Defunct Marketing Company Leaked the Sensitive Data of Over 300,000 People
- A now shut American marketing firm has exposed 32GB of sensitive data online.
- The incident is the result of leaving an Amazon S3 bucket unprotected, while it still remains open to access.
- The exposed details include full names, email addresses, physical addresses, phone numbers, and hashed passwords.
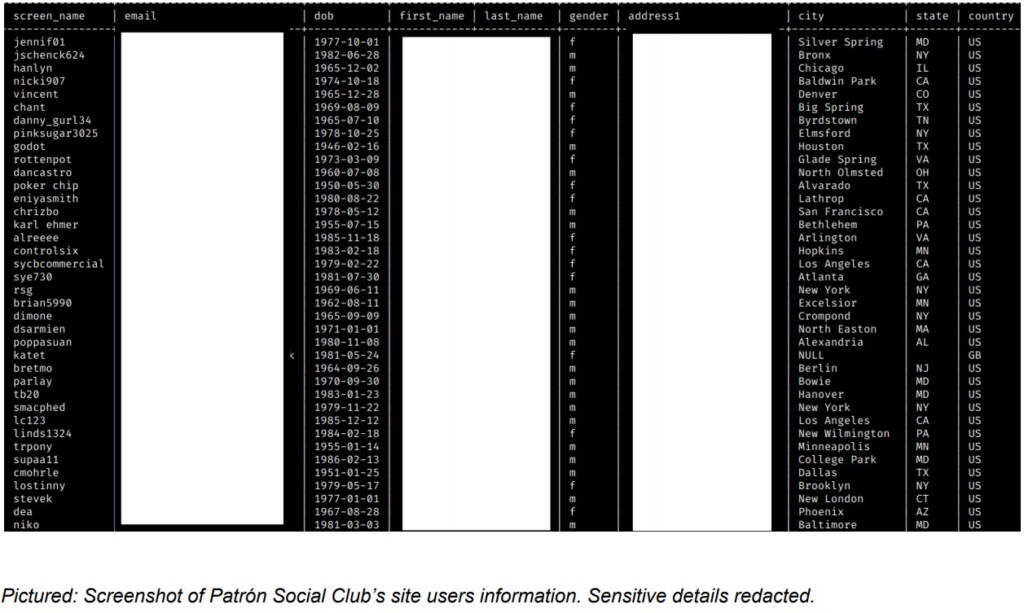
‘Reindeer,’ a New York-based digital media advertising and marketing company that is now out of business has left an Amazon S3 bucket exposed to public access resulting in the irreversible leak of 50,000 files that account for a total of 32 GB of size. The exposure affects roughly 306,000 people, who were customers of various Reindeer clients such as the ‘Patrón Tequila’ alcoholic beverage brand and the ‘Jack Wills’ UK clothing brand. The discovery of the bucket comes from the security team at WizCase, who shared their finding exclusively with TechNadu.
The information contained in the exposed bucket depends on the client but generally includes the following:
- Full name
- Email address
- Physical address
- Date of birth
- Phone number
- Hashed passwords
- Facebook IDs
People from the United States, Canada, and Great Britain account for almost 280,000 of the user entries in the database, so the majority is from these three countries. In total, there are people from 35 countries in the bucket. The information was collected between May 2, 2007, and February 6, 2012, so it’s pretty outdated. However, most of this data cannot be reset or changed, so it’s still exploitable by scammers, phishing actors, and malicious individuals in general.
When it comes to the passwords, Reindeer used the now-obsolete SHA256 algorithm to convert them into a 64-character string and also salted the hashes. This means that even if the information falls into the wrong hands, it’ll be a tedious process to crack the encryption and derive cleartext passwords. Due to the age of the algorithm, though, it’s practically possible. As such, if you remember having subscribed on Patrón Tequila or JackWills online platforms, you should reset your passwords immediately.
The Wizcase team attempted to contact Reindeer to inform them about the configuration problem, but since the company went defunct years ago, they were out of reach. They then contacted Amazon and also US Cert, but at the time of writing this, the database remains online and accessible by anyone with a valid URL.
This is yet another example of how the risks of having your details scraped/collected by a marketing firm can persist for a very long time, even after several years since that company has shut its doors. In this case, we see an entity still holding a set of data that should have been deleted from all its systems long ago, let alone its cloud environment. Unfortunately for hundreds of thousands of people, this never happened.