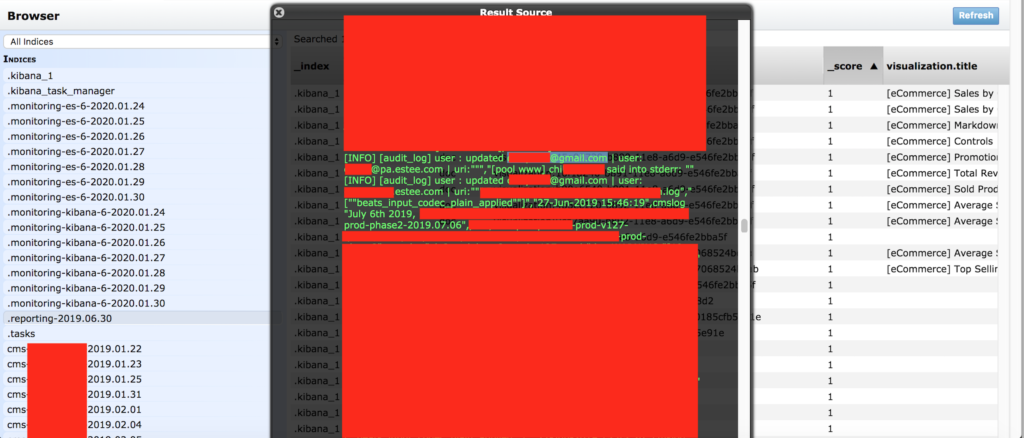
Specialized researcher and “unprotected database” hunter Jeremiah Fowler, has discovered a pretty massive data leak totaling 440336852 records. The discovery of the database was made on January 30, 2019, and the evidence of the owner being Estée Lauder was all over the place. The records contained highly-sensitive corporate information, network data, user details, etc., all in plaintext form and without any password set up to protect them.
Estée Lauder is a New York-based maker of cosmetic products and one of the most successful and renowned firms in the field. They also own another 14 cosmetic brands, 15 fragrance brands, and two that specialize in hair care. So, we’re talking about a major multinational manufacturer and marketer of cosmetics who employs 46000 people, and who measures their revenue in the tens of billions.
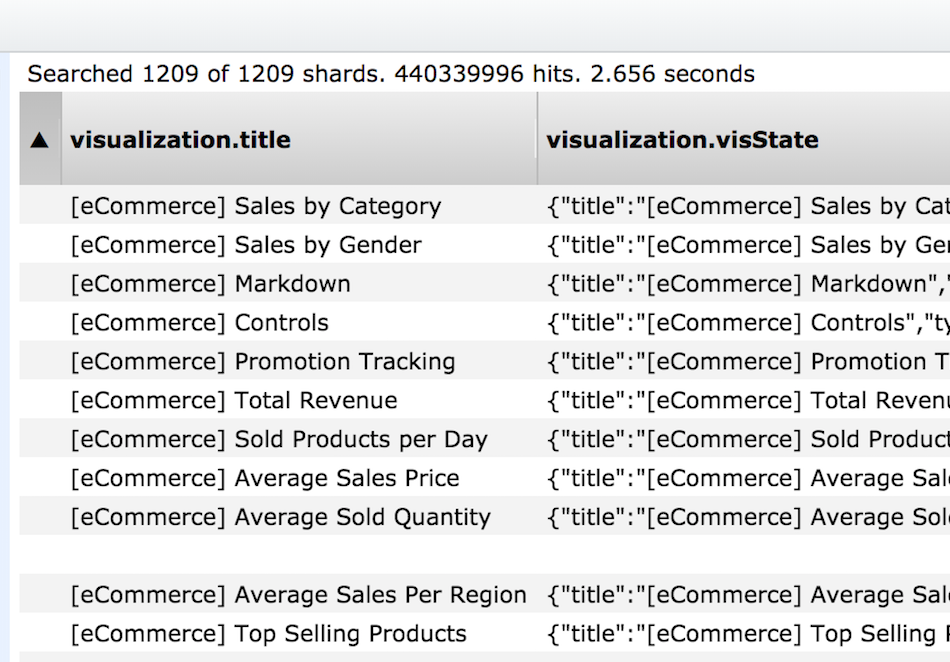
Still, when it comes to securing databases that contain internal data, they somehow managed to fail like many others do every day. Here is what the exposed records contained according to Fowler:
- 440,336,852 logs and records that should not have been publicly exposed online.
- “User” emails in plain text (including internal email addresses from the @estee.com domain)
- Production, Audit, Error, CMS, and Middleware logs were exposed.
- References to reports and other internal documents.
- IP addresses, Ports, Pathways, and storage info that cybercriminals could exploit to access deeper into the network.
Source: Security Discovery
Source: Security Discovery
So, one could say that this leak was pretty catastrophic in terms of the security of the company’s systems. There are details about the middleware that is used for operations internally, so malicious actors could access the API, data management services, or even the authentication systems. Planting malware, or ransomware or a backdoor in Estée Lauder’s computers would be very easy, and may very well be the case already.
The researcher has even found an entry that details a 2011 data breach that has gone undisclosed. Thankfully, it only concerned employees of the company, and they seem to have received the associated notices. Because of the vast amount of the leaked data, the researcher didn’t have the time to fully evaluate it yet, but he affirms that he has found no payment or sensitive employee information in there so far. As for whether anyone has accessed the database, this is entirely unknown. We reckon that Estée Lauder will conduct an in-depth investigation, systems clean-up, and universal credential resets no matter the assurances that their IT department may provide.
In the meantime, Estée Lauder has provided us with the following comment:
"On 30 January 2020, we were made aware that a limited number of non-consumer email addresses from an education platform were temporarily accessible via the internet. This education platform was not consumer-facing, nor did it contain consumer data. We have found no evidence of unauthorized use of the temporarily accessible data. The Estée Lauder Companies takes data privacy and security very seriously. As soon as we became aware, we took immediate action to secure the data and notify appropriate parties."