CISA Warns About Video Camera SDK Vulnerability Affecting Millions of Devices
- There’s a flaw in ThroughTek P2P SDK that could let someone spy on the video feeds of millions of cameras.
- The vulnerability has been addressed via an update since last summer, but many clients still run an old version.
- CISA has published an alert to raise awareness on this important cybersecurity issue.
CISA (Cybersecurity and Infrastructure Security Agency) has published a new advisory warning about a novel flaw in the ThroughTek P2P SDK versions 3.1.5 and older, which could permit unauthorized access to cleartext video and audio feeds through millions of affected cameras. The flaw in question is tracked as “CVE-2021-32934” and has a severity score of 9.1 in the CVSS v3 evaluation standard. It is also exploitable remotely, and it doesn’t require much complexity to do so.
According to the advisory, the following products are affected by the flaw:
- Versions 3.1.5 and prior.
- SDK versions with nossl tag.
- Device firmware that does not use AuthKey for IOTC connection.
- Device firmware using the AVAPI module without enabling DTLS mechanism.
- Device firmware using P2PTunnel or RDT module.
The proposed mitigations are the following:
- If SDK is Version 3.1.10 and above, enable authkey and DTLS.
- If SDK is any version prior to 3.1.10, upgrade library to v3.3.1.0 or v3.4.2.0 and enable authkey/DTLS.
CISA also suggests that users should minimize network exposure for all control system devices and to locate control system networks and remote devices behind firewalls and isolate them from the business network. If remote access is required and there’s no other option, reliable VPNs should be deployed for secure access and also the encryption of the data that comes and goes.
ThroughTek has clarified that this issue has been addressed in SDK version 3.3 and onwards, which was released last summer. Even though a full year has passed since then, it appears there is still a noteworthy number of customers who have either ignored the new version or didn’t implement it correctly. These customers correspond to several millions of devices, so the impact of this flaw is pretty big.
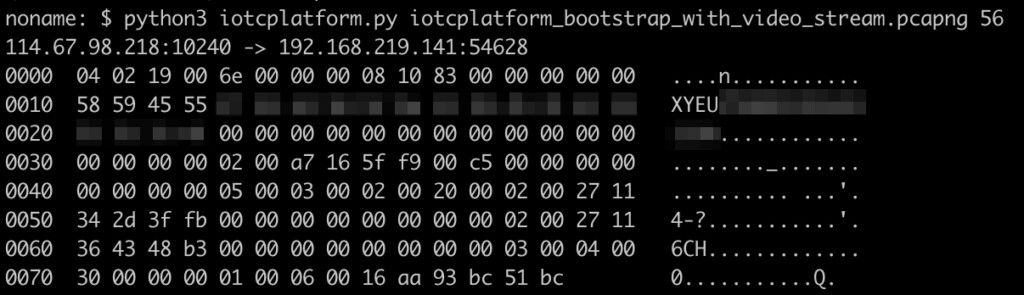
As for who discovered the vulnerability, that would be researchers at ‘Nozomi Networks Labs.’ They discovered that the video and audio feed passed through ThroughTek’s P2P platform lacks a secure key exchange and relies instead on an obfuscation scheme based on a fixed key. They then created a proof-of-concept script that deobfuscates on-the-fly packets from the sniffed network traffic and disclosed the bug to ThroughTek in March 2021.