The ‘DarkSide’ Operators Respond to the Release of a Decryptor
- BitDefender’s DarkSide decryptor hasn’t done much damage to the RaaS program, according to the operators.
- The group has given new incentives to join the platform and saw a 20% rise in membership in just two days.
- BitDefender could have chosen a better timing for the decryptor’s release, as they now saved only three firms.
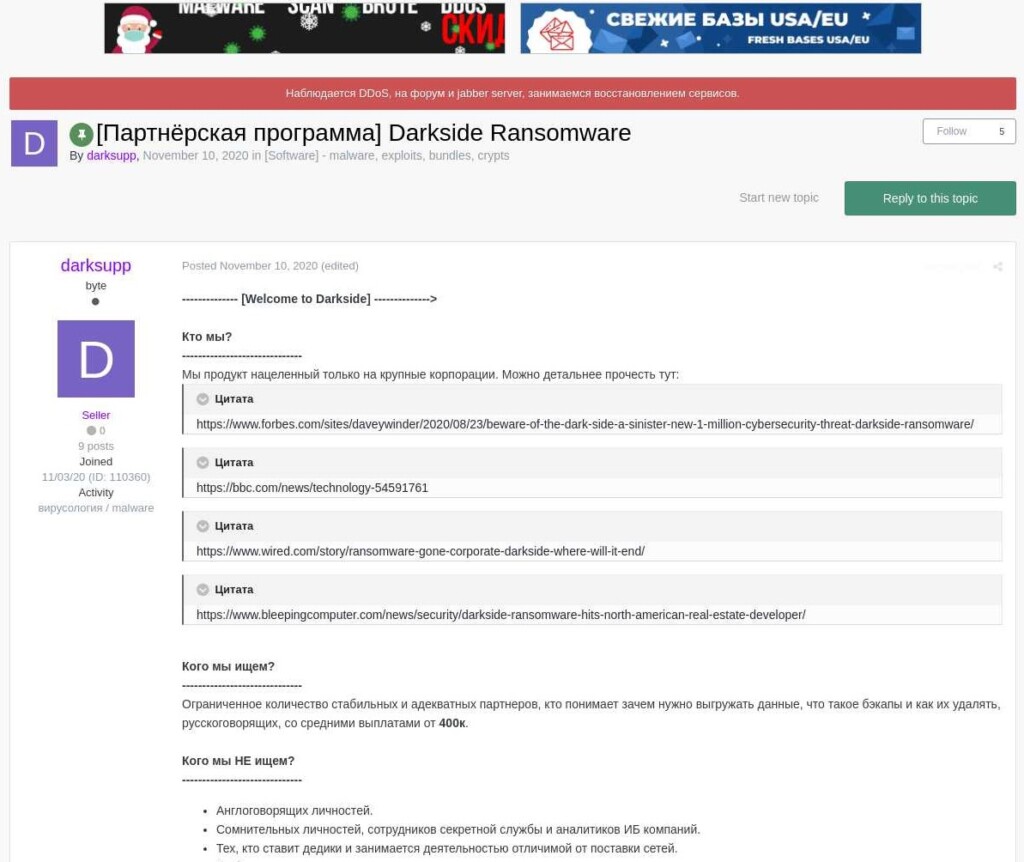
Last week, BitDefender released a working decryptor for the DarkSide group’s ransomware, giving victims a way to unlock their files for free. Being a new and “hopeful” RaaS (ransomware as a service), DarkSide had to provide an official response to the situation, or the underground cyber-crime community could lose faith and not use the platform anymore.
Darkweb intelligence firm KELA tipped us about a relevant Q&A that was released by ‘DarkSide’ over the weekend, giving some explanations about the situation - and most importantly, providing some unexpected assurances.
First of all, the ransomware actors do not believe that the decryptor’s release will affect subsequent payments because all new targets will be victimized using unique keys, and BitDefender’s tool won’t be able to help them. Also, the chances of having an update on the current decryptor that would enable it to unlock subsequent infections are slim. As the announcement explains, the ransomware authors don’t use pseudo-random number generators but the FIPS 140-2 cryptographic standard, which is a U.S.-government-level crypting module approval system.
All that said, only existing infections are affected by BitDefender’s decryptor, and DarkSide claims that the number of targets who can benefit from it is just “four.” One of them already paid the ransom, so in reality, it’s just three companies. For these three, the directly affected partners will be fully compensated from the DarkSide’s deposit in the next 10 days.
This is a move to help establish a higher level of trust between the operators of the RaaS program and the partners. In this context, the operators declared a plan to increase the deposit amount in the following two months to cover for any potential problems in the future. In addition to all of the above, existing partners will get to keep the full amounts of any paid ransoms for the next three weeks, while new registrants will enjoy a cut of 90% for the first two weeks.
Finally, DarkSide mocks BitDefender for choosing a very bad time to release the decryptor as the New Year holidays are when everyone is taking a break, including ransomware actors. Thus, there were no significant attacks and no opportunities to help high-profile victims. In fact, DarkSide claims that the publicity from the release of the decryptor actually brought many new partners aboard (20% increase) in just 48 hours, further strengthening the platform.