Cosmetics Brand ‘Avon’ Has Leaked 7GB of Data Online
- ‘Avon’ has left a server completely unprotected for at least nine days, exposing sensitive data.
- The exposure affects mainly the sales representatives of the company, and also its security.
- Access to the server could have been abused by hackers, causing damage to the company.
‘Avon’ has fallen in the pothole of server misconfigurations. It is the fourteenth-largest beauty products company globally, and the second-largest direct-selling enterprise (6.4 million representatives).
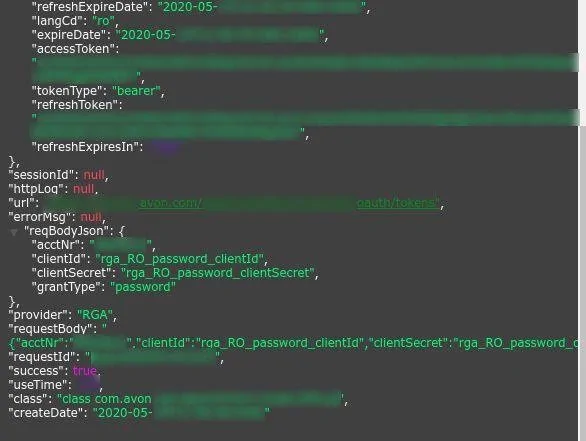
Security researcher Anurag Sen has discovered an unprotected server belonging to “Avon.com” and immediately informed the company. The server contained 7GB of data, including API logs and internal OAuth tokens - about 40,000 of them.
It means that the breach exposed all production server data, including the OAuth tokens representatives used to sign-in on the company’s online platform. So, essentially, anyone with a web browser could take over random Avon seller accounts.
Source: Security Detectives Blog
But this is not the end of the problems or the exploitation potential. The server also contained internal logs that could be used in a way that would harm Avon’s IT infrastructure. For example, planting cryptocurrency miners onto the server would be possible, and infecting it with data-stealing malware or data-locking ransomware shouldn’t be much harder either.
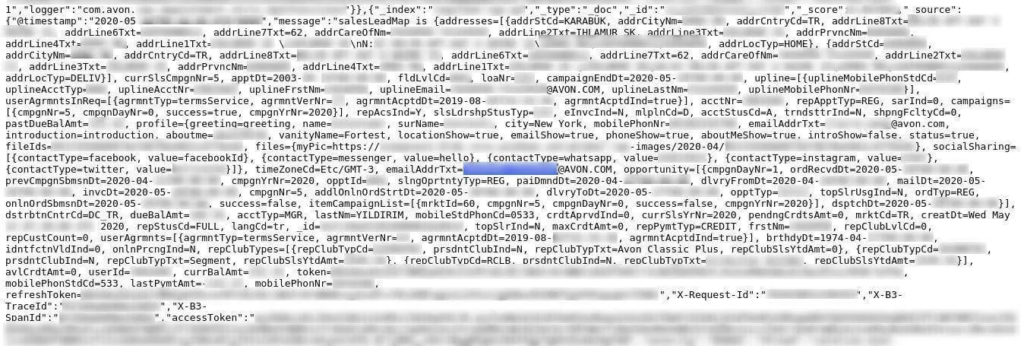
Besides that, the following details were found in the 19 million records that were stored on the server:
- Full names
- Phone numbers
- Dates of birth
- Email addresses
- Physical addresses
- GPS coordinates
- Last payment amounts
- Names of company employees (suspected but not confirmed)
- Administrator user emails
Source: Security Detectives Blog
Considering the above, the exposed sales representatives are now running the risk of identity fraud, scamming, and phishing. There are no indications that Avon clients are part of this data leak, though, which is the bright side of the story.
As for the technical exposure aspect, this is solely Avon’s problem, and it’s admittedly a pretty big one. Hackers could have brought the firm’s operations down, and in fact, there are indications that something like that may have taken place.
Based on the indexing details, Avon’s server first appeared online on June 3, 2020. The researchers contacted the company on June 12, 2020, and access to the system was closed almost right after their communication.
On June 9, 2020, however, Avon published a statement where they described a cyber incident of some form, which interrupted some of its systems and partially affected operations. The server’s discovery may be connected to the subject of that statement, and it is also possible that Avon hadn’t realized the source of their problems until the researchers reported it. Of course, these are just assumptions, but the pieces fit.
Read More:
- Owners of Unprotected MongoDB Databases Now Facing Unusual Extortion
- “Aspire News” Has Leaked 4,000 Recordings of Domestic Violence Victims
- ‘Lollicupstore’ Exposed Customer Data Online via Unprotected Database