CyberStrikeAI Deployed in Over 600 FortiGate Attacks Targeting 55 Countries
- Massive Scale: The open-source CyberStrikeAI framework orchestrated over 600 unauthorized network intrusions spanning 55 countries.
- Targeted Infrastructure: Threat actors specifically compromised FortiGate appliances utilizing 21 IP addresses linked to China-based operational infrastructure.
- Automated Exploitation: This campaign demonstrates a critical evolution in automated threat deployment and the bypassing of perimeter defenses.
Threat actors used CyberStrikeAI, an open-source AI testing framework, to breach the over 600 distinct enterprise network environments across 55 countries that AWS reported last month. Security analysts have identified that the operation relies heavily on 21 specific IP addresses and the platform is hosted in regions such as China, Singapore, and Hong Kong, with additional related servers in the U.S., Japan, and Switzerland.
Analyzing AI-Driven FortiGate Breaches
A Team Cymru report said that CyberStrikeAI is built in Go and integrates more than 100+ security tools, an orchestration engine, role-based testing, a skills system, and comprehensive lifecycle management capabilities.
The report found that the offensive security tool (OST) was created by a China-based developer who may have “some ties to the Chinese government,” including Chinese private sector firms with known ties to the nation’s Ministry of State Security (MSS).
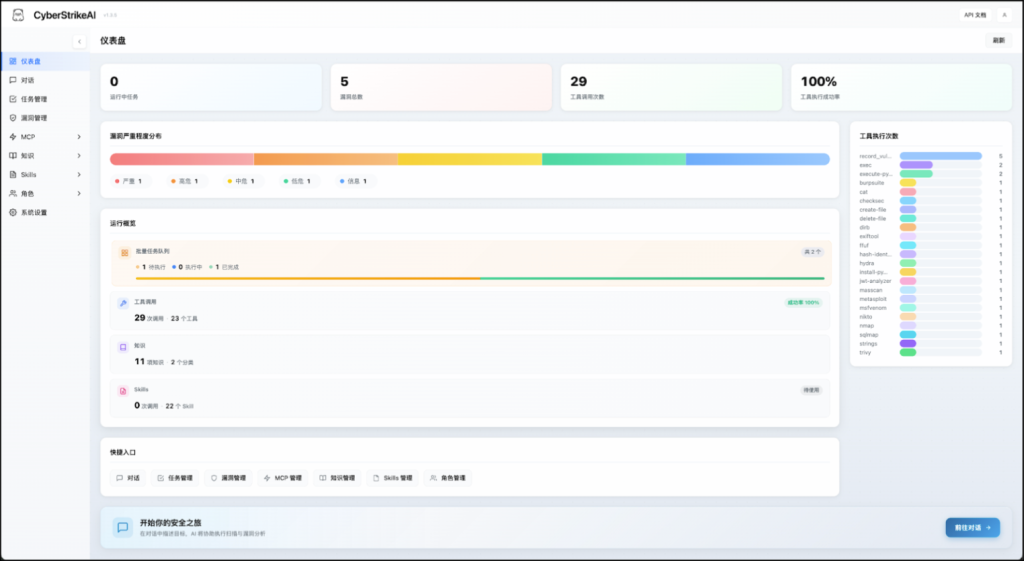
CyberStrikeAI even provides a user dashboard that details the platform's core features and current state. The use of an AI engine enables attackers to adapt their intrusion techniques dynamically, testing multiple exploit variants against a target until a successful breach is achieved.
The CyberStrikeAI developer’s GitHub profile suggests interest in exploitation activity, such as an invisible digital watermark tool and tools to detect privilege escalation vulnerabilities.
Escalating Global Cybersecurity Threats
As open-source AI tools become more accessible, threat actors seamlessly integrate them into their offensive operations to increase attack velocity and scale. Network administrators must immediately apply all critical firmware patches to FortiGate appliances.
Last month, Amazon Integrated Security threat intelligence revealed a large-scale Russian-speaking, AI-assisted hacking campaign targeting over 600 FortiGate firewalls across more than 55 countries between January and February 2026, including deployments in South Asia, Latin America, and Northern Europe.
Other reports include Google revealing that state-backed hackers use Gemini AI for cyberespionage and hackers using AI-generated malware to exploit the React2Shell flaw.