Counter-Strike 1.6 RCE Vulnerabilities Infect Players’ PCs with Trojan
- Counter-Strike 1.6 players are becoming part of a vast botnet network, and Valve doesn’t care about the fact.
- An antivirus product team has discovered the problem and took action to mitigate the risks for everyone.
- The infection Trojan has been rebuffed, but the actors may try again with a different set of domains.
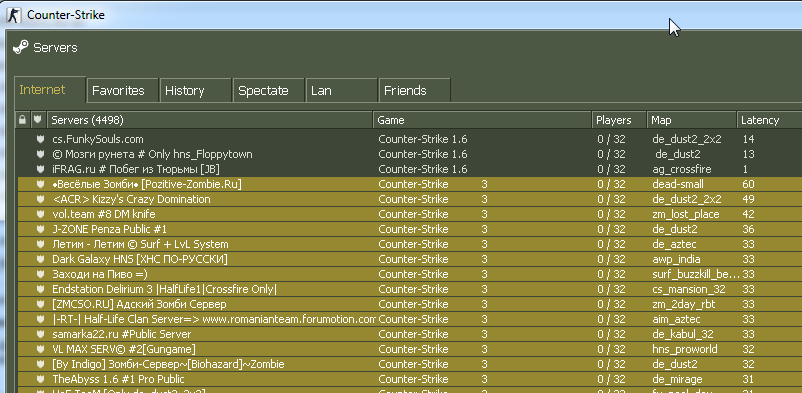
A study by the Dr. Web Antivirus team shows that the old and now obsolete Counter-Strike first-person PC game poses a severe risk to those who keep playing it. More specifically, version 1.6, which is over 19 years old now, is still played by an average of 20000 players at any given moment, supported by a server network of over 5000. The problem is that about 1950 of these servers are malicious, and have been set up with the sole purpose of hacking the PCs of their clients, by using a Trojan.
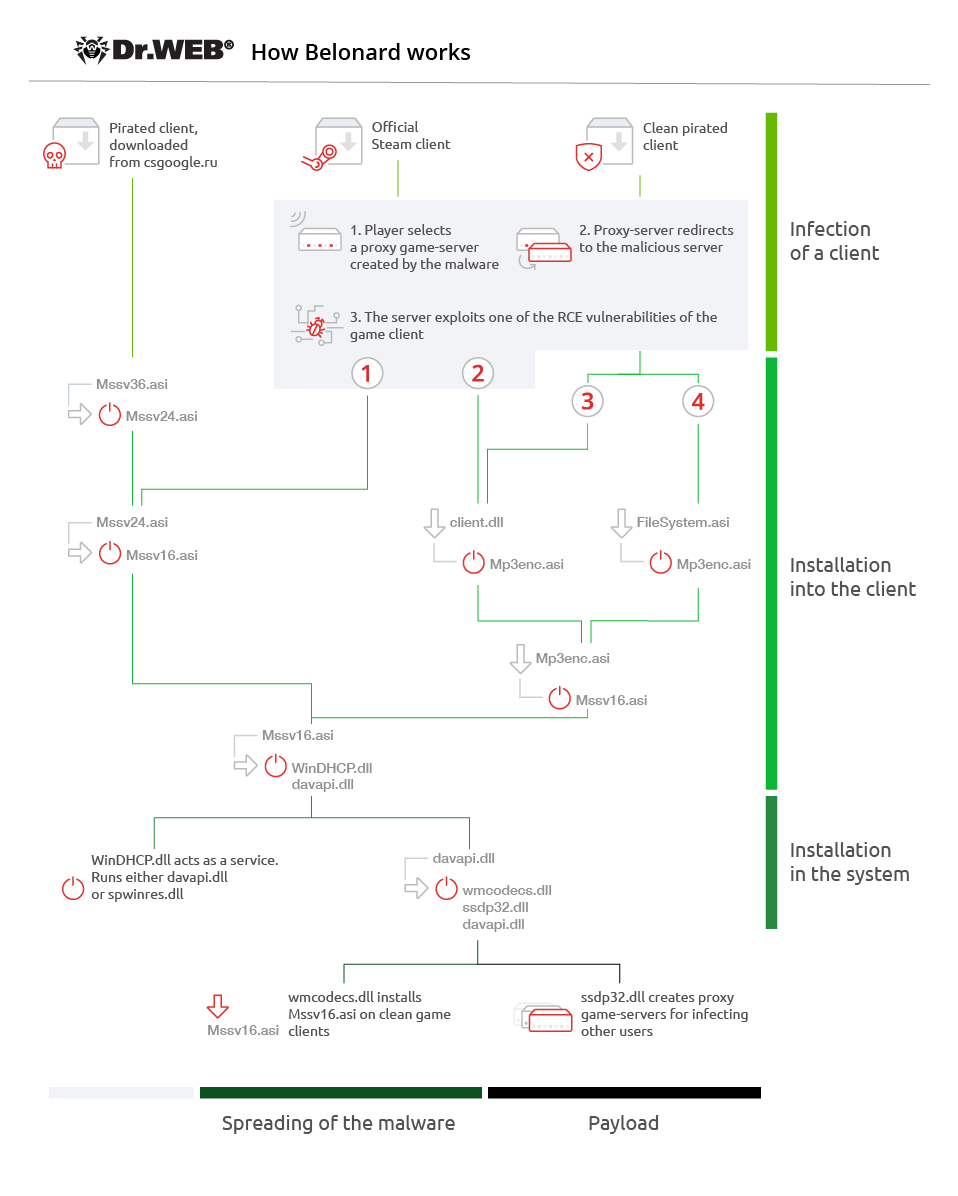
The developers of the “Trojan.Belonard” have had all the time and comfort in the world to seamlessly develop a versatile malicious tool, as Valve, the developer of CS, is no longer maintaining it and neither do they pay any real attention to the security reports that concern it. The Trojan infects the player’s PC by taking advantage of multiple RCE (Remote Code Execution) vulnerabilities that exist in the product, while some of the clients that are available out there are even pre-infected, for even higher levels of Trojan persistence.
source: drweb.com
Once one or more of the malicious binaries are downloaded from the C2 server onto the infected PC, the Trojan activates self-protection, and finally downloads a botnet. All of the communication data between the Trojan and its control server is encrypted, while a clever registration of more proxy game servers with the Stream API is also taking place to ensure that the infection propagates.
source: drweb.com
Dr. Web’s analysts have taken steps to protect the CS players from connecting to the malicious servers by contacting a Russian domain name registrar company and delegating those that were used by the malware developer. This means that right now, the malicious activity has been disrupted, and the botnet growth has been put to a halt.
While this has helped render the classic CS gaming scene safe again, it will almost certainly not be the end of the story if Valve doesn’t fix the RCE flaws that leave the door open to malicious actors. As much as old the particular game may be, there’s still a community of players who enjoy it, and unethical hackers are taking advantage of this combination of facts, based on Valve’s indifference.
Are you one of those tenacious old-school first-person players? Let us know why you still play SC 1.6 in the comments section underneath, and share this story through our socials, on Facebook and Twitter.