Chinese Actor APT41 Exploiting Vulnerabilities in Lengthy Global Campaign
- APT41 has engaged in one of the most long-lasting campaigns ever to have been recorded.
- The Chinese cyber-espionage actors used multiple published vulnerabilities to compromise unpatched systems.
- In many cases, it only took them a couple of days to use a published proof of concept exploit.
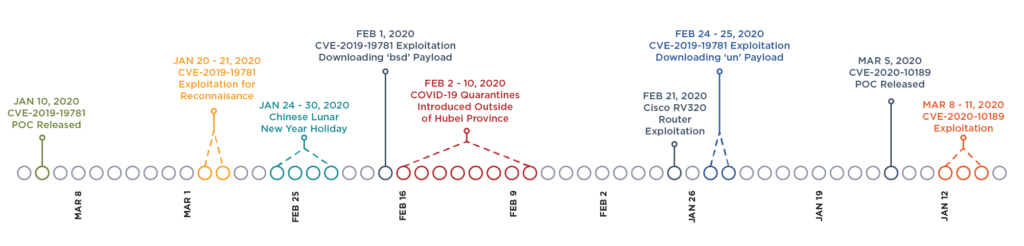
FireEye researchers have been monitoring the activity of the Chinese hacking group APT41. They report that they are seeing one of the lengthiest and most persistent campaigns ever to have stemmed from them. APT41 started their recent activity on January 20, 2020, and cycled through a total of four vulnerabilities, exploiting them individually and subsequently within specific periods. As for the target countries, the list includes Australia, Canada, Denmark, Finland, France, India, Italy, Japan, Malaysia, Mexico, Philippines, Poland, Qatar, Saudi Arabia, Singapore, Sweden, Switzerland, UAE, UK, and the USA.
Here’s a summary of the timeline of the attacks:
- January 20 – 21: Exploiting CVE-2019-19781. This is a flaw in the Citrix Application Delivery Controller and Citrix Gateway devices, which became known on December 17, 2019. The PoC for this vulnerability was released on January 10, 2020.
- February 1: Exploiting CVE-2019-19781. This time, the group wasn’t limited to reconnaissance activities. They worked with actual payloads this time, planting backdoors on the compromised systems, and executed exploitation commands.
- February 21: Exploiting CVE-2019-1653 and CVE-2019-1652. These two flaws enable the remote code execution against Cisco Routers RV320 and RV325. The group used a Metasploit module that combines the two vulnerabilities to a single exploit.
- February 24 – 25: Exploiting CVE-2019-19781. Last time, the group used the ‘bsd’ payload. This time, they used FTP-fetching to download the ‘un’ payload.
- March 8 – 11: Exploiting CVE-2020-10189. This is a zero-day vulnerability in Zoho ManageEngine, for which a PoC was released on March 5, 2020. The group used two variations of payload deployment and generally had a successful run. In both cases, they used the Cobalt Strike BEACON loader.
Source: FireEye
What becomes evident from the above is that APT41 is using publicly available PoC (proof of concept) code to launch their attacks, and it only takes them a couple of days to engage in this activity. It means that system administrators have a limited time to update, proving how crucial it is to upgrade your software immediately when a PoC is made public.
In all of the above cases, APT41 managed to compromise vulnerable systems that didn’t get to be updated. Apart from that, it is noteworthy that APT41 is now making use of “off the shelf” malware like Cobalt Strike and Metepreter. It proves that these tools are handy and versatile nowadays, as groups like APT41 are skilled enough to develop and use their own sophisticated tools.