Browser Extension Developers Turn to Code Injection for Monetization
- A significant number of browser extensions rely on code injection to monetize their add-ons.
- Most of these extensions are poorly maintained or lack support, so they turn to shady firms.
- One of them is a proxying platform that anonymizes traffic by bouncing it to residential computers.
Most browser extensions are free, so the provision of their services has to be supported somehow, especially when their userbases count tens or even hundreds of thousands of people. Incorporating ads is one way, but according to extension developers who tried it, ads bring a lot of whining in the community and don’t generate much money in return anyway.
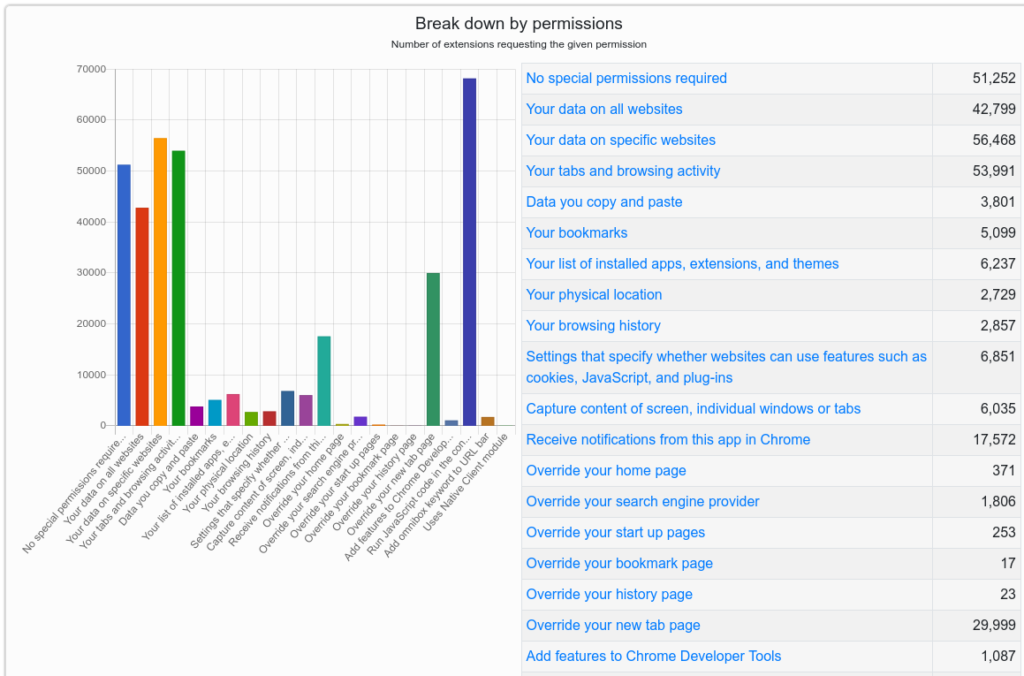
The other way to monetize extensions (which, according to a KrebsOnSecurity report, is very popular today) is adding code that turns people’s browsers into proxies.
One of the most notable examples of that is a Singapore-based company named "Infatica," which rents out access to browsers so that its clients can hide their true IPs. It’s not a VPN in the sense of encrypting the traffic, but more like a basic bouncer that adds a weak layer of anonymization that’s enough in most cases.
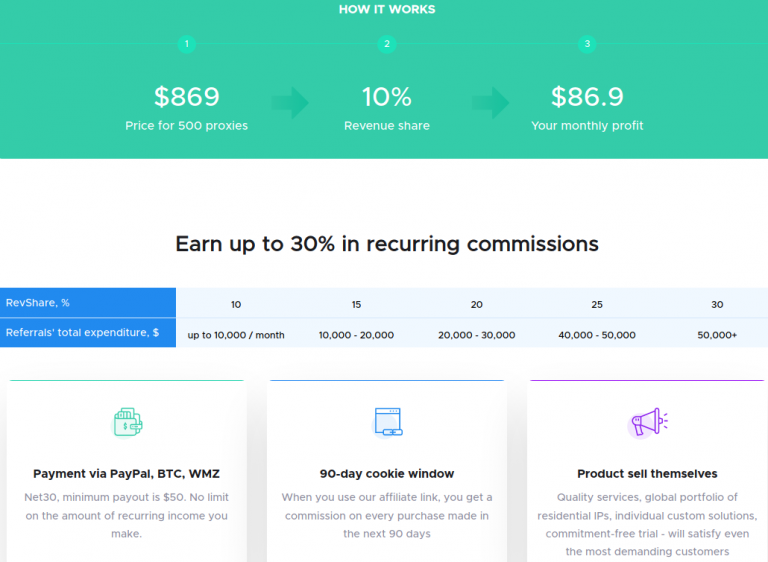
Infatica pays extension developers with over 50,000 users to incorporate its proxy code in their products, and the rate ranges between $15 and $45 per month per 1,000 users. Infatica then sells its anonymization services to its customers for varying rates, depending on the traffic volumes.
So, you could be using Infatica’s code through an extension that doesn’t mention that little detail, indirectly offering your services to the firm and getting the extension’s functionality in return. While the code won’t access sensitive information like cookies and stored passwords or even the user’s screen, having your browser used as a proxy for going to risky websites isn’t ideal.
An epidermic investigation by Brian Krebs has revealed that Infatica’s code is present in at least 36 extensions, some of which count over 100,000 users. One of them is "Video Downloader Plus," which has 1.4 million monthly users.
In its privacy policy, the particular extension mentions the collection of personal and non-personal identification information, and the sharing of data with advertisers, sponsors, suppliers, partners, and other third parties, but there’s no clear mention of proxying functions.
If we had to advise you one thing about browser extensions, that would be to keep their number at the minimum possible. Stick to using only those that you absolutely need, check the user reviews on the store, read the privacy policy, and finally ensure that the particular extension is actively maintained and not abandoned.