When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
How Good is Encryption Safety?
When you buy something, be it a toaster or a car, one of the main questions is always how safe it is. Will the toaster burn down your house? Will the car protect you in a crash? It’s right and logical to assess the safety of the tools you use to make your life better, but how often do we do it with certain computer technologies?
Lithium batteries are a good example. Until they started going wrong on certain phones and cheap Chinese hoverboard imports, most people didn’t really understand how dangerous the technology was. This is largely thanks to the stellar safety standards for lithium-ion batteries devised in the West.
When it comes to the safety of our online services, it’s a similar situation. When using Google products, how many people stop to consider how safe that service is? One they are trusting with quite a lot of important information?
We’ve been advocating the use of VPNs like ExpressVPN as a strong way to make the internet a safer place for you. These services use strong encryption to protect your online browsing. However, not every implementation is the same and not all encryption services are equally strong.
Encryption in a Nutshell
We have several articles on TechNadu that explain the overall concept of encryption. However, we need to touch on it a little in this article for it to make sense.
The short and simple explanation of encryption is that it is a way of scrambling information in a systematic way so that only the intended recipient can understand it. Before computers, this was done manually and later with mechanical encryption machines. Encryption has played a key role in all major wars and today is absolutely essential to internet services such as banking and online shopping.
The Power of Modern Algorithms
In the digital realm, there have been several encryption algorithms which were considered powerful enough to meet the rigorous safety standards of the day. DES or the Data Encryption Standard was a powerful encryption algorithm that served as US standard starting in the 70s. Unfortunately, the algorithm was beaten pretty quickly. Since it's encryption keys were only 56-bits long, computer power caught up with it quickly. By 1999 it was trivial to crack.
Today there are two main encryption algorithms that are in widespread use thanks to their high-level of security. AES or Advanced Encryption Standard is used to encode the actual data that flows over the internet. AES key lengths start at 128 bits and 256 is typical. There is no computer system remotely powerful enough to crack AES keys for the foreseeable future.
However, AES is a symmetric algorithm, which means there is only a single key to both encode and decode information. If someone got their hands on that key then it would all be for nothing. That makes it limited for internet use, since how do you get the keys out without being compromised?
The Asymmetric Solution
So asymmetric encryption was developed. Also known as public key cryptography, there are now two keys. One is public and can be used to encrypt information, but only the holder of the other private key can read the info.
RSA, the current standard in secure asymmetric algorithms, is powerful but slow. So it's used for key distribution, getting the AES keys where they need to go.
Both of these encryption standards are effectively impossible to crack. RSA in particular typically has massive keys in the 1024 to 2048 bit range. Even if you linked all the computers in the world, there's not enough time or energy left in the universe to crack these codes.
The Main Threats to Encryption
This doesn't mean modern encryption is completely invulnerable. There are plenty of approaches to breaking the encryption we use to secure our data and browsing. These are some of the most common ones.
Brute Force Cracking
Brute force cracking is the most vanilla and straightforward way to break into encrypted data. It is however completely impractical with current encryption standards. So it's used as the baseline against which other methods are measured. If you work out a way to break the encryption faster than the time a brute force attack would take, then you've essentially compromised it.
Basically, with this method, you use a computer to try and guess every possible combination of allowed characters in the encryption key. Think of the key as a massive combination lock with many possible digits. With AES-128, there are 128 dials with which to fiddle. They don't just use numbers either, but also alphabetical letters in both cases.
Each additional bit you add increases the number of combinations exponentially. So a DES 56-bit key isn't just under half as powerful as an AES 128-bit key, but several orders of magnitude. I've seen some estimated about how long it would take to break these keys, and the fastest supercomputers in the world could crack a DES key in less than five minutes. A 128-bit AES key? Try a trillion years on for size!
Bugs on the Windshield
Instead of literally wasting away to nothing as you wait for the results of a brute force attack that will never come, it makes more sense to find a bug in the actual algorithm that reduces the possibilities from virtually infinite to something more manageable.
For example, most algorithms rely heavily on randomness to ensure that every key is in no way predictable. However, achieving true randomness on a digital computer is pretty hard. If you can figure out any mistakes in the algorithm that produces regular, predictable patterns in the key then you could cut down on the work a lot. Security researchers find these sorts of bugs all the time. In most cases, it might reduce the brute force period from a trillion to "just" a billion years or something equally ridiculous.
Other bugs might have to do with the chain of key creation or some other chink in the algorithm's armor. Criminals and security researchers are always in a race to find these bugs first!
Back Doors
Backdoors are bypasses put into place on purpose. This can be by the people who made the algorithm. Often at the insistence of the government. Backdoors can also be planted without the knowledge of the algorithm maker, although this is only in theory.
Sometimes a bug can be used as a back door, although it was not intentionally put there.
Backdoors are one of the main reasons you should prefer Open Source encryption algorithms since these can be checked by the community for backdoors.
Key Theft
The easiest way to unlock encrypted data is by already having the keys in your possession. There have been plenty of cases where a server or database is hacked and decryption keys are found in plain text format. Secure key storage is incredibly important. Which is why trusted key authorities are used these days to generate and distribute the keys that secure websites. They specialize in keeping keys secure. Nonetheless, site owners have a responsibility to keep their keys secure.
Leaps in Processing Power
With the type of computers we have today, it doesn't seem that there will ever be a system fast enough to do the job in a practical time span.
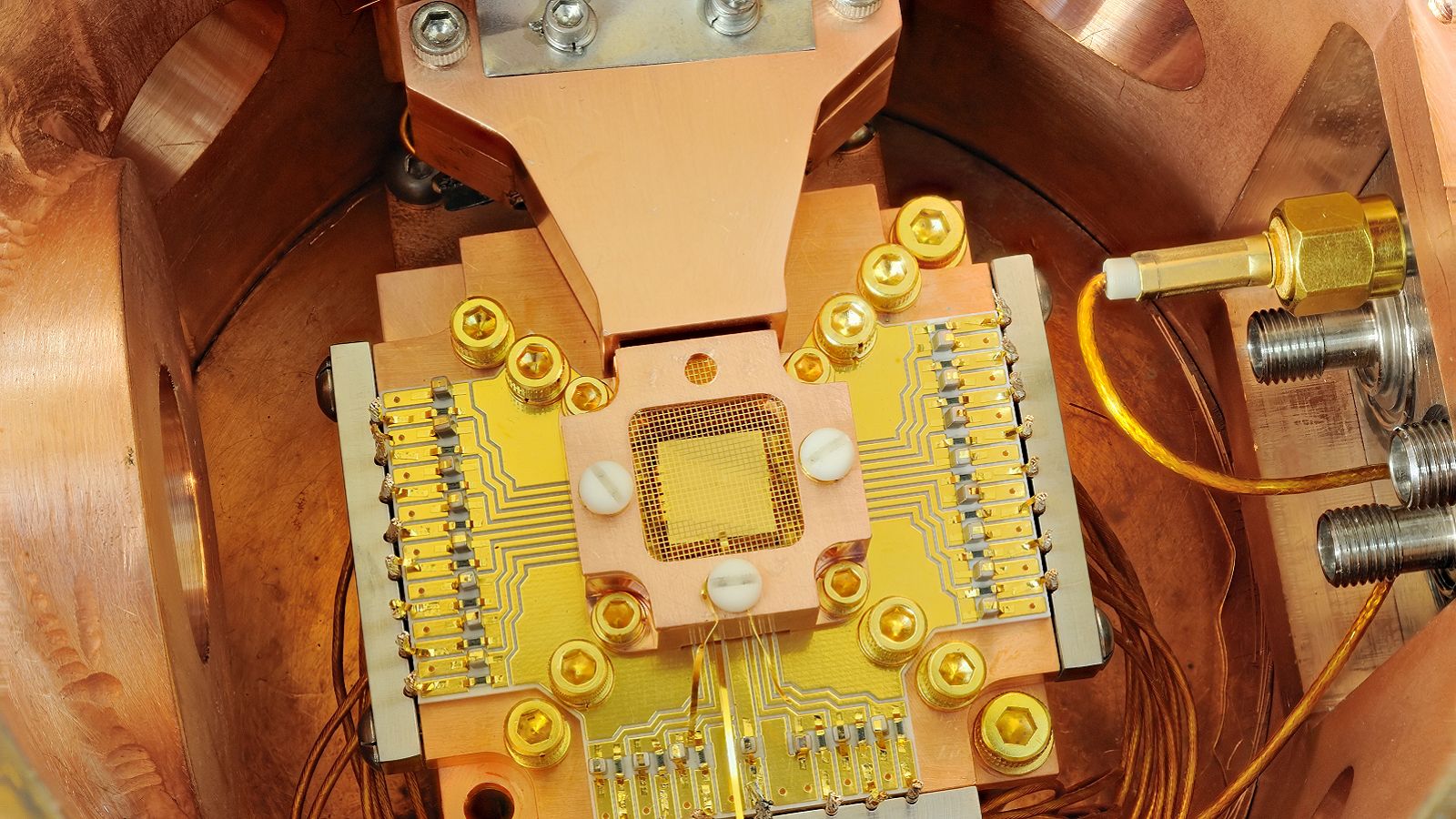
However, there do seem to be a few radical ideas in computing that could make the cracking of something like AES less than an impossibility. The use of quantum-, optical- and DNA- computers could one day surmount this seemingly impossible challenge. Of the three, quantum computing shows the most promise. If we every perfect these technique, the current best encryption could become as trivial as DES to break.
Forced Decryption
This is a particularly nasty one and the subject of much debate. In several countries in the world, you can be compelled to provide your encryption password so that the contents of a device like a phone can be searched. Even in the US, with its 5th Amendment, several cases have seen rulings where forced decryption is not seen as a violation.
If you refuse to provide the encryption password, you may be detained or be charged with other crimes related to interfering with the course of justice.
Security-savvy users who don't use biometrics can claim that they don't remember their password, but if the court doesn't buy it you'll have to choose if the contents of your encrypted data are worse than sitting in jail or not.
Safety Blankets
Encryption is without a doubt one of the most powerful, safe and sophisticated ways to protect your information and actives on the internet. So, in general, you have nothing to worry about when it comes to the safety of using encryption.
That doesn't mean things can never go wrong! There's not much you can do about an algorithm being cracked or a server being hacked. You can try to evaluate the encryption that's being offered to you. Here are some questions you should ask when considering a service that uses encryption:
- Is this encryption algorithm trusted and recognized?
- Has it been compromised?
- Has it been implemented with a long enough key?
- Where applicable, are the keys stored in a safe way?
In most cases, the answers to these questions can be determined by some quick Googling. It's mostly an issue that affects small, lesser-known services. Not the big dogs.
To answer the original question in this article - yes, encryption is very safe. Certainly a million times safer than things would be without it.